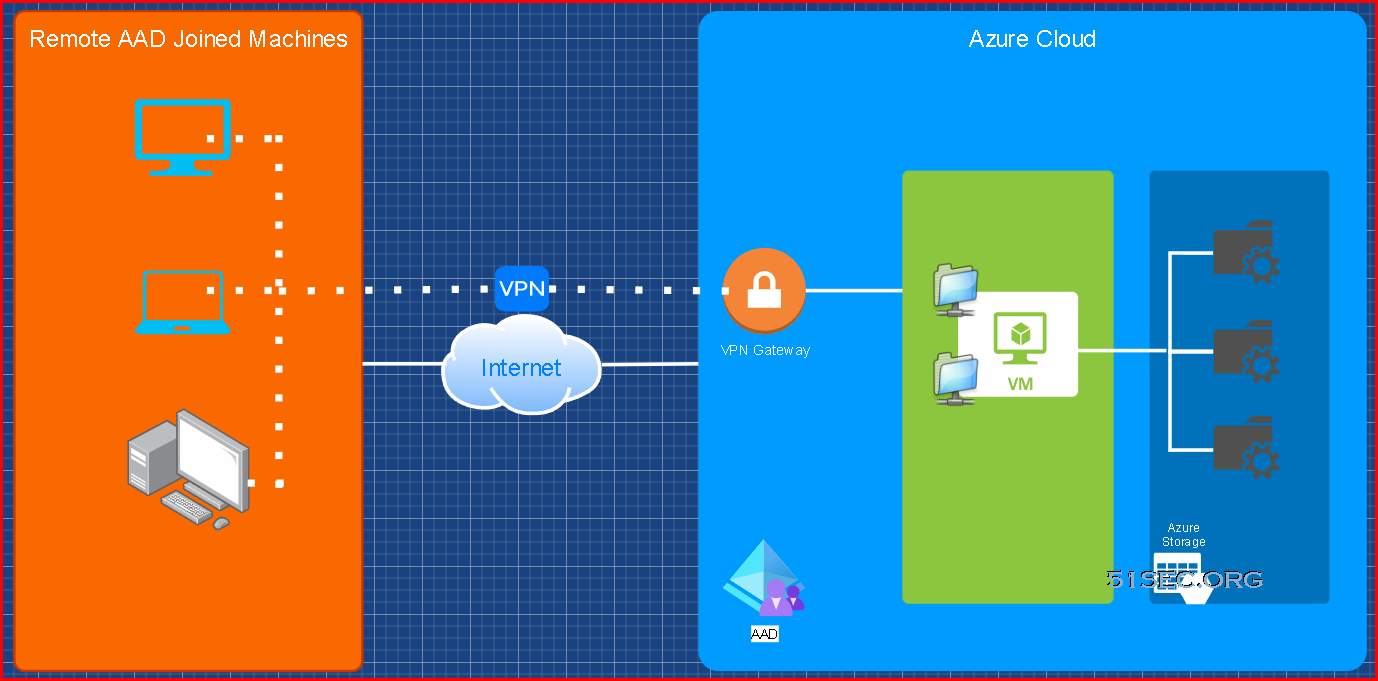
This post is to summarize the steps to have your remote AAD joined Windows machine to access Azure storage file shares with proper access control.
Diagram
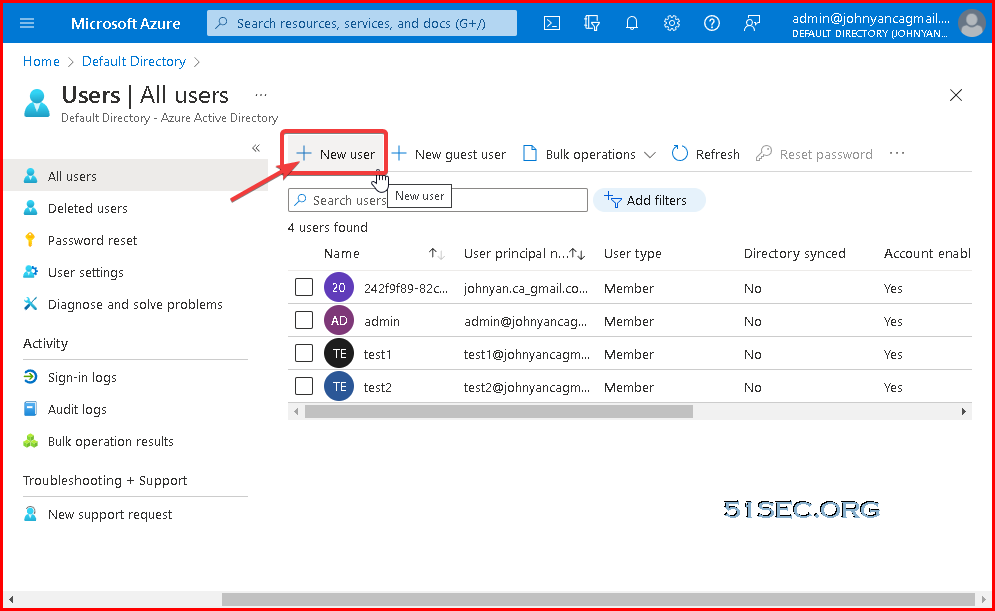
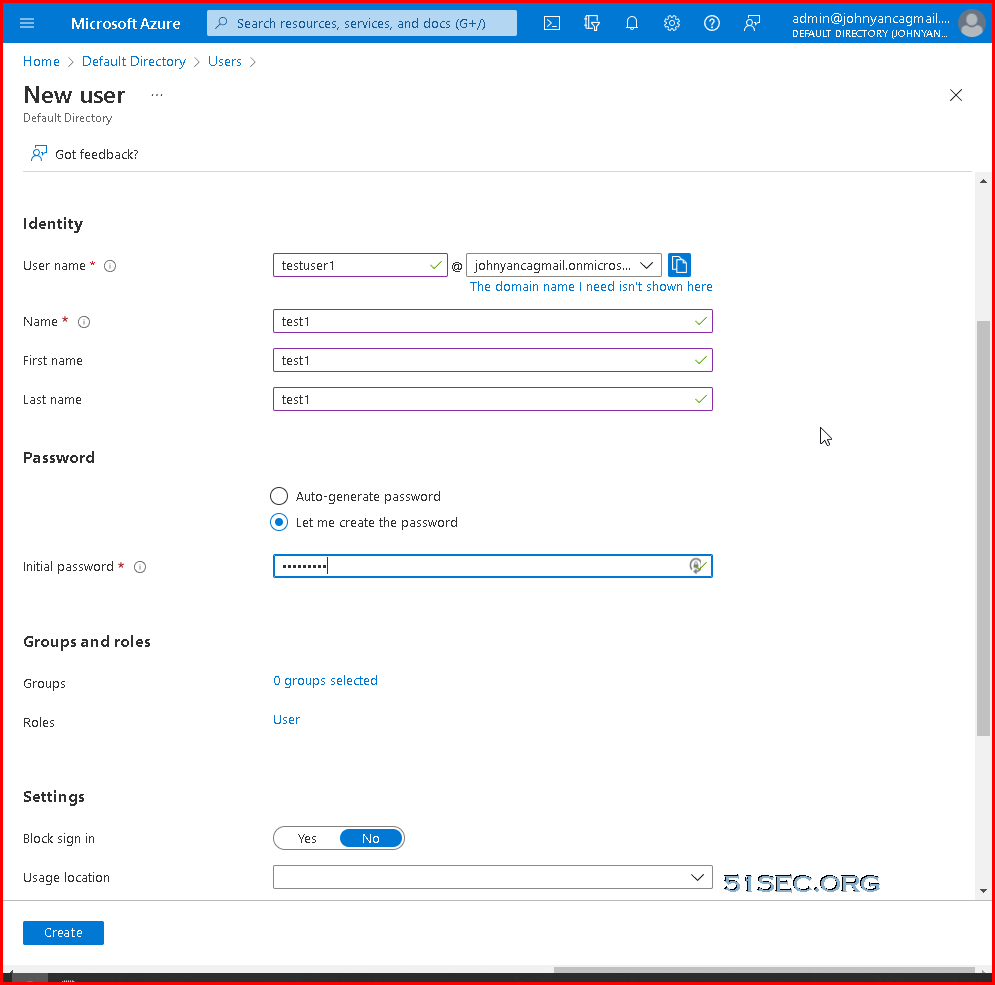
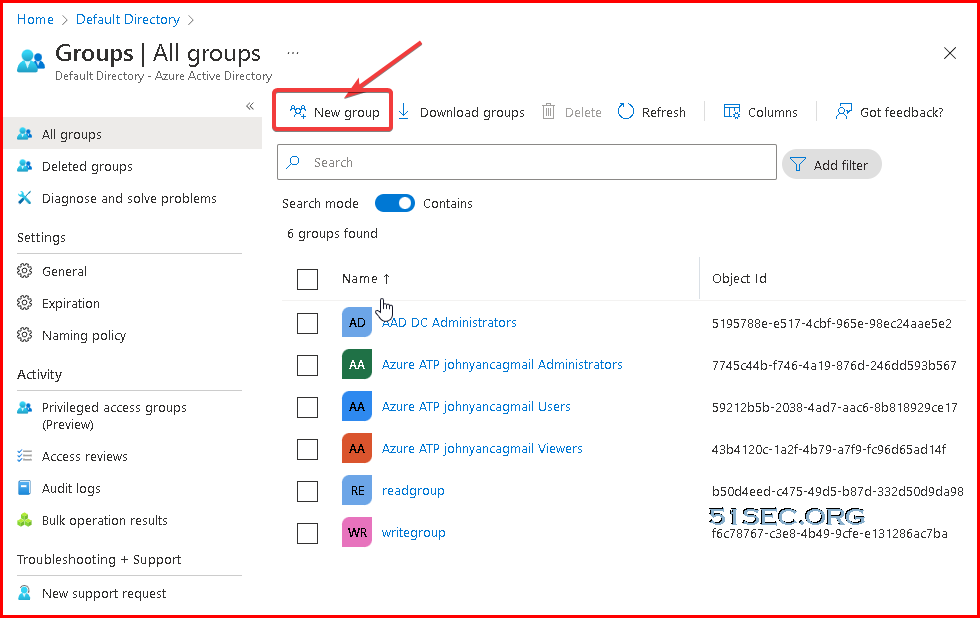
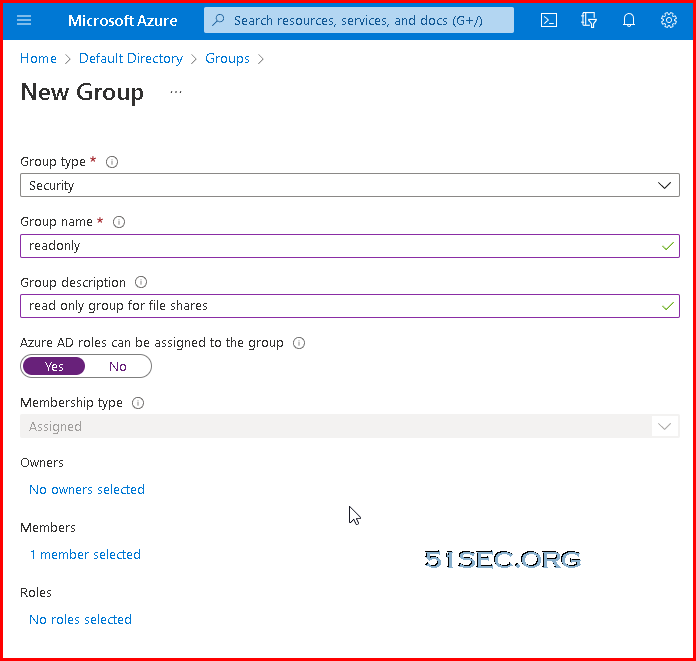
Create AAD Users & Groups
Create AAD UsersCreate AAD Groups
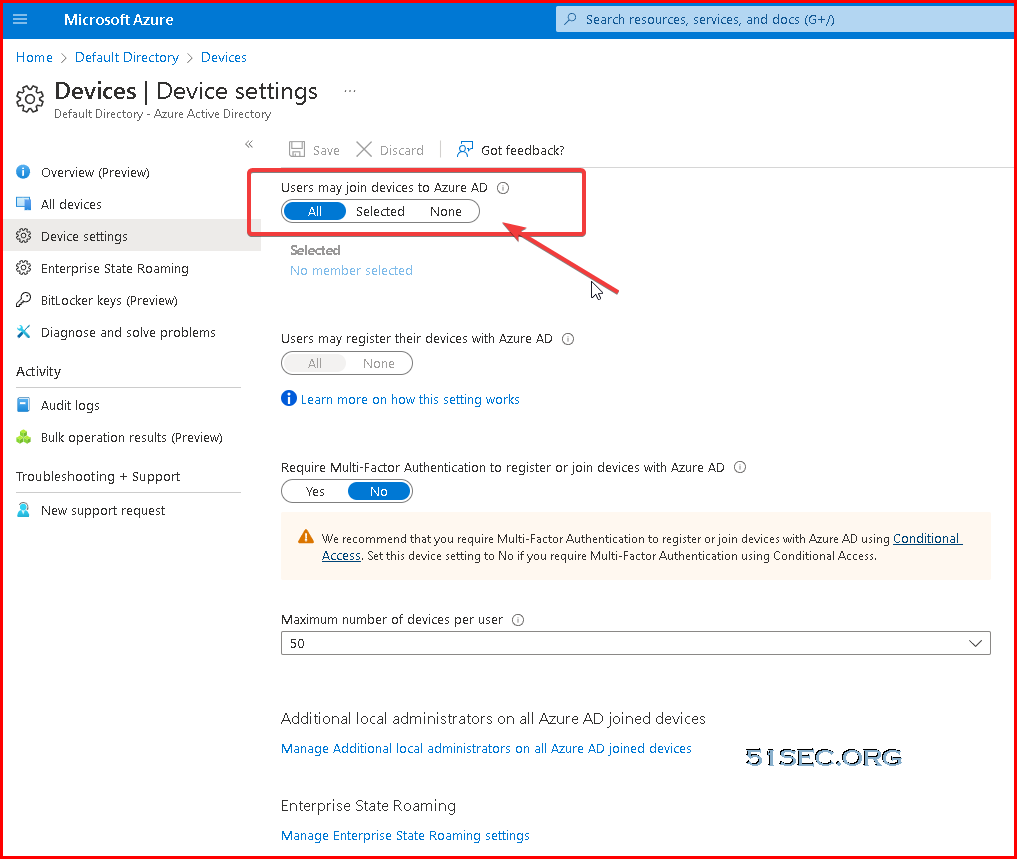
Get Windows Client AAD Joined
Prerequisites
| Operating Systems | All Windows 11 and Windows 10 devices except Home editions |
| Windows Server 2019 Virtual Machines running in Azure (Server core isn't supported) |
Azure AD join can be used in various scenarios like:
- You want to transition to cloud-based infrastructure using Azure AD and MDM like Intune.
- You can’t use an on-premises domain join, for example, if you need to get mobile devices such as tablets and phones under control.
- Your users primarily need to access Microsoft 365 or other SaaS apps integrated with Azure AD.
- You want to manage a group of users in Azure AD instead of in Active Directory. This scenario can apply, for example, to seasonal workers, contractors, or students.
- You want to provide joining capabilities to workers who work from home or are in remote branch offices with limited on-premises infrastructure
Difference between Domain / Hybrid / Azure AD Joined / Azure AD registered device:
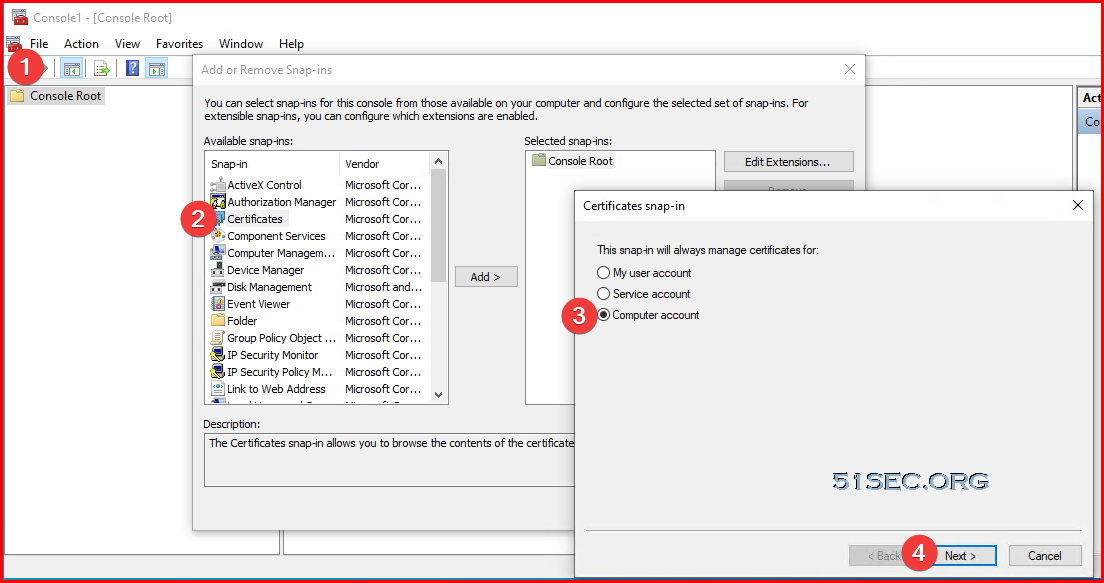
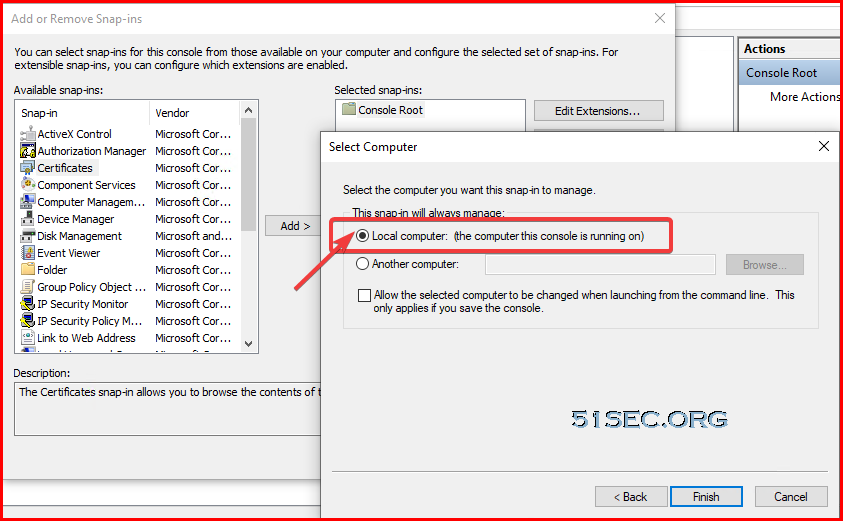
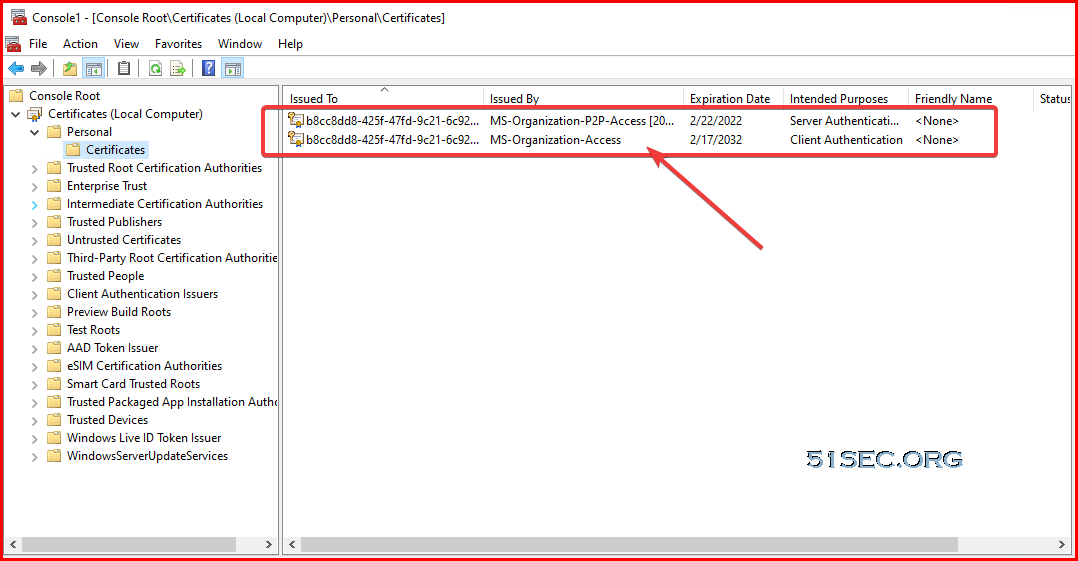
Verify
MMC - Add/Remove Snap-in - Certificate - Computer account - Local computer
- Certmgr.msc
- dsregcmd /status
C:\WINDOWS\system32>dsregcmd /status
+----------------------------------------------------------------------+
| Device State |
+----------------------------------------------------------------------+
AzureAdJoined : YES
EnterpriseJoined : NO
DomainJoined : NO
Device Name : test-win10-1
+----------------------------------------------------------------------+
| Device Details |
+----------------------------------------------------------------------+
DeviceId : b8cc8dd8-425f-47fd-9c21-6c923affc088
Thumbprint : 8B8092340E6EFA40356516D8DEC3DFE2E482E5B7
DeviceCertificateValidity : [ 2022-02-17 20:05:29.000 UTC -- 2032-02-17 20:35:29.000 UTC ]
KeyContainerId : 0003b850-d691-4ddc-b84e-c6fe74709a8c
KeyProvider : Microsoft Software Key Storage Provider
TpmProtected : NO
DeviceAuthStatus : SUCCESS
+----------------------------------------------------------------------+
| Tenant Details |
+----------------------------------------------------------------------+
TenantName : Default Directory
TenantId : 22dbd8e0-9e61-439a-8bd9-fdd502bff1dc
Idp : login.windows.net
AuthCodeUrl : https://login.microsoftonline.com/22dbd8e0-9e61-439a-8bd9-fdd502bff1dc/oauth2/authorize
AccessTokenUrl : https://login.microsoftonline.com/22dbd8e0-9e61-439a-8bd9-fdd502bff1dc/oauth2/token
MdmUrl :
MdmTouUrl :
MdmComplianceUrl :
SettingsUrl :
JoinSrvVersion : 2.0
JoinSrvUrl : https://enterpriseregistration.windows.net/EnrollmentServer/device/
JoinSrvId : urn:ms-drs:enterpriseregistration.windows.net
KeySrvVersion : 1.0
KeySrvUrl : https://enterpriseregistration.windows.net/EnrollmentServer/key/
KeySrvId : urn:ms-drs:enterpriseregistration.windows.net
WebAuthNSrvVersion : 1.0
WebAuthNSrvUrl : https://enterpriseregistration.windows.net/webauthn/22dbd8e0-9e61-439a-8bd9-fdd502bff1dc/
WebAuthNSrvId : urn:ms-drs:enterpriseregistration.windows.net
DeviceManagementSrvVer : 1.0
DeviceManagementSrvUrl : https://enterpriseregistration.windows.net/manage/22dbd8e0-9e61-439a-8bd9-fdd502bff1dc/
DeviceManagementSrvId : urn:ms-drs:enterpriseregistration.windows.net
+----------------------------------------------------------------------+
| User State |
+----------------------------------------------------------------------+
NgcSet : YES
NgcKeyId : {0802468D-D3EF-4857-A4DE-350CBE8F0BC0}
CanReset : DestructiveOnly
WorkplaceJoined : NO
WamDefaultSet : YES
WamDefaultAuthority : organizations
WamDefaultId : https://login.microsoft.com
WamDefaultGUID : {B16898C6-A148-4967-9171-64D755DA8520} (AzureAd)
+----------------------------------------------------------------------+
| SSO State |
+----------------------------------------------------------------------+
AzureAdPrt : YES
AzureAdPrtUpdateTime : 2022-02-21 23:44:39.000 UTC
AzureAdPrtExpiryTime : 2022-03-07 23:45:48.000 UTC
AzureAdPrtAuthority : https://login.microsoftonline.com/22dbd8e0-9e61-439a-8bd9-fdd502bff1dc
EnterprisePrt : NO
EnterprisePrtAuthority :
+----------------------------------------------------------------------+
| Diagnostic Data |
+----------------------------------------------------------------------+
AadRecoveryEnabled : NO
Executing Account Name : AzureAD\test1, [email protected]
KeySignTest : PASSED
+----------------------------------------------------------------------+
| IE Proxy Config for Current User |
+----------------------------------------------------------------------+
Auto Detect Settings : YES
Auto-Configuration URL :
Proxy Server List :
Proxy Bypass List :
+----------------------------------------------------------------------+
| WinHttp Default Proxy Config |
+----------------------------------------------------------------------+
Access Type : DIRECT
For more information, please visit https://www.microsoft.com/aadjerrors
C:\WINDOWS\system32>
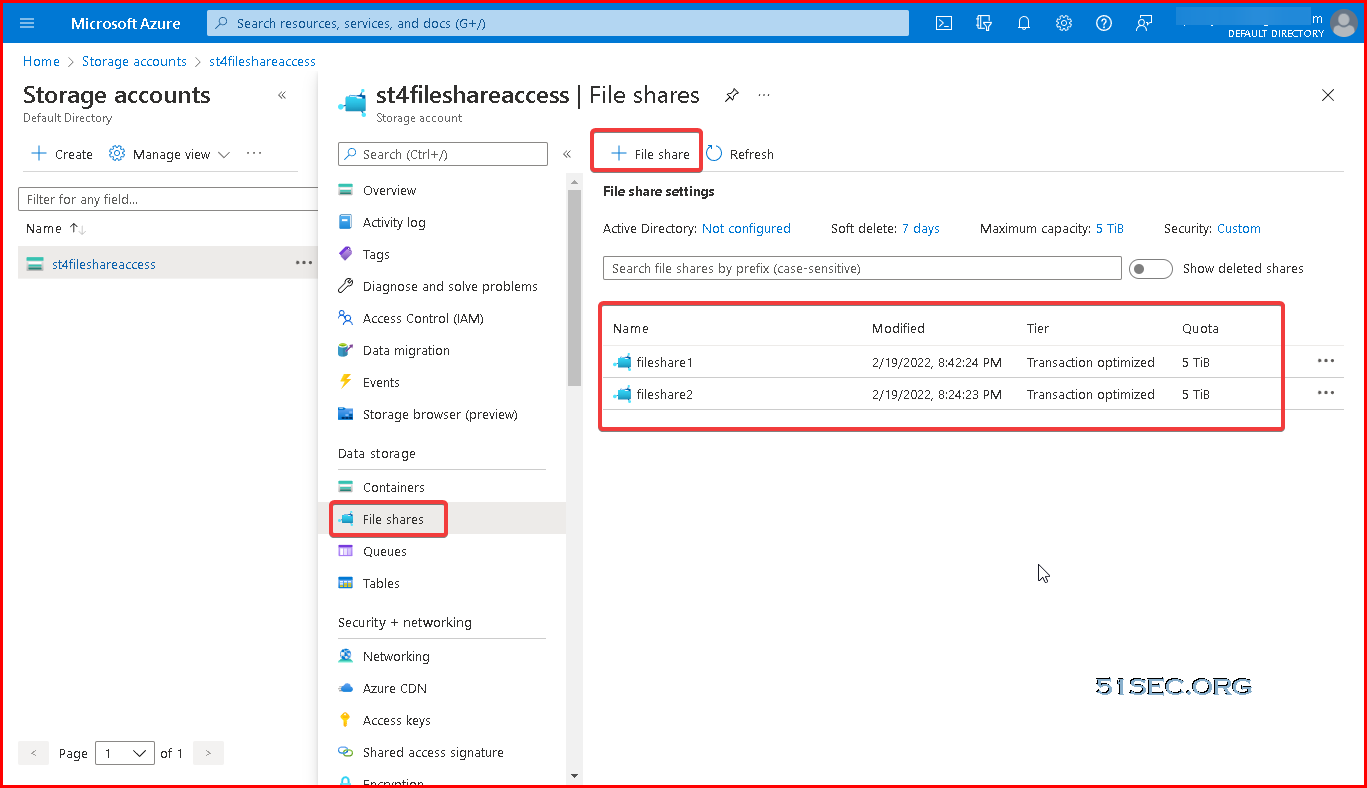
Create Storage Accounts and File Shares
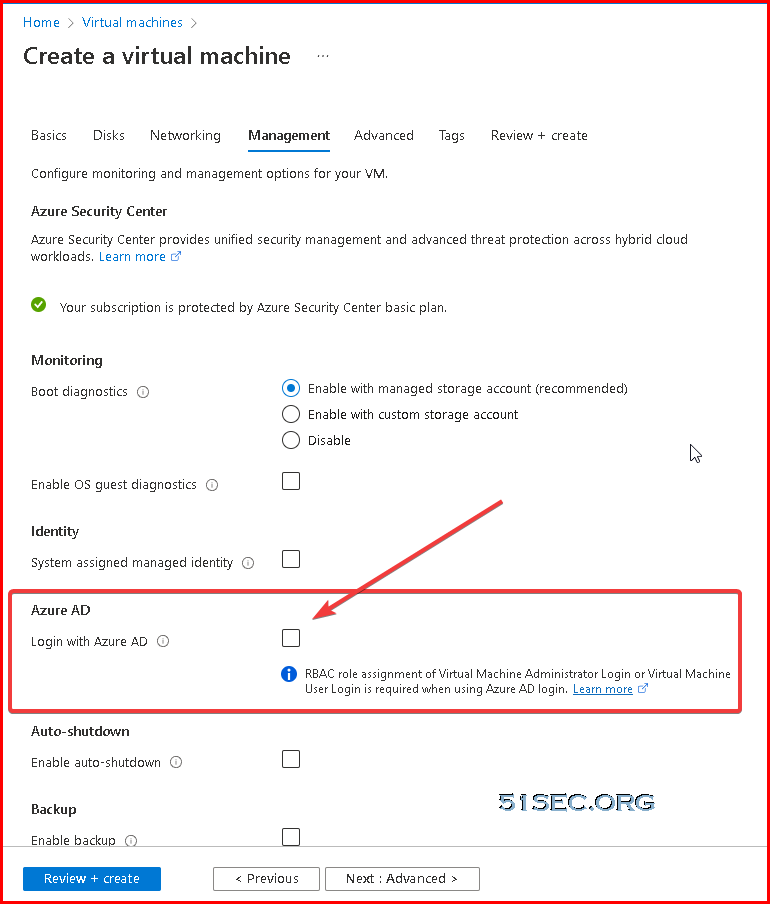
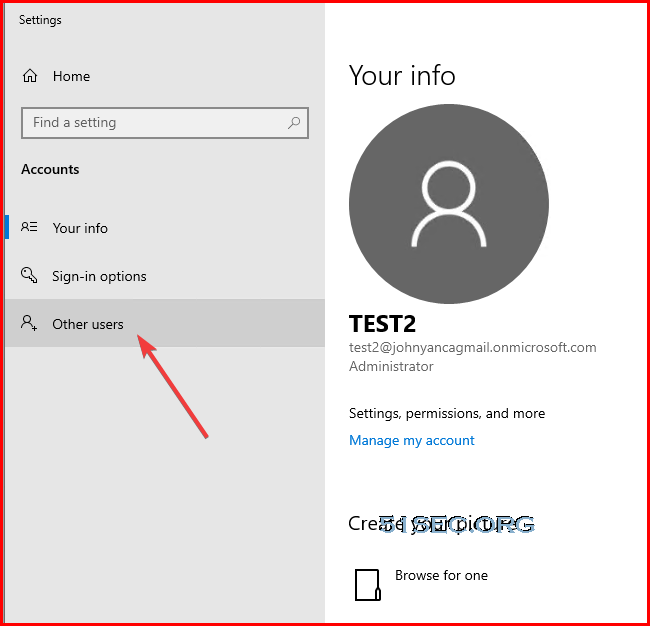
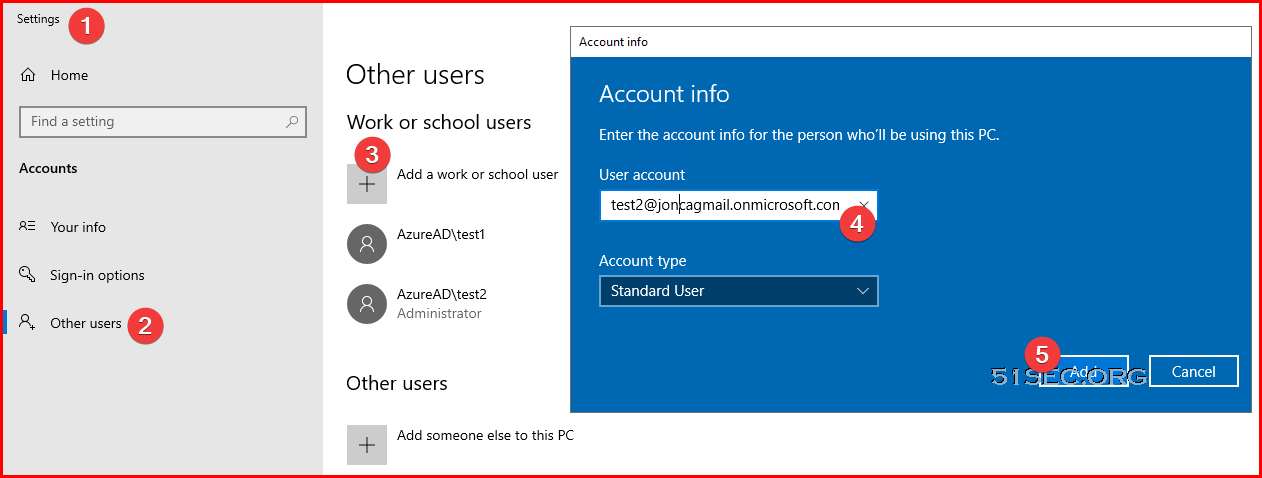
Create AAD Joined Windows 2019 Azure VM and Assign AAD Users Permission to VM
You can now join Windows 2019 Server to Azure AD using Azure AD domain Join. This uses Azure Active Directory (AD) authentication for Azure virtual machines running Windows Server 2019 Datacenter edition or Windows 10 1809 and later.
This provides a centrally controlled, policy driven method for logging on to VMs and authenticating using Azure AD.
This is carried out by using Azure tools such as Azure AD Conditional Access for MFA and Azure Role-Based Access Control (RBAC) to control access.
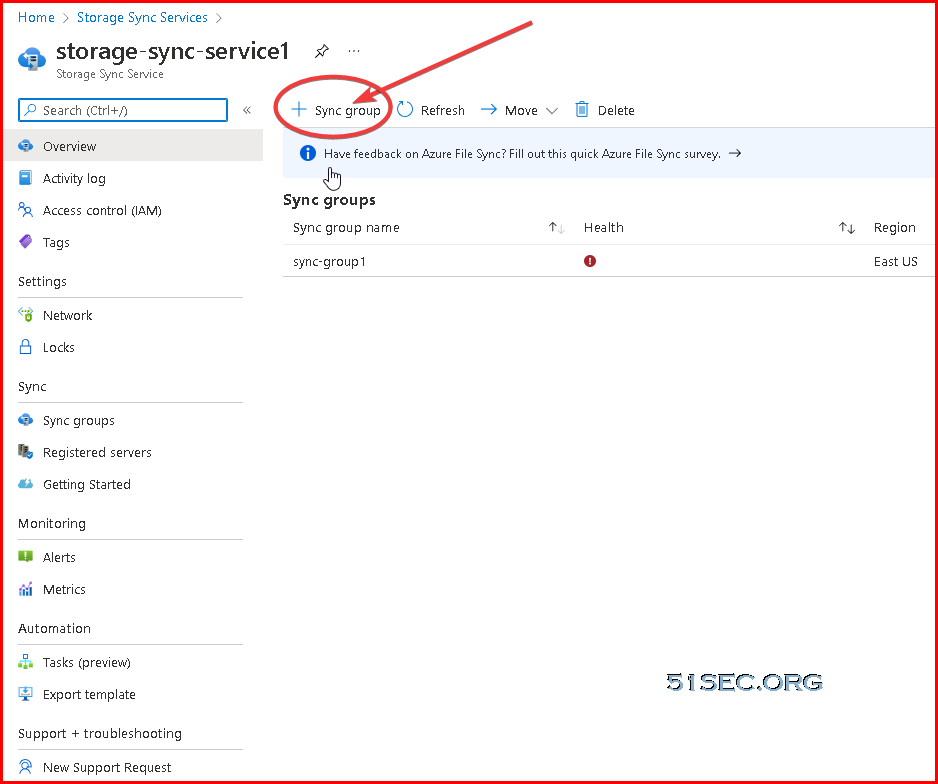
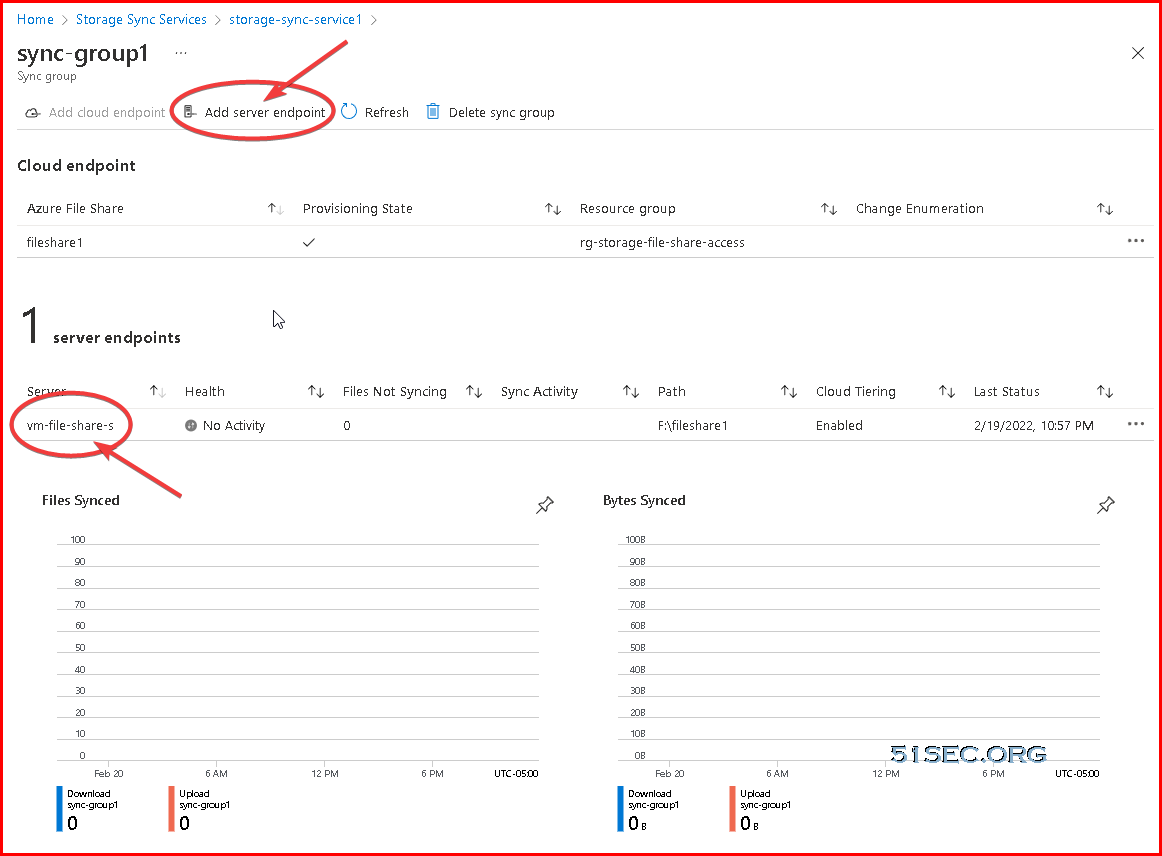
Create Storage Sync Service and Set up Tiered Sync and Shares
Create storage sync service:
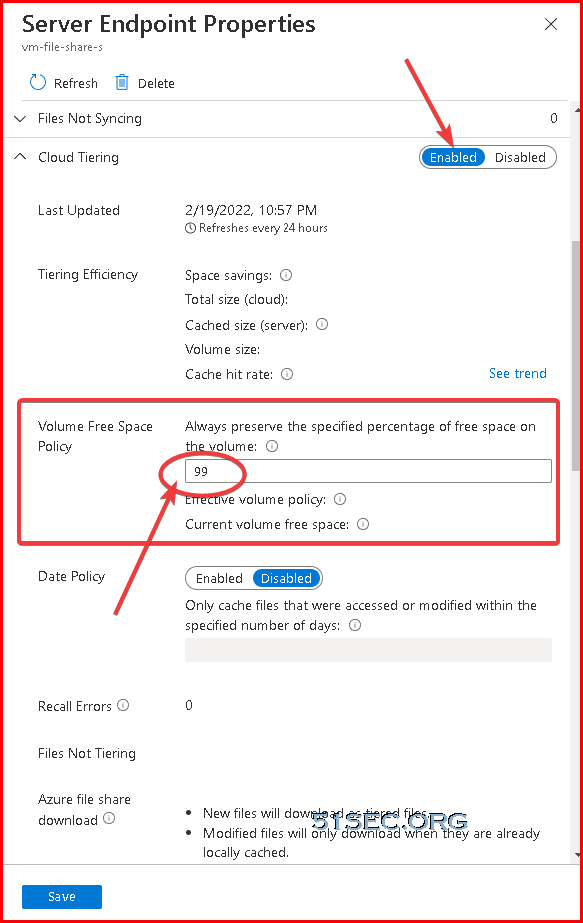
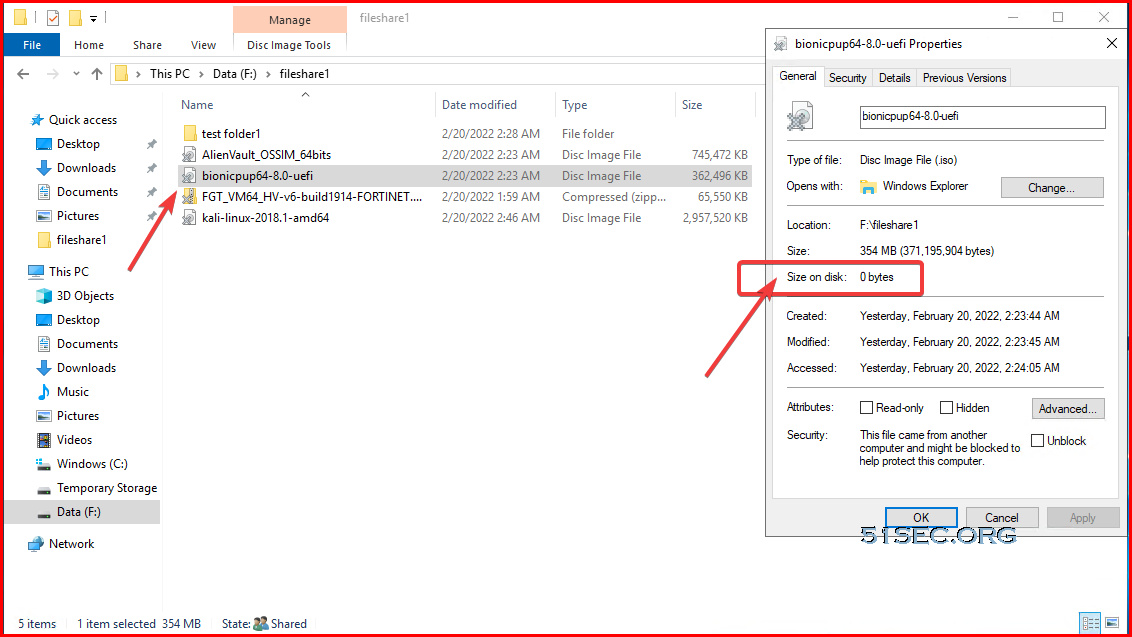
Cloud Tiering :
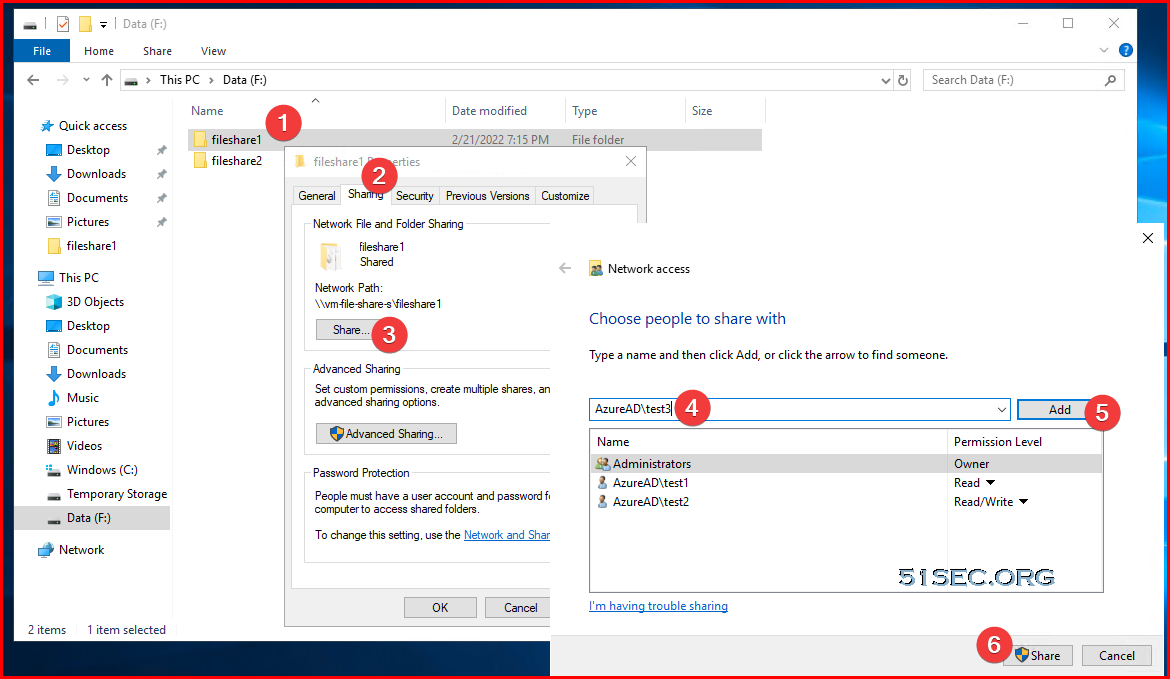
Assign AAD Users Permission to Share Folder
Add AAd accounts to have access to virtual machineAssign permission to share folders
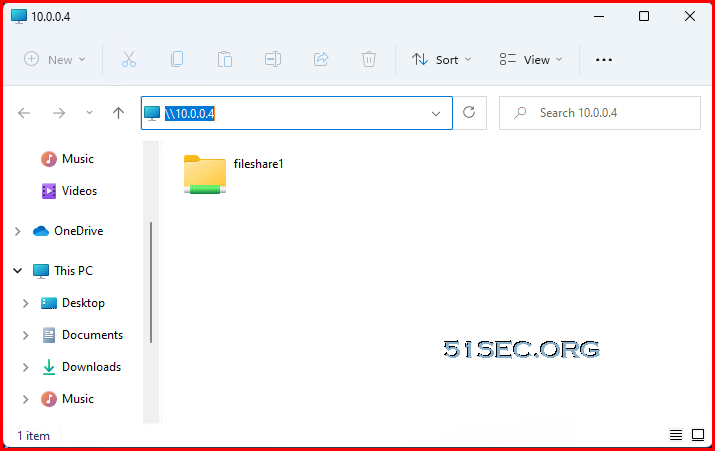
Create P2S VPN
Please refer to this post:Access Azure VM's File Share
PS C:\Users\test2> ipconfig
Windows IP Configuration
Ethernet adapter Ethernet0:
Connection-specific DNS Suffix . : lan
Link-local IPv6 Address . . . . . : fe80::fd79:1858:9a7c:5a4f%4
IPv4 Address. . . . . . . . . . . : 192.168.2.71
Subnet Mask . . . . . . . . . . . : 255.255.255.0
Default Gateway . . . . . . . . . : 192.168.2.1
PPP adapter rg-storage-file-share-access-vnet:
Connection-specific DNS Suffix . :
IPv4 Address. . . . . . . . . . . : 172.16.0.3
Subnet Mask . . . . . . . . . . . : 255.255.255.255
Default Gateway . . . . . . . . . :
PS C:\Users\test2> ping 10.0.0.4
Pinging 10.0.0.4 with 32 bytes of data:
Reply from 10.0.0.4: bytes=32 time=28ms TTL=127
Reply from 10.0.0.4: bytes=32 time=27ms TTL=127
Reply from 10.0.0.4: bytes=32 time=29ms TTL=127
Reply from 10.0.0.4: bytes=32 time=30ms TTL=127
Ping statistics for 10.0.0.4:
Packets: Sent = 4, Received = 4, Lost = 0 (0% loss),
Approximate round trip times in milli-seconds:
Minimum = 27ms, Maximum = 30ms, Average = 28ms
PS C:\Users\test2>
YouTube Videos
References
- Join your work device to your work or school network
- Azure AD joined devices
- https://www.youtube.com/watch?v=Dj3zOaQ3oUk
- Disable Mandatory Windows Hello for Business Prompt on Azure AD joined Devices









No comments:
Post a Comment