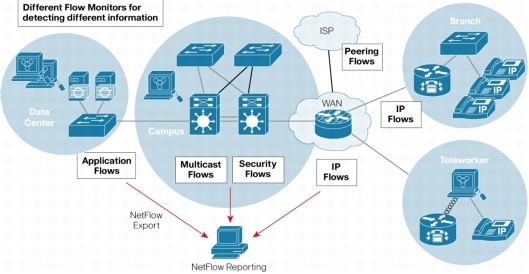
As shown in the following diagrams, different flows will be defined for detecting different information and used for different purpose.
Flexible NetFlow can track a wide range of packet information for Layer2, IPv4, IPv6 Flows.
• Source and destination Mac Addresses
• Source and destination IPv4 or IPv6 addresses
• Source and destination TCP/User Datagram Protocol (UDP) ports
• Type of service (ToS)
• DSCP
• Packet and byte counts
• Flow timestamps
• Input and output interface numbers
• TCP flags and encapsulated protocol (TCP/UDP) and individual TCP Flags
• Sections of packet for deep packet inspection
• All fields in IPv4 Header including IP-ID, TTL and others
• All fields in IPv6 Header including Flow Label, Option Header and others
• Routing information (next-hop address, source autonomous system (AS) number, destination AS number, source prefix mask, destination prefix mask, BGP Next Hop, BGP Policy Accounting traffic index)
In my environment, I am having Cisco-4510R+E with Supervisor 8-E, using ipbase cat4500es8-universalk9.SPA.03.03.01.XO.151-1.XO1.bin IOS file. There is no Netflow service card installed. But flexible netflow is supported
CS#show module
Chassis Type : WS-C4510R+E
Power consumed by backplane : 40 Watts
Mod Ports Card Type Model Serial No.
---+-----+--------------------------------------+------------------+-----------
1 48 10/100/1000BaseT EEE (RJ45) WS-X4748-RJ45-E CA1737L5CP
2 48 10/100/1000BaseT Premium POE E Series WS-X4748-RJ45V+E CA1746L5KJ
3 48 10/100/1000BaseT Premium POE E Series WS-X4748-RJ45V+E CA1746L5RN
4 48 10/100/1000BaseT (RJ45) WS-X4648-RJ45-E JA17410F8D
5 8 Sup 8-E 10GE (SFP+), 1000BaseX (SFP) WS-X45-SUP8-E CA1749L63E
7 48 10/100/1000BaseT (RJ45) WS-X4648-RJ45-E JA17410AF6
8 12 10GE SFP+ WS-X4712-SFP+E CA1741L4FU
9 48 10/100/1000BaseT (RJ45) WS-X4648-RJ45-E JA17410F1K
10 48 10/100/1000BaseT EEE (RJ45) WS-X4748-RJ45-E CA1806L2H6
M MAC addresses Hw Fw Sw Status
--+--------------------------------+---+------------+----------------+---------
1 885a.924.69c0 to 885a.9244.69ef 1.1 Ok
2 24e9.b34.9748 to 24e9.b3f4.9777 1.3 Ok
3 24e9.bf4.9988 to 24e9.b3f4.99b7 1.3 Ok
4 e4c7.2df.d9da to e4c7.22df.da09 2.1 Ok
5 24e9.3fb.a4c0 to 24e9.b3fb.a4c7 1.0 15.1(1r)SG1 03.03.01.XO Ok
7 e4c7.2df.b42a to e4c7.22df.b459 2.1 Ok
8 78da.e56.3ad0 to 78da.6e56.3adb 2.0 Ok
9 e4c7.2df.d01a to e4c7.22df.d049 2.1 Ok
10 7426.c47.9dcc to 7426.ac47.9dfb 1.2 Ok
Mod Redundancy role Operating mode Redundancy status
----+-------------------+-------------------+----------------------------------
5 Active Supervisor SSO Active
CS#sh verCisco IOS Software, IOS-XE Software, Catalyst 4500 L3 Switch Software (cat4500es8-UNIVERSALK9-M), Version 03.03.01.XO RELEASE SOFTWARE (fc1)Technical Support: http://www.cisco.com/techsupportCopyright (c) 1986-2014 by Cisco Systems, Inc.Compiled Wed 30-Apr-14 02:55 by prod_rel_teamThis simple sample will configure traditional NetFlow export using the new Flexible NetFlow CLI. The user will create the Flow Monitor and attaches the Flow Record and Flow Exporter to the Flow Monitor.
Cisco IOS-XE software, Copyright (c) 2005-2013 by cisco Systems, Inc.All rights reserved. Certain components of Cisco IOS-XE software arelicensed under the GNU General Public License ("GPL") Version 2.0. Thesoftware code licensed under GPL Version 2.0 is free software that comeswith ABSOLUTELY NO WARRANTY. You can redistribute and/or modify suchGPL code under the terms of GPL Version 2.0. For more details, see thedocumentation or "License Notice" file accompanying the IOS-XE software,or the applicable URL provided on the flyer accompanying the IOS-XEsoftware.
ROM: 15.1(1r)SG1CS uptime is 30 weeks, 4 days, 10 hours, 5 minutesUptime for this control processor is 30 weeks, 4 days, 10 hours, 6 minutesSystem returned to ROM by reloadSystem restarted at 16:18:25 UTC Mon Jul 7 2014System image file is "bootflash:/cat4500es8-universalk9.SPA.03.03.01.XO.151-1.XO1.bin"Jawa Revision 3, RadTrooper Revision 0x0.0x41, Conan Revision 0x1449
Last reload reason: Reload command
This product contains cryptographic features and is subject to UnitedStates and local country laws governing import, export, transfer anduse. Delivery of Cisco cryptographic products does not implythird-party authority to import, export, distribute or use encryption.Importers, exporters, distributors and users are responsible forcompliance with U.S. and local country laws. By using this product youagree to comply with applicable laws and regulations. If you are unableto comply with U.S. and local laws, return this product immediately.
A summary of U.S. laws governing Cisco cryptographic products may be found at:http://www.cisco.com/wwl/export/crypto/tool/stqrg.html
If you require further assistance please contact us by sending email to[email protected].
License Information for 'WS-X45-SUP8-E' License Level: ipbase Type: Permanent Next reboot license Level: ipbase
cisco WS-C4510R+E (P5040) processor (revision 2) with 4194304K bytes of physical memory.Processor board ID FXS1749Q1VP5040 CPU at 2.2GHz, Supervisor 8-ELast reset from Reload17 Virtual Ethernet interfaces336 Gigabit Ethernet interfaces20 Ten Gigabit Ethernet interfaces511K bytes of non-volatile configuration memory.
Configuration register is 0x2102
Step1: Configure Flow Record
flow record ipv4_record
match ipv4 protocol
match ipv4 source address
match ipv4 destination address
match transport source-port
match transport destination-port
collect ipv4 tos
collect transport tcp source-port
collect transport tcp destination-port
collect transport tcp flags
collect interface input
collect interface output
collect counter bytes
collect counter packets
collect timestamp sys-uptime first
collect timestamp sys-uptime last
Step2: Configure Flow Exporter
flow exporter flow1
description for vlan 1
destination 10.4.2.13
source Vlan1
transport udp 9995
template data timeout 60
Step3: Configure Flow Monitor
flow monitor main_monitor
exporter flow1
cache timeout active 30
record ipv4_record
Step4: Applying an IPv4 Flow Monitor to an Interface
interface GigabitEthernet1/4
ip flow monitor main_monitor input
end
Step5: Configure PRTG Server (10.4.2.13) to Receive the flow data on UDP port 9995
This Step is same as my previous post "Configure Netflow on network devices for PRTG Netflow Monitoring"Add a new Sensor at this Switch Device and put Vlan 1 ip address into Sendor IP. Receive NetFlow Packets on UDP port is 9995.
Step 6: Verify:
CS#show flow interface g1/4
Interface GigabitEthernet1/4
FNF: monitor: main_monitor
direction: Input
traffic(ip): on
CS#show flow monitor name main_monitor cache format record
Cache type: Normal
Cache size: 4096
Current entries: 451
High Watermark: 1024
Flows added: 681122
Flows aged: 680671
- Active timeout ( 30 secs) 51744
- Inactive timeout ( 15 secs) 628927
- Event aged 0
- Watermark aged 0
- Emergency aged 0
IPV4 SOURCE ADDRESS: 10.31.51.9
IPV4 DESTINATION ADDRESS: 10.4.1.15
TRNS SOURCE PORT: 52034
TRNS DESTINATION PORT: 1352
IP PROTOCOL: 6
tcp source port: 52034
tcp destination port: 1352
tcp flags: 0x18
interface input: Gi1/4
interface output: Gi10/24
counter bytes: 7060
counter packets: 20
timestamp first: 03:05:59.637
timestamp last: 03:06:24.637
ip tos: 0x00
Notes:
1. The Flexible NetFlow in Cisco 4500 requires you to configure your own “record” since there are no predefined ones available like in some other IOS.2. Interface Flow monitor output does not support on Cisco 4500 switch yet.
CS(config-if)#ip flow monitor main_monitor output3. Traditional Netflow V5 and V9 configuration:
% Flow Monitor: 'main_monitor' could not be added to interface due to invalid sub-traffic type: 0
This feature is only available if the NetFlow Services Card (WS-F4531) is present. The modules can be viewed by executing the “show module” command.
For example:
Mod Submodule Model Serial No. Hw Status
----+-----------------------+-----------------+------------+----+---------
1 Netflow Services Card WS-F4531 JAB062209CG 0.2 Ok
2 Netflow Services Card WS-F4531 JAB062209AG 0.2 Ok
The basic command set is as follows:
ip flow ingress infer-fields
ip flow-cache timeout active 1
ip flow-export source Loopback0
ip flow-export version 5
ip flow-export destination x.x.x.x 2059
Reference:
1. Configuring Flexible NetFlow Export on Cisco Routers2. Cisco IOS Flexible NetFlow Technology Q&A
3. What is Flexible NetFlow part 1 of 3









ReplyDeleteI actually enjoyed reading through this posting.Many thanks.
Setup HP Envy
Is there a reason for duplicating the TCP source and destination ports in the flow record?
ReplyDeleteAre you talking about following configuration?
Deleteflow record ipv4_record
match ipv4 protocol
match ipv4 source address
match ipv4 destination address
match transport source-port
match transport destination-port
collect ipv4 tos
collect transport tcp source-port
collect transport tcp destination-port
collect transport tcp flags
collect interface input
collect interface output
collect counter bytes
collect counter packets
collect timestamp sys-uptime first
collect timestamp sys-uptime last
This configuration gives a PRTG graph only for inbound traffica right? Is there a way for graph inbound and outbound traffic in the same graph?
ReplyDeleteRegards.
Hello.
ReplyDeleteI understand that this configuration gives a PRTG graphic for inbound traffic. Is there a way to graph inbound and outbound traffic in the same graph?
Regards.
Hi Starrk,
DeleteTo be honest, I am not sure if it is possible, but I doubt it is possible without any specific support from PRTG.