Intel has announced Intel Developer Cloud trial is open to prequalified Intel customers and approved developers on their website. But actually it is open to almost everyone who has an email address. In this post, I am going to show you how to get this free 4 CPU Cores, 8GM RAM, 10GB Storage VPS from Intel Developer Cloud.
There is a time limitation how long this VM can last, five days. Basically you can get one high performance VM with Internet access, root permission for five days to use.
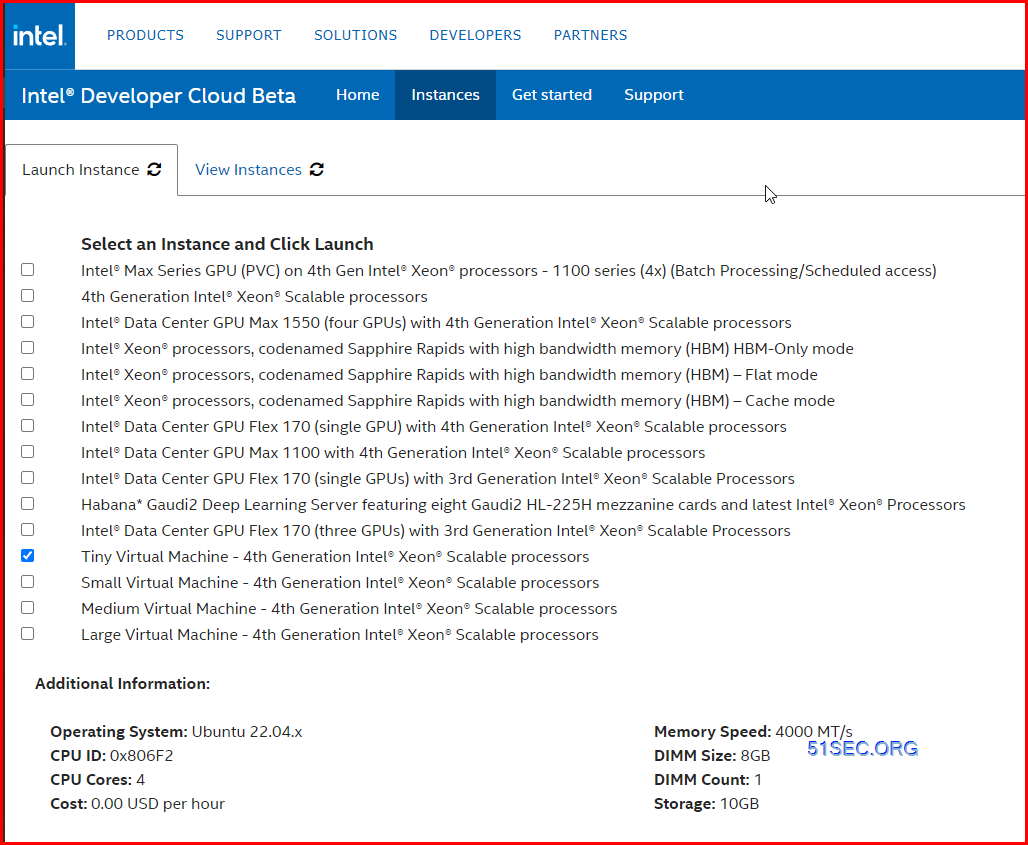
Specifications
- Make sure your Intel® Developer Zone profile has a valid US Cell Phone number.
Steps to launch free VM
To get started, three high level steps:
- Sign up for a standard Intel® Developer Zone account.
- Explore the service catalog.
- Schedule and deploy the service with Intel® Developer Cloud management console.
1 Sign up an account
URL: https://www.intel.com/content/www/us/en/developer/tools/devcloud/services.html
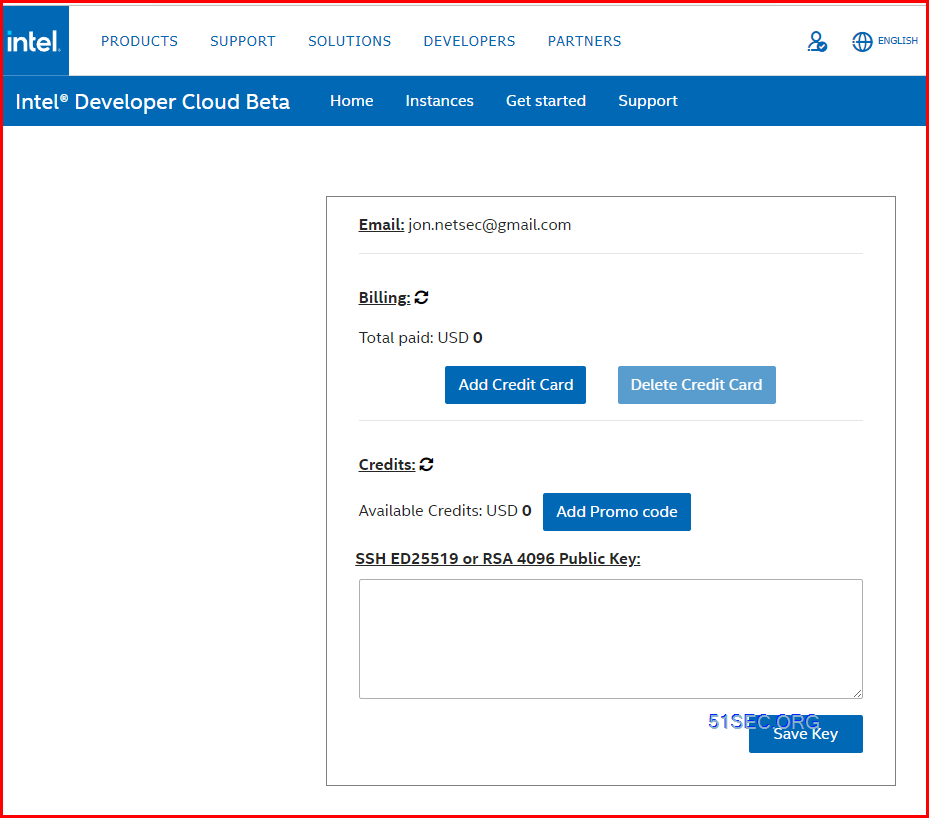
2 Sign in to launch instance
You might need to generate your OpenSSH Public Key
Windows*
mkdir %USERPROFILE%\.ssh
ssh-keygen -t ed25519 -f %USERPROFILE%\.ssh\id_rsa
Windows*:
notepad %USERPROFILE%\.ssh\id_rsa.pub
Note: The public key must be in your profile before starting an instance. The instance will need to be relaunched if the public key was updated after a virtual machine is launched.
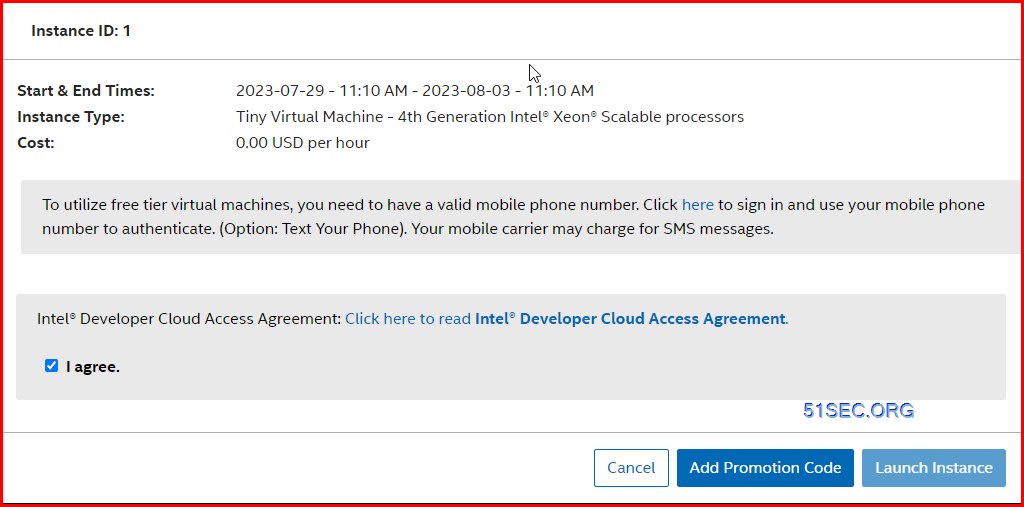
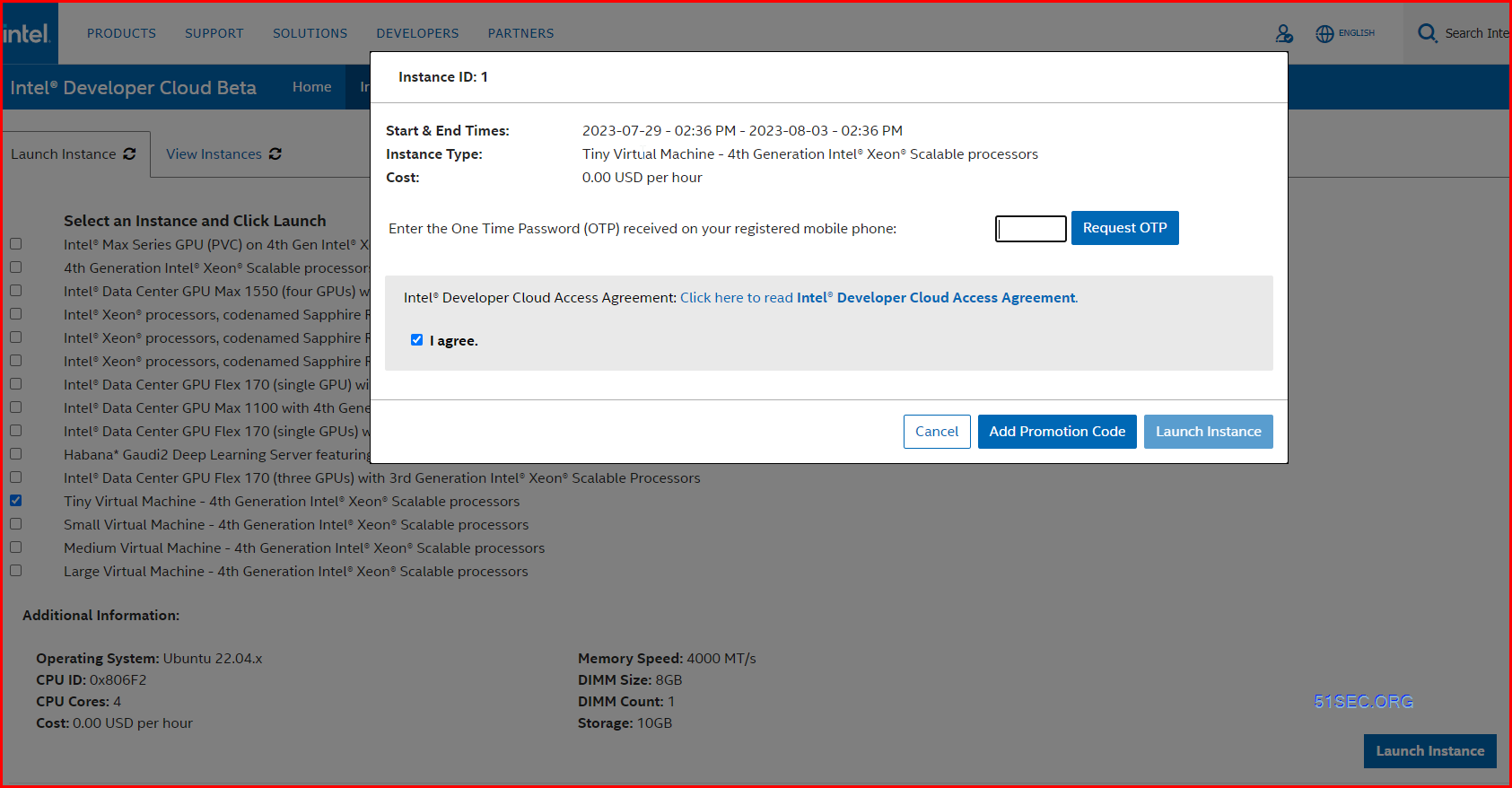
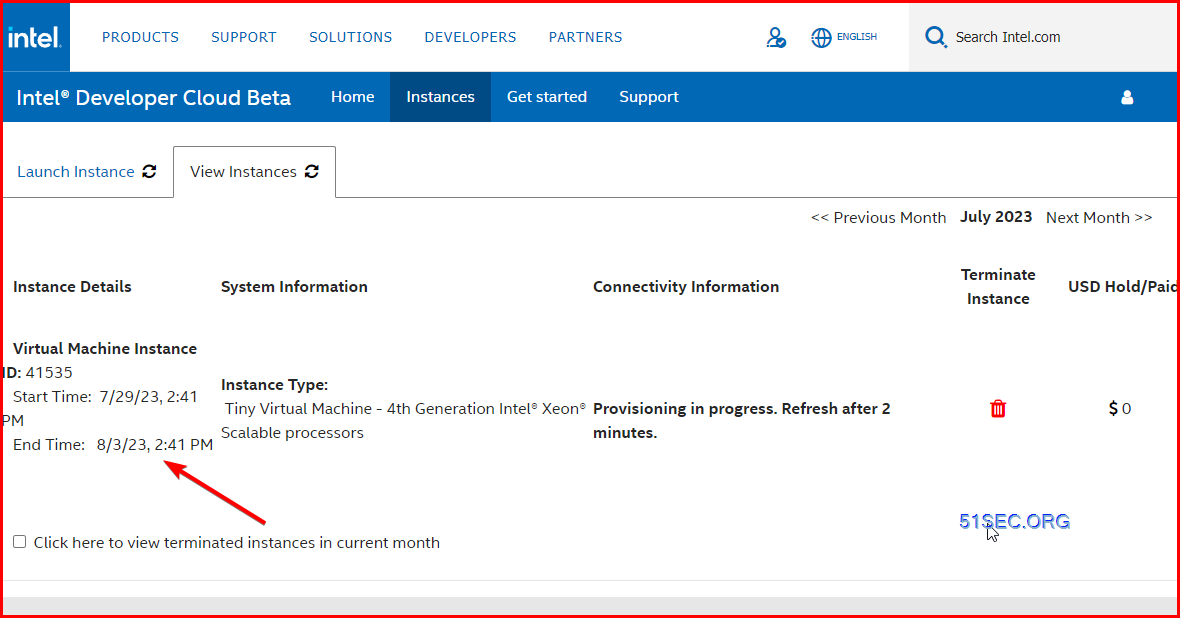
3 Launch Tiny VM
A mobile phone number be needed for launching free tier virtual machines. If you have not verified or entered your mobile phone number before, you will get following message to enter a valid mobile phone number.
4 Generate your public key in your windows command line and log into your VM
Note: https://scheduler.cloud.intel.com/public/Intel_Developer_Cloud_Getting_Started.html#setupsshkeys
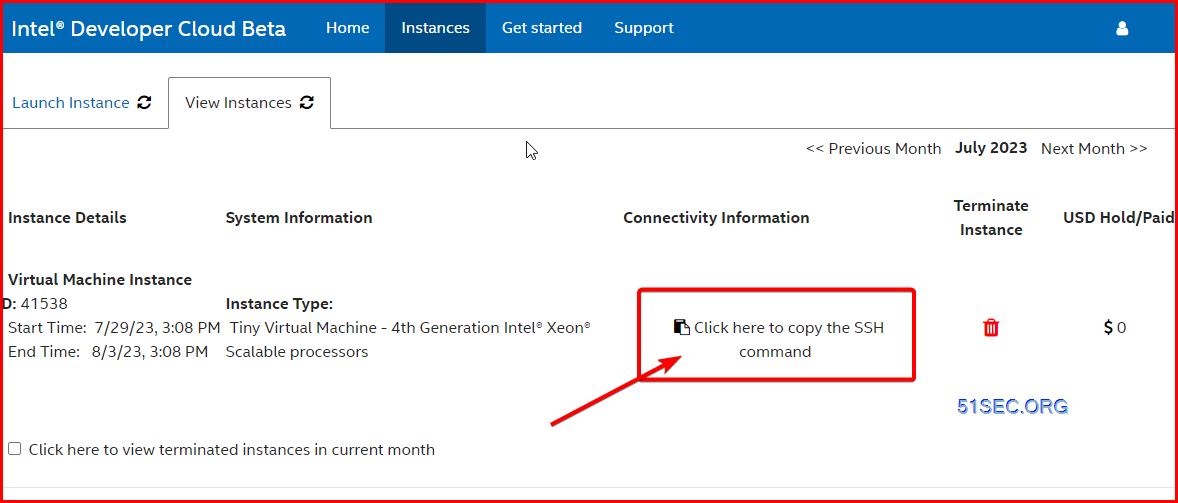
You can copy the ssh command from View instances page:
From my Windows 10 machine 's CMD window:
Microsoft Windows [Version 10.0.19045.3208]
(c) Microsoft Corporation. All rights reserved.
C:\Users\User>mkdir %USERPROFILE%\.ssh & ssh-keygen -t ed25519 -f %USERPROFILE%\.ssh\id_rsa
A subdirectory or file C:\Users\User\.ssh already exists.
Generating public/private ed25519 key pair.
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in C:\Users\User\.ssh\id_rsa.
Your public key has been saved in C:\Users\User\.ssh\id_rsa.pub.
The key fingerprint is:
SHA256:GKjFNupltaZgTM4CQqDplp2POvnNZTYm1WBWZ6rm32g user@minipc2
The key's randomart image is:
+--[ED25519 256]--+
|o. . o |
|o. . . . + |
|= . * o+ . |
|+=o=.oo++ |
|.+Ooo ++S. |
|.+ +oo+ |
| o..o B |
| o. o * oEo |
| .o. o .o . |
+----[SHA256]-----+
C:\Users\User>type %USERPROFILE%\.ssh\id_rsa.pub
ssh-ed25519 AAAAC3NzaC2lZDI1NTE5AAAAIJyWVCqihSxYXx21E4BXwEv1t3Tn3LvatYkljIZRf+2t user@minipc
C:\Users\User>ssh -J [email protected] -L 10022:10.2.155.107:22 [email protected]
The authenticity of host '146.152.226.46 (146.152.226.46)' can't be established.
ECDSA key fingerprint is SHA256:yI1eGvLTKfCCpuX7my+UFyrU041ZJM/i+0kGKYhFUn0.
Are you sure you want to continue connecting (yes/no/[fingerprint])?
Warning: Permanently added '146.152.226.46' (ECDSA) to the list of known hosts.
Welcome to Ubuntu 22.04.1 LTS (GNU/Linux 5.15.0-56-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Sat Jul 29 19:12:29 UTC 2023
System load: 0.1298828125 Processes: 154
Usage of /: 20.2% of 9.51GB Users logged in: 0
Memory usage: 3% IPv4 address for enp1s0: 10.2.155.107
Swap usage: 0%
158 updates can be applied immediately.
94 of these updates are standard security updates.
To see these additional updates run: apt list --upgradable
The programs included with the Ubuntu system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Ubuntu comes with ABSOLUTELY NO WARRANTY, to the extent permitted by
applicable law.
To run a command as administrator (user "root"), use "sudo <command>".
See "man sudo_root" for details.
ubuntu@cloud41538:~$
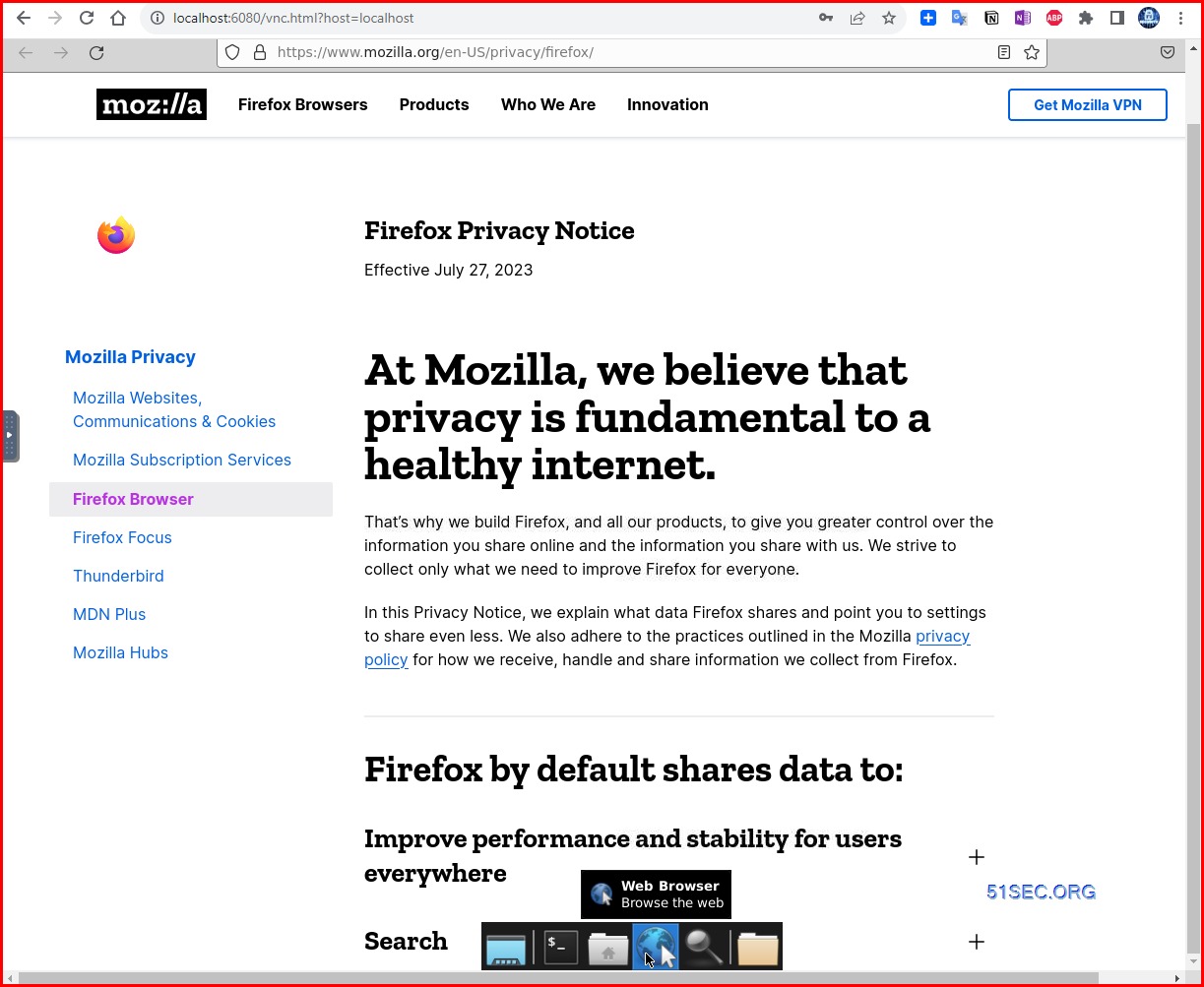
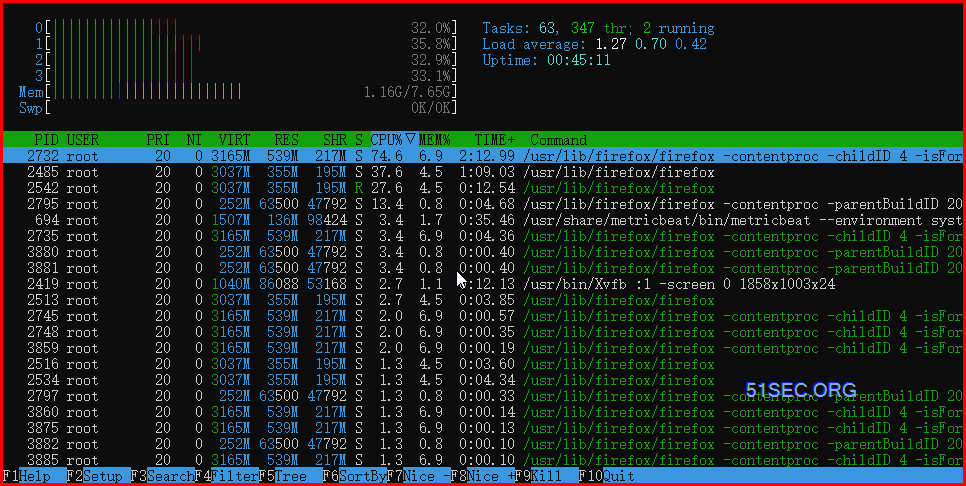
Run noVNC Web GUI access to instance
To enable GUI access to this launched instance, run following codes and then connect to the instance directly through your browser:
sudo apt install xfce4 xfce4-goodies tightvncserver xterm firefox -y
sudo update-alternatives --config x-terminal-emulator
snap install novnc
mkdir ~/.vnc
cat > ~/.vnc/xstartup <<EOF
#!/bin/bash
xrdb $HOME/.Xresources
startxfce4 &
EOF
chmod +x ~/.vnc/xstartup
vncserver -geometry 1280x1024 :1
novnc --vnc localhost:5901 &
Steps to connect to it:
1. From your local computer's powershell window, disconnect from your connected VPS instance2. Add -L 6080:localhost:6080 to end of your SSH Connection Command and connect
- ssh -J [email protected] -L 10022:10.2.155.107:22 [email protected] -L 6080:localhost:6080
4. Launch xterm and run the command xhost +
5. From the GUI, you can launch any installed application
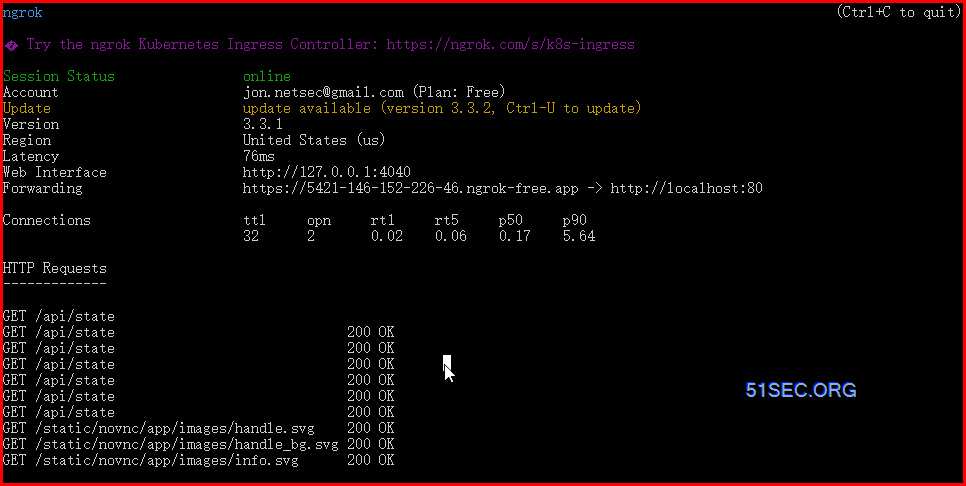
Run noVNC desktop environment using Docker & Ngrok Tunnel
All related commands:
- apt update
- apt install docker.io
- snap install ngrok
- ngrok config add-authtoken zzzzzzzzzzzzzyyyyyyyyyyxxxxxxxxxxxxxxxxxxxxxxx
- https://dashboard.ngrok.com/
- docker run -d -p 80:80 -e HTTP_PASSWORD=password -v /dev/shm:/dev/shm dorowu/ubuntu-desktop-lxde-vnc
- apt install screen
- screen -S bash
- screen -S <command> //create a new session to run a command
- screen -ls //listing all screen session
- screen -R <session name> //retach to the session
- ctrl+a d
- ngrok http 80
- ngrok tcp 3389
https://5421-146-152-226-46.ngrok-free.app/
Or, you do need to install ngrok, and you can access it through local SSH tunnel:
- ssh -J [email protected] [email protected] -L 80:localhost:80
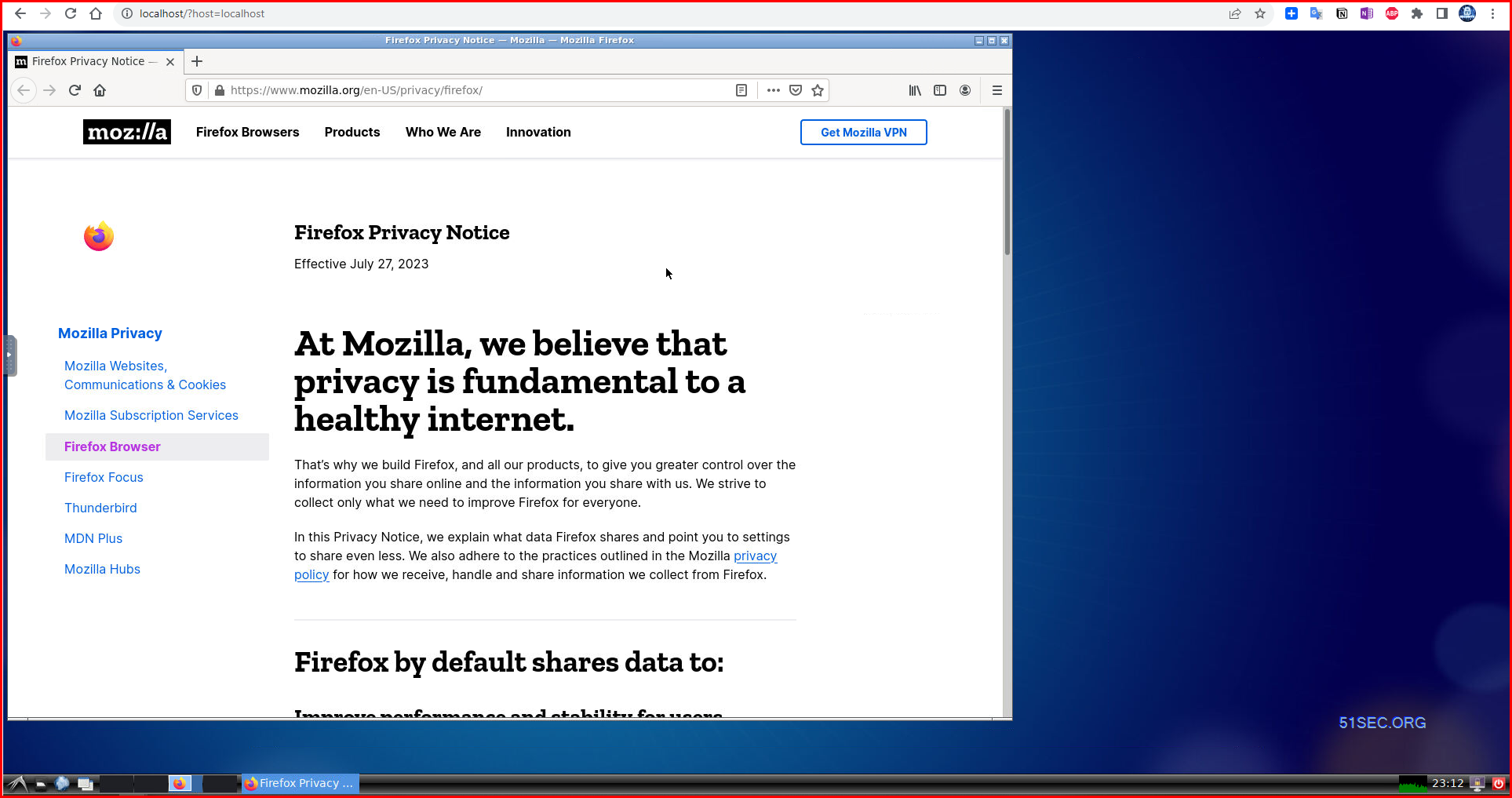
- Click here to GUI http://localhost/?host=localhost
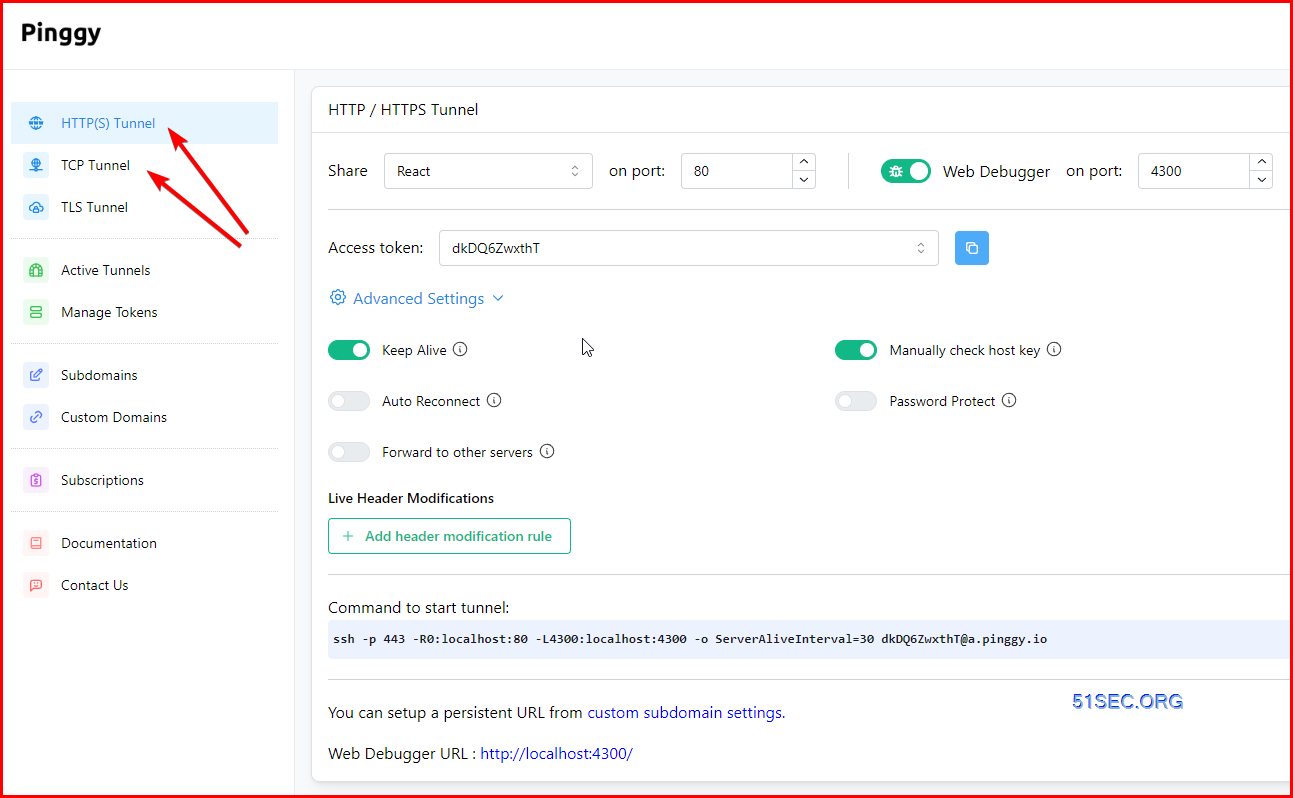
Using Pinggy Tunnel
Pinggy is the easiest way to get public URLs for your localhost. You can use it to quickly host a website from your laptop, receive webhooks, share files, connect to your Raspberry Pi, and more.
Follow the three simple steps to get started:
Step 1: Run your service in localhost
First you need to run the service you want to share in localhost. For example you may be using a webserver like Apache. Make sure your service is available in a localhost URL such as http://localhost:8080.
You can quickly launch such a server for testing purposes using Python: python3 -m http.server . This will start a server at http://localhost:8000.
Following screenshot is using port 80 for local http site.
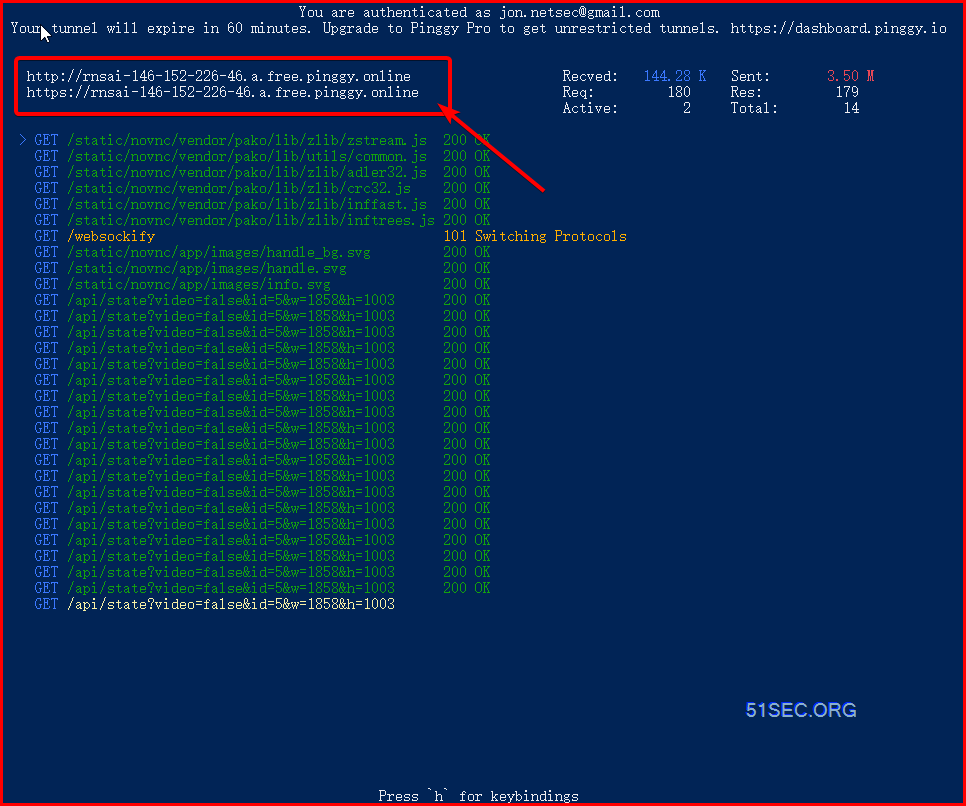
Step 2: Create a tunnel using a single command
ssh -p 443 -R0:localhost:80 a.pinggy.io
Replace the port 80 with the localhost port where your service is running.
Step 3: Access through public URL
The above command will provide you http and https URLs as follows:
You can access local server via following URL(s):
http://fakqxzqrohxxx.a.pinggy.online
https://fakqxzqrohxxx.a.pinggy.online
You can access your localhost service using these URLs.
Run xRDP with Audio Support
Check the following blog posts for more details:
- Install xRDP with Ubuntu Desktop on Oracle ARM VM ( xRDP Sound Support)
- DD Original Ubuntu Image to Oracle ARM VM and Install Lxde desktop and xRDP with Sound Forwarding
There will be no sound from other accounts. But if you are using default rdpuser account to log in, the sound is supported.
echo "Default Username: rdpuser"
echo "Default Password: rdpuser_password"Scanning Outgoing Ports to Find out Non-Restricted Ports
Mapping all the open outgoing ports is actually pretty straightforward, with two tools: nmap and portquiz.
Install nmap:
- apt install nmap
- snap install nmap
- You have to grant network access to nmap with:
snap connect nmap:network-control
Finding restricted ports is as easy as scanning all the ports of Portquiz or scanme.nmap.org with nmap:
- # Scan the 100 first ports only: nmap portquiz.net -p1-100 -v
- # Scan all the 65535 ports (this may take a long time): nmap portquiz.net -p1-65535 -v
- time nmap -p- portquiz.net | grep -i open
- nmap -sU scanme.nmap.org
- nmap scanme.nmap.org -p1-65535 -v
root@cloud43123:~# nmap scanme.nmap.org -p1-65535 -v
Starting Nmap 7.80 ( https://nmap.org ) at 2023-08-19 15:58 UTC
Initiating Ping Scan at 15:58
Scanning scanme.nmap.org (45.33.32.156) [4 ports]
Completed Ping Scan at 15:58, 0.05s elapsed (1 total hosts)
Initiating Parallel DNS resolution of 1 host. at 15:58
Completed Parallel DNS resolution of 1 host. at 15:58, 0.00s elapsed
Initiating SYN Stealth Scan at 15:58
Scanning scanme.nmap.org (45.33.32.156) [65535 ports]
Discovered open port 80/tcp on 45.33.32.156
SYN Stealth Scan Timing: About 20.24% done; ETC: 16:01 (0:02:02 remaining)
SYN Stealth Scan Timing: About 48.53% done; ETC: 16:00 (0:01:05 remaining)
Completed SYN Stealth Scan at 16:00, 104.79s elapsed (65535 total ports)
Nmap scan report for scanme.nmap.org (45.33.32.156)
Host is up (0.021s latency).
Other addresses for scanme.nmap.org (not scanned): 2600:3c01::f03c:91ff:fe18:bb2f
Not shown: 65533 filtered ports
PORT STATE SERVICE
80/tcp open http
443/tcp closed https
Read data files from: /usr/bin/../share/nmap
Nmap done: 1 IP address (1 host up) scanned in 104.97 seconds
Raw packets sent: 131153 (5.771MB) | Rcvd: 84 (3.364KB)
root@cloud43123:~# nmap -sU portquiz.net
Starting Nmap 7.80 ( https://nmap.org ) at 2023-08-19 16:02 UTC
Nmap scan report for portquiz.net (35.180.139.74)
Host is up (0.15s latency).
rDNS record for 35.180.139.74: ec2-35-180-139-74.eu-west-3.compute.amazonaws.com
Not shown: 998 open|filtered ports
PORT STATE SERVICE
53/udp closed domain
123/udp closed ntp
Nmap done: 1 IP address (1 host up) scanned in 12.51 seconds
root@cloud43123:~#








No comments:
Post a Comment