- Passive information gathering refers to gathering as much information as possible without establishing contact between the pen tester (yourself) and the target about which you are collecting information.
- Active information gathering involves contact between the pen tester and the actual target. When you actively query systems to gain the information you are moving to a dark legal situation as most countries prohibit attempts to break into systems without the necessary permission.
Topology
Information to be collected
- IP Addresses
- Company Address
- Email Addresses
- Domain Information
- Phone
- Staff
- Opened Ports on targets
- Applications running on targets
- OS
- Other Sensitive Information
Shodan
Shodan is a search engine that lets the user find specific types of devices (webcams, routers, servers, etc.) connected to the internet using a variety of filters. Shodan currently returns 10 results to users without an account and 50 to those with one.
Shodan has several powerful yet easy to use filters which prove handy during VA/PT exercises. The usage of filters is usually of the form filter:value.Some of the most common basic filters that you can use in Shodan are as follows.
- city: find devices in a particular city.
- country: find devices in a particular country.
- geo: search for specific GPS coordinates. geo:"31.8639, 117.2808"
- hostname: find values that match the hostname.
- product: search the name of the software or product identified in the banner.
- os: search based on operating system.
- port: find particular ports that are open.
- before/after: find results within a timeframe.
- org: search specific organization or company. org:"google"
- isp" search specific ISP. isp:"rogers"
- version:"13.1.6"
1. Country: The country filter allows users to search for computers running services in a particular country. The country code is specified as a two-letter word.
Usage: cisco country: IN (searches for Cisco devices in the particular country. In this case, it’s India).
2. Host name: This useful option in Shodan lets you find a particular service or the service running in specified hosts or domains.
Usage: "Server:IIS" host name: domain name
Host name: domain name
3. Net: This filter is used to scan a particular IP address or subnet range. The service name can also be added along with the IP address or subnet.
Usage: For scanning an IP address: net: 198.162.1.1(any IP)
For scanning a subnet: net: 198.162.1.1/24
4. Port: This filter allows you to scan a particular service. For instance, FTP (21), HTTP (80).
Usage: Service port number
Example: IIS port: 80
5. Operating system (OS): This Shodan filter helps you to identify a service with a required OS. You can use it to find the service running on the particular OS.
Usage: Service: OS: OS name
Example: IIS “OS: OSName”
6. After/before: This option helps or returns the query, changed or unchanged before.
Example: apache after: 22/03/2010 before: 4/6/2010
Example: apache country: CH after:22/03/2010 before: 4/6/2010
Whois
From Kali terminal :
whois 51sec.eu.org
Browser:
https://lookup.icann.org/
https://www.networksolutions.com/whois
intext: Find pages containing a certain word (or words) somewhere in the content.
filetype: Restrict results to those of a certain filetype. E.g., PDF, DOCX, TXT, PPT, etc. The “ext:” operator can also be used—the results are identical.
intitle: Find pages with a certain word (or words) in the title
info:
cache: Returns the most recent cached version of a web page
site:msn.com intitle:admin|user|password|account|login|system|manage
site:msn.com inurl:robots.txt
site:msn.com inurl:txt
SubDomain Scanning
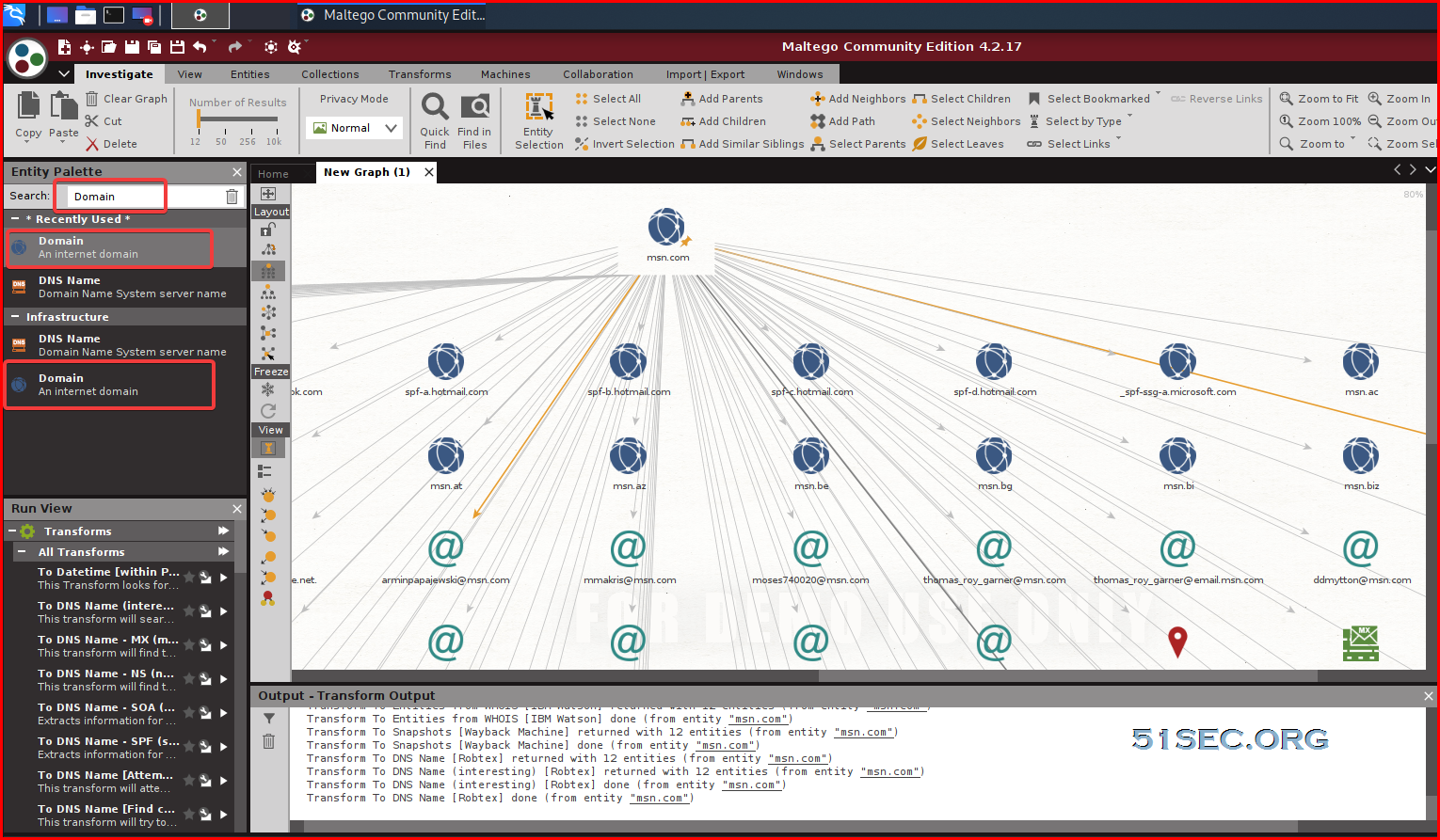
Using Maltego from Kali- http://builtwith.com/
- https://spyse.com/
- https://securitytrails.com/
- https://github.com/euphrat1ca/LayerDomainFinder
- Google search: site:51sec.org
- http://tool.chinaz.com/subdomain
- https://dnsdumpster.com/
- Certs : https://crt.sh, http://centsys.io
- Other methods: https://phpinfo.me/domain, http://dns.aizhan.com
- Other tools helps to find out subdomain related information:
- AMASS
┌──(root💀kali)-[~]
└─# amass enum -d 51sec1.eu.org
blog.51sec1.eu.org
www.51sec1.eu.org
www-oct.51sec1.eu.org
www-smtp-api.51sec1.eu.org
wwwlax.51sec1.eu.org
wwwc.51sec1.eu.org
w3-qa.51sec1.eu.org
www-qa-2.51sec1.eu.org
wwwnginxsearch.51sec1.eu.org
www-qa10.51sec1.eu.org
www-akali.51sec1.eu.org
www-smtpbrasil.51sec1.eu.org
w-www-smtp.51sec1.eu.org
www-akaliregion.51sec1.eu.org
...(Omitted)
www-smtp-brasil-boards.51sec1.eu.org
wwwnginxsearchdev.51sec1.eu.org
www-smtp-brasil-net.51sec1.eu.org
w-www-smtp-ghcpi.51sec1.eu.org
www-oct-box-singed.51sec1.eu.org
^C
OWASP Amass v3.12.3 https://github.com/OWASP/Amass
--------------------------------------------------------------------------------
567 names discovered - alt: 565, cert: 1, scrape: 1
--------------------------------------------------------------------------------
ASN: 15169 - GOOGLE - Google LLC
172.217.0.0/19 1 Subdomain Name(s)
2607:f8b0:4006::/48 1 Subdomain Name(s)
ASN: 13335 - CLOUDFLARENET - Cloudflare, Inc.
172.67.0.0/16 1 Subdomain Name(s)
ASN: 20940 - AKAMAI-ASN1
23.202.231.0/24 565 Subdomain Name(s)
23.217.138.0/24 565 Subdomain Name(s)
The enumeration has finished
Discoveries are being migrated into the local database
┌──(root💀kali)-[~]
└─#
- SubBrute
- Knockpy
┌──(root💀kali)-[~]
└─# knockpy 127 ⨯
Command 'knockpy' not found, but can be installed with:
apt install knockpy
Do you want to install it? (N/y)y
apt install knockpy
Reading package lists... Done
Building dependency tree... Done
Reading state information... Done
The following NEW packages will be installed:
knockpy
0 upgraded, 1 newly installed, 0 to remove and 2 not upgraded.
Need to get 17.2 kB of archives.
After this operation, 68.6 kB of additional disk space will be used.
Get:1 http://kali.download/kali kali-rolling/main amd64 knockpy all 4.1.0-4 [17.2 kB]
Fetched 17.2 kB in 1s (23.5 kB/s)
Selecting previously unselected package knockpy.
(Reading database ... 276265 files and directories currently installed.)
Preparing to unpack .../knockpy_4.1.0-4_all.deb ...
Unpacking knockpy (4.1.0-4) ...
Setting up knockpy (4.1.0-4) ...
Processing triggers for kali-menu (2021.2.2) ...
Processing triggers for man-db (2.9.4-2) ...
┌──(root💀kali)-[~]
└─# knockpy 127 ⨯
usage: knockpy [-h] [--version] [-w WORDLIST] [-r] [-c] [-f] [-j] domain
knockpy: error: the following arguments are required: domain
┌──(root💀kali)-[~]
└─# knockpy msn.com
_ __ _
| |/ / | | 4.1.1
| ' / _ __ ___ ___| | ___ __ _ _
| < | '_ \ / _ \ / __| |/ / '_ \| | | |
| . \| | | | (_) | (__| <| |_) | |_| |
|_|\_\_| |_|\___/ \___|_|\_\ .__/ \__, |
| | __/ |
|_| |___/
+ checking for virustotal subdomains:SKIP
VirusTotal API_KEY not found
+ checking for wildcard:YES
{
"status_code": 301,
"content_length": ""
}
+ checking for zonetransfer:NO
+ resolving target:YES
- scanning for subdomain...
Ip Address Status Type Domain Name Server
---------- ------ ---- ----------- ------
202.89.232.117 host 6.msn.com
204.79.197.203 302 alias a.msn.com
204.79.197.203 302 alias a-msn-com.a-0003.a-msedge.net
204.79.197.203 302 host a-0003.a-msedge.net
204.79.197.200 400 alias about.msn.com
204.79.197.200 400 alias about-msn-com.a-0001.a-msedge.net
204.79.197.200 400 host dual-a-0001.a-msedge.net
13.107.21.200 400 host dual-a-0001.a-msedge.net
...(Omitted)
64.73.25.131 host win.msn.com
204.79.197.203 301 alias windows.msn.com
204.79.197.203 301 alias www-msn-com.a-0003.a-msedge.net
204.79.197.203 301 host a-0003.a-msedge.net
208.91.197.27 alias windowsxp.msn.com
208.91.197.27 host eshop.com
204.79.197.203 302 alias www.msn.com
204.79.197.203 302 alias www-msn-com.a-0003.a-msedge.net
204.79.197.203 302 host a-0003.a-msedge.net
208.91.197.27 alias xp.msn.com
208.91.197.27 host eshop.com
┌──(root💀kali)-[~]
└─#
FOFA
https://fofa.so/ - FOFA(网络空间资产检索系统)是世界上数据覆盖更完整的IT设备搜索引擎,拥有全球联网IT设备更全的DNA信息。探索全球互联网的资产信息,进行资产及漏洞影响范围分析、应用分布统计、应用流行度态势感知等。Links: FOFA、FOEYE、FOCII、EWSIS、检查工具箱;








No comments:
Post a Comment