Once it has been determined whether a SOC 1 or SOC 2 is required (or both) and whether a type 1 or type 2 report will be the first report, the service organization then needs to prepare for the examination. A readiness assessment can be beneficial to validate that controls are in place to meet the control objectives or control criteria.
SOC 1 vs SOC 2 Reports
SOC 1 Reports
A SOC 1 report falls under the Statement on Standards for Attestation Engagements (SSAE) 18 AT-C 320 (formerly SSAE 16 or AT 801). It is named a SOC 1 versus the name of the standard (reports are NOT called SSAE 18s). A SOC 1 report has a financial focus that includes a service organization’s controls relevant to an audit of a service organization’s client’s financials. The service organization (with the assistance of the auditors) will figure out what the key control objectives are for the services they are providing to their clients. Control objectives will be related to both information technology processes and business processes at the service organization.SOC 2 Reports
A SOC 2 report also falls under the SSAE 18 standard AT-C 105 and the SSAE 21 standard AT-C 205. The SOC 2 report includes a service organization’s controls that are outlined by the AICPA’s Trust Services Criteria (TSC), and that are relevant to its services, operations, and compliance. There are five available criteria that include security, availability, processing integrity, confidentiality, and privacy. The security criteria, which are also referred to as the common criteria, are the only required criteria to be included in the SOC 2. The difference between SOC 1 and SOC 2 in reference to these controls and criteria are as follows:- In a SOC 2, controls meeting the criteria are identified and tested.
- In a SOC 1, controls meeting the identified control objectives are tested.
In summary of the comparison of SOC 1 vs. SOC 2 reports:
- The SOC 1 addresses internal control relevant to a service organization’s client’s financial statements.
- The SOC 2 report addresses a service organization’s controls that are relevant to its operations and compliance, as outlined by the AICPA’s Trust Services Criteria (TSCs).
A type II examination also looks at the design of controls, but additionally includes testing of the operating effectiveness of controls over a period of time. A type II report covers a minimum of six months (there are exceptions to this, but as a general rule six months is the minimum). The goal of an organization is to have the type II cover 12 months and then have annual type II reports to have continual coverage of controls.
If a service organization needs to get an initial report to a client or prospect quickly, the initial report can be a type I to show evidence of controls in place. If there is not a rush to get an initial report out quickly, we generally recommend starting with a type II.
For each trust services criteria (TSC) you choose to cover with your SOC 2 audit, there is a list of requirements (or “criteria”) that your auditor will assess your compliance against. Controls are what you implement to meet those requirements, and the auditor is attesting to the design and/or operating effectiveness of those controls.
If your audit covers security only, your auditor will typically be looking for 80-100 controls. As you add more TSCs to your audit (privacy, availability, processing integrity, or confidentiality), each will come with its own set of requirements that your business has to meet and controls you design and implement to satisfy them.
SOC 2 Trust Services Criteria
1 Security
Also known as the “common criteria,” security is the foundational criteria required in a SOC 2 assessment. Security focuses on the protection of information and systems against unauthorized access. It tests if your customers’ information is protected at all times (collection, creation, use, processing, transmission, and storage) along with the systems that handle it.
Security is required in any SOC audit because it not only sets overarching security standards for your company, but also overlaps with the others: setting security controls for availability, confidentiality, privacy, and processing integrity.
For example, the criteria related to risk management apply to four of the criteria (security, processing integrity, confidentiality, and availability). The common criteria establish the criteria common to all the trust services criteria and the comprehensive set of criteria for the security criteria.When a service organization’s client wants to know their information/data is secure and protected, they are likely interested in the security criteria. This criteria is comprehensive enough that including it in the scope of the examination alone will likely be enough for service organization’s clients to get the assurance they need with respect to the security of their information/data.
2 Availability
Availability addresses network performance, downtime, security event handling, etc. This criterion makes sure your systems are secure and available for customers to use when they expect to. This is important for startups that promise customers access to their data and your services at key times.
For example, your team worked hard to get your platform’s uptime to 99.31%. By validating your uptime and other availability considerations with the availability criteria, you’re further demonstrating your reliability to your customers.
3 Confidentiality
Confidentiality addresses the handling and protection of information, personal or not, that you’ve agreed to designate confidential and secure for your customers (think of proprietary information like business plans, financial or transaction details, legal documents, etc.)
In addition to the protections outlined in the security criteria, the confidentiality criteria provide guidance for identifying, protecting, and destroying confidential information.
For example, your platform manages a customer’s documentation about their trade secrets and intellectual property. For obvious reasons, they only want people within the company (and only some of them) to have access to this sensitive information. The confidentiality criteria signal that you’re set up to protect that information and secure access as desired. It also shows that you’re set up to appropriately destroy confidential information if, say, the customer decides to stop using your platform.
4 Privacy
Privacy addresses the secure collecting, storing, and handling of personal information, like name, address, email, Social Security number, or other identification info, purchase history, criminal history, etc.
Similar to confidentiality, the privacy criteria test whether you effectively protect your customers’ personal information. Confidentiality, on the other hand, applies to any information you agreed to keep confidential.
5 Processing Integrity
Processing integrity addresses processing errors and how long it takes to detect and fix them, as well as the incident-free storage and maintenance of data. It also makes sure that any system inputs and outputs are free from unauthorized assessor manipulation. This criterion helps businesses make sure their services are delivered in an accurate, authorized, and timely manner.
For example, the processing integrity criteria demonstrate to customers that your data, processes, and system work as intended, so they don’t have to worry about inaccuracies, delays, errors and whether only authorized people can use your product.
SOC 2 Controls / Criteria List
In simplest terms, a control is a system, process, or policy you put in place in order to mitigate a bad thing from happening. A bicycle helmet is a control to help avoid a head injury!While there are many controls associated with each of the five TSCs, controls associated with the common criteria include common IT general controls.
1 Control Environment
These SOC 2 controls relate to a commitment to integrity and ethical values.
Involvement of the board of directors and senior management’s oversight relating to the development and performance of internal control.
Hold individuals accountable for their internal control responsibilities in the pursuit of objectives.
2 Communication and Information
This includes SOC 2 controls related to the internal and external use of quality information to support the functioning of internal control.
3 Risk Assessment
This requests the identification and assessment of risk relating to objectives, including fraud.
4 Monitoring Activities
Place controls related to the performance of ongoing and separate evaluations to determine deficiencies of controls and communicate those to the correct parties.
5 Control Activities
These relate to the control activities contributing to risk mitigation and policy and procedure establishment.
6 Logical and Physical Access Controls
Related to the implementation of logical access security software, infrastructure, and architectures over protected information assets to protect them from security events to meet its objectives.
- Issuing of credentials to new internal and external users
- Authorization, modification, or removal of access to data, software, functions, and other protected information assets based on roles, responsibilities, or the system design
- Restriction of physical access to facilities and protected information assets to authorized personnel to meet its objectives
- Implementation of controls to prevent or detect and act upon the introduction of unauthorized or malicious software to meet its objectives.
7 System Operations
SOC 2 controls related to the use of detection and monitoring procedures to identify (1) changes to configurations that result in the introduction of new vulnerabilities and (2) susceptibilities to newly-discovered vulnerabilities.
- Response to identified security incidents by executing a defined incident response program to understand, contain, remediate, and communicate security incidents, as appropriate.
- Monitoring of system components and the operation of those components for anomalies indicative of malicious acts, natural disasters, and errors
8 Change Management
Controls related to the authorization, design, development, testing, approval, and implementation of changes to infrastructure, data, software, and procedures to meet its objectives.
9 Risk Mitigation
Identifies, selects, and develops risk mitigation activities for risks arising from potential business disruptions.
Additional SOC 2 Criteria for Privacy, Processing Integrity, Confidentiality, Availability
In addition to the requirements attached to Security, businesses should fulfill the controls for other relevant categories based on the commitments they make to their customers.
Find examples of additional SOC 2 control categories and control types that satisfy these categories below.
10 Privacy:
Provides notice of privacy practices to relevant parties.
The notice is updated and communicated in a timely manner, including changes in the use of personal information.
11 Processing Integrity:
Obtains or generates, uses, and communicates relevant, quality information regarding the SOC 2 objectives related to processing.
This includes definitions of processed data, and product and service specifications, to support the use of products and services.
12 Confidentiality:
Identifies and maintains confidential information to meet SOC 2 objectives related to confidentiality.
- Retention and Classification
- Disposal of Information
13 Availability:
Maintains, monitors, and evaluates current processing capacity and use of system components like infrastructure, data, and software.
- System Capacity
Maintaining processing capacity and use of system components (infrastructure, data, and software) to manage demand and enable the implementation of additional capacity to help meet objectives.
- Backups and evironmental controls
- Recovery controls
SOC 2 Control Details
# | Category | Trust ID | Point of Focus | Trust Criteria |
1 | Control Environment | CC1.1 | | COSO Principle 1: The entity demonstrates a commitment to integrity and ethical values. |
2 | Control Environment | CC1.1 | 1 | Sets the Tone at the Top—The board of directors and management, at all levels, demonstrate through their directives, actions, and behavior the importance of integrity and ethical values to support the functioning of the system of internal control. |
3 | Control Environment | CC1.1 | 2 | Establishes Standards of Conduct—The expectations of the board of directors and senior management concerning integrity and ethical values are defined in the entity’s standards of conduct and understood at all levels of the entity and by outsourced service providers and business partners. |
4 | Control Environment | CC1.1 | 3 | Evaluates Adherence to Standards of Conduct—Processes are in place to evaluate the performance of individuals and teams against the entity’s expected standards of conduct. |
5 | Control Environment | CC1.1 | 4 | Addresses Deviations in a Timely Manner—Deviations from the entity’s expected standards of conduct are identified and remedied in a timely and consistent manner. |
6 | Control Environment | CC1.1 | 5 | Considers Contractors and Vendor Employees in Demonstrating Its Commitment—Management and the board of directors consider the use of contractors and vendor employees in its processes for establishing standards of conduct, evaluating adherence to those standards, and addressing deviations in a timely manner. |
7 | Control Environment | CC1.2 | | COSO Principle 2: The board of directors demonstrates independence from management and exercises oversight of the development and performance of internal control. |
8 | Control Environment | CC1.2 | 1 | Establishes Oversight Responsibilities—The board of directors identifies and accepts its oversight responsibilities in relation to established requirements and expectations. |
9 | Control Environment | CC1.2 | 2 | Applies Relevant Expertise—The board of directors defines, maintains, and periodically evaluates the skills and expertise needed among its members to enable them to ask probing questions of senior management and take commensurate action. |
10 | Control Environment | CC1.2 | 3 | Operates Independently—The board of directors has sufficient members who are independent from management and objective in evaluations and decision making. |
11 | Control Environment | CC1.2 | 4 | Supplements Board Expertise—The board of directors supplements its expertise relevant to security, availability, processing integrity, confidentiality, and privacy, as needed, through the use of a subcommittee or consultants. |
12 | Control Environment | CC1.3 | | COSO Principle 3: Management establishes, with board oversight, structures, reporting lines, and appropriate authorities and responsibilities in the pursuit of objectives. |
13 | Control Environment | CC1.3 | 1 | Considers All Structures of the Entity—Management and the board of directors consider the multiple structures used (including operating units, legal entities, geographic distribution, and outsourced service providers) to support the achievement of objectives. |
14 | Control Environment | CC1.3 | 2 | Establishes Reporting Lines—Management designs and evaluates lines of reporting for each entity structure to enable execution of authorities and responsibilities and flow of information to manage the activities of the entity. |
15 | Control Environment | CC1.3 | 3 | Defines, Assigns, and Limits Authorities and Responsibilities—Management and the board of directors delegate authority, define responsibilities, and use appropriate processes and technology to assign responsibility and segregate duties as necessary at the various levels of the organization. |
16 | Control Environment | CC1.3 | 4 | Addresses Specific Requirements When Defining Authorities and Responsibilities—Management and the board of directors consider requirements relevant to security, availability, processing integrity, confidentiality, and privacy when defining authorities and responsibilities. |
17 | Control Environment | CC1.3 | 5 | Considers Interactions With External Parties When Establishing Structures, Reporting Lines, Authorities, and Responsibilities—Management and the board of directors consider the need for the entity to interact with and monitor the activities of external parties when establishing structures, reporting lines, authorities, and responsibilities. |
18 | Control Environment | CC1.4 | | COSO Principle 4: The entity demonstrates a commitment to attract, develop, and retain competent individuals in alignment with objectives. |
19 | Control Environment | CC1.4 | 1 | Establishes Policies and Practices—Policies and practices reflect expectations of competence necessary to support the achievement of objectives. |
20 | Control Environment | CC1.4 | 2 | Evaluates Competence and Addresses Shortcomings—The board of directors and management evaluate competence across the entity and in outsourced service providers in relation to established policies and practices and act as necessary to address shortcomings. |
21 | Control Environment | CC1.4 | 3 | Attracts, Develops, and Retains Individuals—The entity provides the mentoring and training needed to attract, develop, and retain sufficient and competent personnel and outsourced service providers to support the achievement of objectives. |
22 | Control Environment | CC1.4 | 4 | Plans and Prepares for Succession—Senior management and the board of directors develop contingency plans for assignments of responsibility important for internal control. |
23 | Control Environment | CC1.4 | 5 | Considers the Background of Individuals—The entity considers the background of potential and existing personnel, contractors, and vendor employees when determining whether to employ and retain the individuals. |
24 | Control Environment | CC1.4 | 6 | Considers the Technical Competency of Individuals—The entity considers the technical competency of potential and existing personnel, contractors, and vendor employees when determining whether to employ and retain the individuals. |
25 | Control Environment | CC1.4 | 7 | Provides Training to Maintain Technical Competencies— The entity provides training programs, including continuing education and training, to ensure skill sets and technical competency of existing personnel, contractors, and vendor employees are developed and maintained. |
26 | Control Environment | CC1.5 | | COSO Principle 5: The entity holds individuals accountable for their internal control responsibilities in the pursuit of objectives. |
27 | Control Environment | CC1.5 | 1 | Enforces Accountability Through Structures, Authorities, and Responsibilities—Management and the board of directors establish the mechanisms to communicate and hold individuals accountable for performance of internal control responsibilities across the entity and implement corrective action as necessary. |
28 | Control Environment | CC1.5 | 2 | Establishes Performance Measures, Incentives, and Rewards—Management and the board of directors establish performance measures, incentives, and other rewards appropriate for responsibilities at all levels of the entity, reflecting appropriate dimensions of performance and expected standards of conduct, and considering the achievement of both short-term and longer-term objectives. |
29 | Control Environment | CC1.5 | 3 | Evaluates Performance Measures, Incentives, and Rewards for Ongoing Relevance—Management and the board of directors align incentives and rewards with the fulfillment of internal control responsibilities in the achievement of objectives. |
30 | Control Environment | CC1.5 | 4 | Considers Excessive Pressures—Management and the board of directors evaluate and adjust pressures associated with the achievement of objectives as they assign responsibilities, develop performance measures, and evaluate performance. |
31 | Control Environment | CC1.5 | 5 | Evaluates Performance and Rewards or Disciplines Individuals—Management and the board of directors evaluate performance of internal control responsibilities, including adherence to standards of conduct and expected levels of competence, and provide rewards or exercise disciplinary action, as appropriate. |
32 | Communication and Information | CC2.1 | | COSO Principle 13: The entity obtains or generates and uses relevant, quality information to support the functioning of internal control. |
33 | Communication and Information | CC2.1 | 1 | Identifies Information Requirements—A process is in place to identify the information required and expected to support the functioning of the other components of internal control and the achievement of the entity’s objectives. |
34 | Communication and Information | CC2.1 | 2 | Captures Internal and External Sources of Data—Information systems capture internal and external sources of data. |
35 | Communication and Information | CC2.1 | 3 | Processes Relevant Data Into Information—Information systems process and transform relevant data into information. |
36 | Communication and Information | CC2.1 | 4 | Maintains Quality Throughout Processing—Information systems produce information that is timely, current, accurate, complete, accessible, protected, verifiable, and retained. Information is reviewed to assess its relevance in supporting the internal control components. |
37 | Communication and Information | CC2.2 | | COSO Principle 14: The entity internally communicates information, including objectives and responsibilities for internal control, necessary to support the functioning of internal control. |
38 | Communication and Information | CC2.2 | 1 | Communicates Internal Control Information—A process is in place to communicate required information to enable all personnel to understand and carry out their internal control responsibilities. |
39 | Communication and Information | CC2.2 | 2 | Communicates With the Board of Directors—Communication exists between management and the board of directors so that both have information needed to fulfill their roles with respect to the entity’s objectives. |
40 | Communication and Information | CC2.2 | 3 | Provides Separate Communication Lines—Separate communication channels, such as whistle-blower hotlines, are in place and serve as fail-safe mechanisms to enable anonymous or confidential communication when normal channels are inoperative or ineffective. |
41 | Communication and Information | CC2.2 | 4 | Selects Relevant Method of Communication—The method of communication considers the timing, audience, and nature of the information. |
42 | Communication and Information | CC2.2 | 5 | Communicates Responsibilities—Entity personnel with responsibility for designing, developing, implementing, operating, maintaining, or monitoring system controls receive communications about their responsibilities, including changes in their responsibilities, and have the information necessary to carry out those responsibilities. |
43 | Communication and Information | CC2.2 | 6 | Communicates Information on Reporting Failures, Incidents, Concerns, and Other Matters—Entity personnel are provided with information on how to report systems failures, incidents, concerns, and other complaints to personnel. |
44 | Communication and Information | CC2.2 | 7 | Communicates Objectives and Changes to Objectives —The entity communicates its objectives and changes to those objectives to personnel in a timely manner. |
45 | Communication and Information | CC2.2 | 8 | Communicates Information to Improve Security Knowledge and Awareness—The entity communicates information to improve security knowledge and awareness and to model appropriate security behaviors to personnel through a security awareness training program. |
46 | Communication and Information | CC2.2 | 9 | Communicates Information About System Operation and Boundaries—The entity prepares and communicates information about the design and operation of the system and its boundaries to authorized personnel to enable them to understand their role in the system and the results of system operation. |
47 | Communication and Information | CC2.2 | 10 | Communicates System Objectives—The entity communicates its objectives to personnel to enable them to carry out their responsibilities. |
48 | Communication and Information | CC2.2 | 11 | Communicates System Changes—System changes that affect responsibilities or the achievement of the entity's objectives are communicated in a timely manner. |
49 | Communication and Information | CC2.3 | | COSO Principle 15: The entity communicates with external parties regarding matters affecting the functioning of internal control. |
50 | Communication and Information | CC2.3 | 1 | Communicates to External Parties—Processes are in place to communicate relevant and timely information to external parties, including shareholders, partners, owners, regulators, customers, financial analysts, and other external parties. |
51 | Communication and Information | CC2.3 | 2 | Enables Inbound Communications—Open communication channels allow input from customers, consumers, suppliers, external auditors, regulators, financial analysts, and others, providing management and the board of directors with relevant information. |
52 | Communication and Information | CC2.3 | 3 | Communicates With the Board of Directors—Relevant information resulting from assessments conducted by external parties is communicated to the board of directors. |
53 | Communication and Information | CC2.3 | 4 | Provides Separate Communication Lines—Separate communication channels, such as whistle-blower hotlines, are in place and serve as fail-safe mechanisms to enable anonymous or confidential communication when normal channels are inoperative or ineffective. |
54 | Communication and Information | CC2.3 | 5 | Selects Relevant Method of Communication—The method of communication considers the timing, audience, and nature of the communication and legal, regulatory, and fiduciary requirements and expectations. |
55 | Communication and Information | CC2.3 | 6 | Communicates Objectives Related to Confidentiality and Changes to Objectives— The entity communicates, to external users, vendors, business partners and others whose products and services are part of the system, objectives and changes to objectives related to confidentiality. |
56 | Communication and Information | CC2.3 | 7 | Communicates Objectives Related to Privacy and Changes to Objectives—The entity communicates, to external users, vendors, business partners and others whose products and services are part of the system, objectives related to privacy and changes to those objectives. |
57 | Communication and Information | CC2.3 | 8 | Communicates Information About System Operation and Boundaries—The entity prepares and communicates information about the design and operation of the system and its boundaries to authorized external users to permit users to understand their role in the system and the results of system operation. |
58 | Communication and Information | CC2.3 | 9 | Communicates System Objectives—The entity communicates its system objectives to appropriate external users. |
59 | Communication and Information | CC2.3 | 10 | Communicates System Responsibilities—External users with responsibility for designing, developing, implementing, operating, maintaining, and monitoring system controls receive communications about their responsibilities and have the information necessary to carry out those responsibilities. |
60 | Communication and Information | CC2.3 | 11 | Communicates Information on Reporting System Failures, Incidents, Concerns, and Other Matters—External users are provided with information on how to report systems failures, incidents, concerns, and other complaints to appropriate personnel. |
61 | Risk Assessment | CC3.1 | | COSO Principle 6: The entity specifies objectives with sufficient clarity to enable the identification and assessment of risks relating to objectives. |
62 | Risk Assessment | CC3.1 | 1 | Reflects Management's Choices—Operations objectives reflect management's choices about structure, industry considerations, and performance of the entity. |
63 | Risk Assessment | CC3.1 | 2 | Considers Tolerances for Risk—Management considers the acceptable levels of variation relative to the achievement of operations objectives. |
64 | Risk Assessment | CC3.1 | 3 | Includes Operations and Financial Performance Goals—The organization reflects the desired level of operations and financial performance for the entity within operations objectives. |
65 | Risk Assessment | CC3.1 | 4 | Forms a Basis for Committing of Resources—Management uses operations objectives as a basis for allocating resources needed to attain desired operations and financial performance. |
66 | Risk Assessment | CC3.1 | 5 | Complies With Applicable Accounting Standards—Financial reporting objectives are consistent with accounting principles suitable and available for that entity. The accounting principles selected are appropriate in the circumstances. |
67 | Risk Assessment | CC3.1 | 6 | Considers Materiality—Management considers materiality in financial statement presentation. |
68 | Risk Assessment | CC3.1 | 7 | Reflects Entity Activities—External reporting reflects the underlying transactions and events to show qualitative characteristics and assertions. |
69 | Risk Assessment | CC3.1 | 8 | Complies With Externally Established Frameworks—Management establishes objectives consistent with laws and regulations or standards and frameworks of recognized external organizations. |
70 | Risk Assessment | CC3.1 | 9 | Considers the Required Level of Precision—Management reflects the required level of precision and accuracy suitable for user needs and based on criteria established by third parties in nonfinancial reporting. |
71 | Risk Assessment | CC3.1 | 10 | Reflects Entity Activities—External reporting reflects the underlying transactions and events within a range of acceptable limits. |
72 | Risk Assessment | CC3.1 | 11 | Reflects Management's Choices—Internal reporting provides management with accurate and complete information regarding management's choices and information needed in managing the entity. |
73 | Risk Assessment | CC3.1 | 12 | Considers the Required Level of Precision—Management reflects the required level of precision and accuracy suitable for user needs in nonfinancial reporting objectives and materiality within financial reporting objectives. |
74 | Risk Assessment | CC3.1 | 13 | Reflects Entity Activities—Internal reporting reflects the underlying transactions and events within a range of acceptable limits. |
75 | Risk Assessment | CC3.1 | 14 | Reflects External Laws and Regulations—Laws and regulations establish minimum standards of conduct, which the entity integrates into compliance objectives. |
76 | Risk Assessment | CC3.1 | 15 | Considers Tolerances for Risk—Management considers the acceptable levels of variation relative to the achievement of operations objectives. |
77 | Risk Assessment | CC3.1 | 16 | Establishes Sub-objectives to Support Objectives—Management identifies sub-objectives related to security, availability, processing integrity, confidentiality, and privacy to support the achievement of the entity’s objectives related to reporting, operations, and compliance. |
78 | Risk Assessment | CC3.2 | | COSO Principle 7: The entity identifies risks to the achievement of its objectives across the entity and analyzes risks as a basis for determining how the risks should be managed. |
79 | Risk Assessment | CC3.2 | 1 | Includes Entity, Subsidiary, Division, Operating Unit, and Functional Levels—The entity identifies and assesses risk at the entity, subsidiary, division, operating unit, and functional levels relevant to the achievement of objectives. |
80 | Risk Assessment | CC3.2 | 2 | Analyzes Internal and External Factors—Risk identification considers both internal and external factors and their impact on the achievement of objectives. |
81 | Risk Assessment | CC3.2 | 3 | Involves Appropriate Levels of Management—The entity puts into place effective risk assessment mechanisms that involve appropriate levels of management. |
82 | Risk Assessment | CC3.2 | 4 | Estimates Significance of Risks Identified—Identified risks are analyzed through a process that includes estimating the potential significance of the risk. |
83 | Risk Assessment | CC3.2 | 5 | Determines How to Respond to Risks—Risk assessment includes considering how the risk should be managed and whether to accept, avoid, reduce, or share the risk. |
84 | Risk Assessment | CC3.2 | 6 | Identifies and Assesses Criticality of Information Assets and Identifies Threats and Vulnerabilities—The entity's risk identification and assessment process includes (1) identifying information assets, including physical devices and systems, virtual devices, software, data and data flows, external information systems, and organizational roles; (2) assessing the criticality of those information assets; (3) identifying the threats to the assets from intentional (including malicious) and unintentional acts and environmental events; and (4) identifying the vulnerabilities of the identified assets. |
85 | Risk Assessment | CC3.2 | 7 | Analyzes Threats and Vulnerabilities From Vendors, Business Partners, and Other Parties—The entity's risk assessment process includes the analysis of potential threats and vulnerabilities arising from vendors providing goods and services, as well as threats and vulnerabilities arising from business partners, customers, and others with access to the entity's information systems. |
86 | Risk Assessment | CC3.2 | 8 | Considers the Significance of the Risk—The entity’s consideration of the potential significance of the identified risks includes (1) determining the criticality of identified assets in meeting objectives; (2) assessing the impact of identified threats and vulnerabilities in meeting objectives; (3) assessing the likelihood of identified threats; and (4) determining the risk associated with assets based on asset criticality, threat impact, and likelihood. |
87 | Risk Assessment | CC3.3 | | COSO Principle 8: The entity considers the potential for fraud in assessing risks to the achievement of objectives |
88 | Risk Assessment | CC3.3 | 1 | Considers Various Types of Fraud—The assessment of fraud considers fraudulent reporting, possible loss of assets, and corruption resulting from the various ways that fraud and misconduct can occur. |
89 | Risk Assessment | CC3.3 | 2 | Assesses Incentives and Pressures—The assessment of fraud risks considers incentives and pressures. |
90 | Risk Assessment | CC3.3 | 3 | Assesses Opportunities—The assessment of fraud risk considers opportunities for unauthorized acquisition, use, or disposal of assets, altering the entity’s reporting records, or committing other inappropriate acts. |
91 | Risk Assessment | CC3.3 | 4 | Assesses Attitudes and Rationalizations—The assessment of fraud risk considers how management and other personnel might engage in or justify inappropriate actions. |
92 | Risk Assessment | CC3.3 | 5 | Considers the Risks Related to the Use of IT and Access to Information—The assessment of fraud risks includes consideration of threats and vulnerabilities that arise specifically from the use of IT and access to information. |
93 | Risk Assessment | CC3.4 | | COSO Principle 9: The entity identifies and assesses changes that could significantly impact the system of internal control. |
94 | Risk Assessment | CC3.4 | 1 | Assesses Changes in the External Environment—The risk identification process considers changes to the regulatory, economic, and physical environment in which the entity operates. |
95 | Risk Assessment | CC3.4 | 2 | Assesses Changes in the Business Model—The entity considers the potential impacts of new business lines, dramatically altered compositions of existing business lines, acquired or divested business operations on the system of internal control, rapid growth, changing reliance on foreign geographies, and new technologies. |
96 | Risk Assessment | CC3.4 | 3 | Assesses Changes in Leadership—The entity considers changes in management and respective attitudes and philosophies on the system of internal control. |
97 | Risk Assessment | CC3.4 | 4 | Assess Changes in Systems and Technology—The risk identification process considers changes arising from changes in the entity’s systems and changes in the technology environment. |
98 | Risk Assessment | CC3.4 | 5 | Assess Changes in Vendor and Business Partner Relationships—The risk identification process considers changes in vendor and business partner relationships. |
99 | Monitoring Activities | CC4.1 | | COSO Principle 16: The entity selects, develops, and performs ongoing and/or separate evaluations to ascertain whether the components of internal control are present and functioning. |
100 | Monitoring Activities | CC4.1 | 1 | Considers a Mix of Ongoing and Separate Evaluations—Management includes a balance of ongoing and separate evaluations. |
101 | Monitoring Activities | CC4.1 | 2 | Considers Rate of Change—Management considers the rate of change in business and business processes when selecting and developing ongoing and separate evaluations. |
102 | Monitoring Activities | CC4.1 | 3 | Establishes Baseline Understanding—The design and current state of an internal control system are used to establish a baseline for ongoing and separate evaluations. |
103 | Monitoring Activities | CC4.1 | 4 | Uses Knowledgeable Personnel—Evaluators performing ongoing and separate evaluations have sufficient knowledge to understand what is being evaluated. |
104 | Monitoring Activities | CC4.1 | 5 | Integrates With Business Processes—Ongoing evaluations are built into the business processes and adjust to changing conditions. |
105 | Monitoring Activities | CC4.1 | 6 | Adjusts Scope and Frequency—Management varies the scope and frequency of separate evaluations depending on risk. |
106 | Monitoring Activities | CC4.1 | 7 | Objectively Evaluates—Separate evaluations are performed periodically to provide objective feedback. |
107 | Monitoring Activities | CC4.1 | 8 | Considers Different Types of Ongoing and Separate Evaluations—Management uses a variety of different types of ongoing and separate evaluations, including penetration testing, independent certification made against established specifications (for example, ISO certifications), and internal audit assessments. |
108 | Monitoring Activities | CC4.2 | | COSO Principle 17: The entity evaluates and communicates internal control deficiencies in a timely manner to those parties responsible for taking corrective action, including senior management and the board of directors, as appropriate. |
109 | Monitoring Activities | CC4.2 | 1 | Assesses Results—Management and the board of directors, as appropriate, assess results of ongoing and separate evaluations. |
110 | Monitoring Activities | CC4.2 | 2 | Communicates Deficiencies—Deficiencies are communicated to parties responsible for taking corrective action and to senior management and the board of directors, as appropriate. |
111 | Monitoring Activities | CC4.2 | 3 | Monitors Corrective Action—Management tracks whether deficiencies are remedied on a timely basis. |
112 | Control Activities | CC5.1 | | COSO Principle 10: The entity selects and develops control activities that contribute to the mitigation of risks to the achievement of objectives to acceptable levels |
113 | Control Activities | CC5.1 | 1 | Integrates With Risk Assessment—Control activities help ensure that risk responses that address and mitigate risks are carried out. |
114 | Control Activities | CC5.1 | 2 | Considers Entity-Specific Factors—Management considers how the environment, complexity, nature, and scope of its operations, as well as the specific characteristics of its organization, affect the selection and development of control activities. |
115 | Control Activities | CC5.1 | 3 | Determines Relevant Business Processes—Management determines which relevant business processes require control activities. |
116 | Control Activities | CC5.1 | 4 | Evaluates a Mix of Control Activity Types—Control activities include a range and variety of controls and may include a balance of approaches to mitigate risks, considering both manual and automated controls, and preventive and detective controls. |
117 | Control Activities | CC5.1 | 5 | Considers at What Level Activities Are Applied—Management considers control activities at various levels in the entity. |
118 | Control Activities | CC5.1 | 6 | Addresses Segregation of Duties—Management segregates incompatible duties, and where such segregation is not practical, management selects and develops alternative control activities. |
119 | Control Activities | CC5.2 | | COSO Principle 11: The entity also selects and develops general control activities over technology to support the achievement of objectives. |
120 | Control Activities | CC5.2 | 1 | Determines Dependency Between the Use of Technology in Business Processes and Technology General Controls—Management understands and determines the dependency and linkage between business processes, automated control activities, and technology general controls. |
121 | Control Activities | CC5.2 | 2 | Establishes Relevant Technology Infrastructure Control Activities—Management selects and develops control activities over the technology infrastructure, which are designed and implemented to help ensure the completeness, accuracy, and availability of technology processing. |
122 | Control Activities | CC5.2 | 3 | Establishes Relevant Security Management Process Controls Activities—Management selects and develops control activities that are designed and implemented to restrict technology access rights to authorized users commensurate with their job responsibilities and to protect the entity’s assets from external threats. |
123 | Control Activities | CC5.2 | 4 | Establishes Relevant Technology Acquisition, Development, and Maintenance Process Control Activities—Management selects and develops control activities over the acquisition, development, and maintenance of technology and its infrastructure to achieve management’s objectives. |
124 | Control Activities | CC5.3 | | COSO Principle 12: The entity deploys control activities through policies that establish what is expected and in procedures that put policies into action. |
125 | Control Activities | CC5.3 | 1 | Establishes Policies and Procedures to Support Deployment of Management ‘s Directives—Management establishes control activities that are built into business processes and employees’ day-to-day activities through policies establishing what is expected and relevant procedures specifying actions. |
126 | Control Activities | CC5.3 | 2 | Establishes Responsibility and Accountability for Executing Policies and Procedures—Management establishes responsibility and accountability for control activities with management (or other designated personnel) of the business unit or function in which the relevant risks reside. |
127 | Control Activities | CC5.3 | 3 | Performs in a Timely Manner—Responsible personnel perform control activities in a timely manner as defined by the policies and procedures. |
128 | Control Activities | CC5.3 | 4 | Takes Corrective Action—Responsible personnel investigate and act on matters identified as a result of executing control activities. |
129 | Control Activities | CC5.3 | 5 | Performs Using Competent Personnel—Competent personnel with sufficient authority perform control activities with diligence and continuing focus. |
130 | Control Activities | CC5.3 | 6 | Reassesses Policies and Procedures—Management periodically reviews control activities to determine their continued relevance and refreshes them when necessary. |
131 | Logical and Physical Access Controls | CC6.1 | | The entity implements logical access security software, infrastructure, and architectures over protected information assets to protect them from security events to meet the entity’s objectives |
132 | Logical and Physical Access Controls | CC6.1 | 1 | Identifies and Manages the Inventory of Information Assets—The entity identifies, inventories, classifies, and manages information assets. |
133 | Logical and Physical Access Controls | CC6.1 | 2 | Restricts Logical Access—Logical access to information assets, including hardware, data (at-rest, during processing, or in transmission), software, administrative authorities, mobile devices, output, and offline system components is restricted through the use of access control software and rule sets. |
134 | Logical and Physical Access Controls | CC6.1 | 3 | Identifies and Authenticates Users—Persons, infrastructure and software are identified and authenticated prior to accessing information assets, whether locally or remotely. |
135 | Logical and Physical Access Controls | CC6.1 | 4 | Considers Network Segmentation—Network segmentation permits unrelated portions of the entity's information system to be isolated from each other. |
136 | Logical and Physical Access Controls | CC6.1 | 5 | Manages Points of Access—Points of access by outside entities and the types of data that flow through the points of access are identified, inventoried, and managed. The types of individuals and systems using each point of access are identified, documented, and managed. |
137 | Logical and Physical Access Controls | CC6.1 | 6 | Restricts Access to Information Assets—Combinations of data classification, separate data structures, port restrictions, access protocol restrictions, user identification, and digital certificates are used to establish access control rules for information assets. |
138 | Logical and Physical Access Controls | CC6.1 | 7 | Manages Identification and Authentication—Identification and authentication requirements are established, documented, and managed for individuals and systems accessing entity information, infrastructure and software. |
139 | Logical and Physical Access Controls | CC6.1 | 8 | Manages Credentials for Infrastructure and Software—New internal and external infrastructure and software are registered, authorized, and documented prior to being granted access credentials and implemented on the network or access point. Credentials are removed and access is disabled when access is no longer required or the infrastructure and software are no longer in use. |
140 | Logical and Physical Access Controls | CC6.1 | 9 | Uses Encryption to Protect Data—The entity uses encryption to supplement other measures used to protect data-at-rest, when such protections are deemed appropriate based on assessed risk. |
141 | Logical and Physical Access Controls | CC6.1 | 10 | Protects Encryption Keys—Processes are in place to protect encryption keys during generation, storage, use, and destruction. |
142 | Logical and Physical Access Controls | CC6.2 | | Prior to issuing system credentials and granting system access, the entity registers and authorizes new internal and external users whose access is administered by the entity. For |
143 | Logical and Physical Access Controls | CC6.2 | 1 | Controls Access Credentials to Protected Assets—Information asset access credentials are created based on an authorization from the system's asset owner or authorized custodian. |
144 | Logical and Physical Access Controls | CC6.2 | 2 | Removes Access to Protected Assets When Appropriate—Processes are in place to remove credential access when an individual no longer requires such access. |
145 | Logical and Physical Access Controls | CC6.2 | 3 | Reviews Appropriateness of Access Credentials—The appropriateness of access credentials is reviewed on a periodic basis for unnecessary and inappropriate individuals with credentials. |
146 | Logical and Physical Access Controls | CC6.3 | | The entity authorizes, modifies, or removes access to data, software, functions, and other protected information assets based on roles, responsibilities, or the system design and changes, giving consideration to the concepts of least privilege and segregation of duties, to meet the entity’s objectives. |
147 | Logical and Physical Access Controls | CC6.3 | 1 | Creates or Modifies Access to Protected Information Assets—Processes are in place to create or modify access to protected information assets based on authorization from the asset’s owner. |
148 | Logical and Physical Access Controls | CC6.3 | 2 | Removes Access to Protected Information Assets—Processes are in place to remove access to protected information assets when an individual no longer requires access. |
149 | Logical and Physical Access Controls | CC6.3 | 3 | Uses Role-Based Access Controls—Role-based access control is utilized to support segregation of incompatible functions. |
150 | Logical and Physical Access Controls | CC6.4 | | The entity restricts physical access to facilities and protected information assets (for example, data center facilities, back-up media storage, and other sensitive locations) to authorized personnel to meet the entity’s objectives. |
151 | Logical and Physical Access Controls | CC6.4 | 1 | Creates or Modifies Physical Access—Processes are in place to create or modify physical access to facilities such as data centers, office spaces, and work areas, based on authorization from the system's asset owner. |
152 | Logical and Physical Access Controls | CC6.4 | 2 | Removes Physical Access—Processes are in place to remove access to physical resources when an individual no longer requires access. |
153 | Logical and Physical Access Controls | CC6.4 | 3 | Reviews Physical Access—Processes are in place to periodically review physical access to ensure consistency with job responsibilities. |
154 | Logical and Physical Access Controls | CC6.5 | | The entity discontinues logical and physical protections over physical assets only after the ability to read or recover data and software from those assets has been diminished and is no longer required to meet the entity’s objectives. |
155 | Logical and Physical Access Controls | CC6.5 | 1 | Identifies Data and Software for Disposal—Procedures are in place to identify data and software stored on equipment to be disposed and to render such data and software unreadable. |
156 | Logical and Physical Access Controls | CC6.5 | 2 | Removes Data and Software From Entity Control—Procedures are in place to remove data and software stored on equipment to be removed from the physical control of the entity and to render such data and software unreadable. |
157 | Logical and Physical Access Controls | CC6.6 | | The entity implements logical access security measures to protect against threats from sources outside its system boundaries. |
158 | Logical and Physical Access Controls | CC6.6 | 1 | Restricts Access—The types of activities that can occur through a communication channel (for example, FTP site, router port) are restricted. |
159 | Logical and Physical Access Controls | CC6.6 | 2 | Protects Identification and Authentication Credentials—Identification and authentication credentials are protected during transmission outside its system boundaries. |
160 | Logical and Physical Access Controls | CC6.6 | 3 | Requires Additional Authentication or Credentials—Additional authentication information or credentials are required when accessing the system from outside its boundaries. |
161 | Logical and Physical Access Controls | CC6.6 | 4 | Implements Boundary Protection Systems—Boundary protection systems (for example, firewalls, demilitarized zones, and intrusion detection systems) are implemented to protect external access points from attempts and unauthorized access and are monitored to detect such attempts. |
162 | Logical and Physical Access Controls | CC6.7 | | The entity restricts the transmission, movement, and removal of information to authorized internal and external users and processes, and protects it during transmission, movement, or removal to meet the entity’s objectives. |
163 | Logical and Physical Access Controls | CC6.7 | 1 | Restricts the Ability to Perform Transmission—Data loss prevention processes and technologies are used to restrict ability to authorize and execute transmission, movement and removal of information. |
164 | Logical and Physical Access Controls | CC6.7 | 2 | Uses Encryption Technologies or Secure Communication Channels to Protect Data—Encryption technologies or secured communication channels are used to protect transmission of data and other communications beyond connectivity access points. |
165 | Logical and Physical Access Controls | CC6.7 | 3 | Protects Removal Media—Encryption technologies and physical asset protections are used for removable media (such as USB drives and back-up tapes), as appropriate. |
166 | Logical and Physical Access Controls | CC6.7 | 4 | Protects Mobile Devices—Processes are in place to protect mobile devices (such as laptops, smart phones and tablets) that serve as information assets. |
167 | Logical and Physical Access Controls | CC6.8 | | The entity implements controls to prevent or detect and act upon the introduction of unauthorized or malicious software to meet the entity’s objectives. |
168 | Logical and Physical Access Controls | CC6.8 | 1 | Restricts Application and Software Installation—The ability to install applications and software is restricted to authorized individuals. |
169 | Logical and Physical Access Controls | CC6.8 | 2 | Detects Unauthorized Changes to Software and Configuration Parameters—Processes are in place to detect changes to software and configuration parameters that may be indicative of unauthorized or malicious software. |
170 | Logical and Physical Access Controls | CC6.8 | 3 | Uses a Defined Change Control Process—A management-defined change control process is used for the implementation of software. |
171 | Logical and Physical Access Controls | CC6.8 | 4 | Uses Antivirus and Anti-Malware Software—Antivirus and anti-malware software is implemented and maintained to provide for the interception or detection and remediation of malware. |
172 | Logical and Physical Access Controls | CC6.8 | 5 | Scans Information Assets from Outside the Entity for Malware and Other Unauthorized Software—Procedures are in place to scan information assets that have been transferred or returned to the entity’s custody for malware and other unauthorized software and to remove any items detected prior to its implementation on the network. |
173 | System Operations | CC7.1 | | To meet its objectives, the entity uses detection and monitoring procedures to identify (1) changes to configurations that result in the introduction of new vulnerabilities, and (2) susceptibilities to newly discovered vulnerabilities. |
174 | System Operations | CC7.1 | 1 | Uses Defined Configuration Standards—Management has defined configuration standards. |
175 | System Operations | CC7.1 | 2 | Monitors Infrastructure and Software—The entity monitors infrastructure and software for noncompliance with the standards, which could threaten the achievement of the entity's objectives. |
176 | System Operations | CC7.1 | 3 | Implements Change-Detection Mechanisms—The IT system includes a change-detection mechanism (for example, file integrity monitoring tools) to alert personnel to unauthorized modifications of critical system files, configuration files, or content files. |
177 | System Operations | CC7.1 | 4 | Detects Unknown or Unauthorized Components—Procedures are in place to detect the introduction of unknown or unauthorized components. |
178 | System Operations | CC7.1 | 5 | Conducts Vulnerability Scans—The entity conducts vulnerability scans designed to identify potential vulnerabilities or misconfigurations on a periodic basis and after any significant change in the environment and takes action to remediate identified deficiencies on a timely basis. |
179 | System Operations | CC7.2 | | The entity monitors system components and the operation of those components for anomalies that are indicative of malicious acts, natural disasters, and errors affecting the entity’s ability to meet its objectives; anomalies are analyzed to determine whether they represent security events. |
180 | System Operations | CC7.2 | 1 | Implements Detection Policies, Procedures, and Tools—Detection policies and procedures are defined and implemented, and detection tools are implemented on Infrastructure and software to identify anomalies in the operation or unusual activity on systems. Procedures may include (1) a defined governance process for security event detection and management that includes provision of resources; (2) use of intelligence sources to identify newly discovered threats and vulnerabilities; and (3) logging of unusual system activities. |
181 | System Operations | CC7.2 | 2 | Designs Detection Measures—Detection measures are designed to identify anomalies that could result from actual or attempted (1) compromise of physical barriers; (2) unauthorized actions of authorized personnel; (3) use of compromised identification and authentication credentials; (4) unauthorized access from outside the system boundaries; (5) compromise of authorized external parties; and (6) implementation or connection of unauthorized hardware and software. |
182 | System Operations | CC7.2 | 3 | Implements Filters to Analyze Anomalies—Management has implemented procedures to filter, summarize, and analyze anomalies to identify security events. |
183 | System Operations | CC7.2 | 4 | Monitors Detection Tools for Effective Operation—Management has implemented processes to monitor the effectiveness of detection tools. |
184 | System Operations | CC7.3 | | The entity evaluates security events to determine whether they could or have resulted in a failure of the entity to meet its objectives (security incidents) and, if so, takes actions to prevent or address such failures. |
185 | System Operations | CC7.3 | 1 | Responds to Security Incidents—Procedures are in place for responding to security incidents and evaluating the effectiveness of those policies and procedures on a periodic basis. |
186 | System Operations | CC7.3 | 2 | Communicates and Reviews Detected Security Events—Detected security events are communicated to and reviewed by the individuals responsible for the management of the security program and actions are taken, if necessary. |
187 | System Operations | CC7.3 | 3 | Develops and Implements Procedures to Analyze Security Incidents—Procedures are in place to analyze security incidents and determine system impact. |
188 | System Operations | CC7.3 | 4 | Assesses the Impact on Personal Information—Detected security events are evaluated to determine whether they could or did result in the unauthorized disclosure or use of personal information and whether there has been a failure to comply with applicable laws or regulations. |
189 | System Operations | CC7.3 | 5 | Determines Personal Information Used or Disclosed—When an unauthorized use or disclosure of personal information has occurred, the affected information is identified. |
190 | System Operations | CC7.4 | | The entity responds to identified security incidents by executing a defined incident response program to understand, contain, remediate, and communicate security incidents, as appropriate. |
191 | System Operations | CC7.4 | 1 | Assigns Roles and Responsibilities—Roles and responsibilities for the design, implementation, maintenance, and execution of the incident response program are assigned, including the use of external resources when necessary. |
192 | System Operations | CC7.4 | 2 | Contains Security Incidents—Procedures are in place to contain security incidents that actively threaten entity objectives. |
193 | System Operations | CC7.4 | 3 | Mitigates Ongoing Security Incidents—Procedures are in place to mitigate the effects of ongoing security incidents. |
194 | System Operations | CC7.4 | 4 | Ends Threats Posed by Security Incidents—Procedures are in place to end the threats posed by security incidents through closure of the vulnerability, removal of unauthorized access, and other remediation actions. |
195 | System Operations | CC7.4 | 5 | Restores Operations—Procedures are in place to restore data and business operations to an interim state that permits the achievement of entity objectives. |
196 | System Operations | CC7.4 | 6 | Develops and Implements Communication Protocols for Security Incidents—Protocols for communicating security incidents and actions taken to affected parties are developed and implemented to meet the entity's objectives. |
197 | System Operations | CC7.4 | 7 | Obtains Understanding of Nature of Incident and Determines Containment Strategy—An understanding of the nature (for example, the method by which the incident occurred and the affected system resources) and severity of the security incident is obtained to determine the appropriate containment strategy, including (1) a determination of the appropriate response time frame, and (2) the determination and execution of the containment approach. |
198 | System Operations | CC7.4 | 8 | Remediates Identified Vulnerabilities—Identified vulnerabilities are remediated through the development and execution of remediation activities. |
199 | System Operations | CC7.4 | 9 | Communicates Remediation Activities—Remediation activities are documented and communicated in accordance with the incident response program. |
200 | System Operations | CC7.4 | 10 | Evaluates the Effectiveness of Incident Response—The design of incident response activities is evaluated for effectiveness on a periodic basis. |
201 | System Operations | CC7.4 | 11 | Periodically Evaluates Incidents—Periodically, management reviews incidents related to security, availability, processing integrity, confidentiality, and privacy and identifies the need for system changes based on incident patterns and root causes. |
202 | System Operations | CC7.4 | 12 | Communicates Unauthorized Use and Disclosure—Events that resulted in unauthorized use or disclosure of personal information are communicated to the data subjects, legal and regulatory authorities, and others as required. |
203 | System Operations | CC7.4 | 13 | Application of Sanctions—The conduct of individuals and organizations operating under the authority of the entity and involved in the unauthorized use or disclosure of personal information is evaluated and, if appropriate, sanctioned in accordance with entity policies and legal and regulatory requirements. |
204 | System Operations | CC7.5 | | The entity identifies, develops, and implements activities to recover from identified security incidents. |
205 | System Operations | CC7.5 | 1 | Restores the Affected Environment—The activities restore the affected environment to functional operation by rebuilding systems, updating software, installing patches, and changing configurations, as needed. |
206 | System Operations | CC7.5 | 2 | Communicates Information About the Event—Communications about the nature of the incident, recovery actions taken, and activities required for the prevention of future security events are made to management and others as appropriate (internal and external). |
207 | System Operations | CC7.5 | 3 | Determines Root Cause of the Event—The root cause of the event is determined. |
208 | System Operations | CC7.5 | 4 | Implements Changes to Prevent and Detect Recurrences—Additional architecture or changes to preventive and detective controls, or both, are implemented to prevent and detect recurrences on a timely basis. |
209 | System Operations | CC7.5 | 5 | Improves Response and Recovery Procedures—Lessons learned are analyzed, and the incident response plan and recovery procedures are improved. |
210 | System Operations | CC7.5 | 6 | Implements Incident Recovery Plan Testing—Incident recovery plan testing is performed on a periodic basis. The testing includes (1) development of testing scenarios based on threat likelihood and magnitude; (2) consideration of relevant system components from across the entity that can impair availability; (3) scenarios that consider the potential for the lack of availability of key personnel; and (4) revision of continuity plans and systems based on test results. |
211 | Change Management | CC8.1 | | The entity authorizes, designs, develops or acquires, configures, documents, tests, approves, and implements changes to infrastructure, data, software, and procedures to meet its objectives. |
212 | Change Management | CC8.1 | 1 | Manages Changes Throughout the System Lifecycle—A process for managing system changes throughout the lifecycle of the system and its components (infrastructure, data, software and procedures) is used to support system availability and processing integrity. |
213 | Change Management | CC8.1 | 2 | Authorizes Changes—A process is in place to authorize system changes prior to development. |
214 | Change Management | CC8.1 | 3 | Designs and Develops Changes—A process is in place to design and develop system changes. |
215 | Change Management | CC8.1 | 4 | Documents Changes—A process is in place to document system changes to support ongoing maintenance of the system and to support system users in performing their responsibilities. |
216 | Change Management | CC8.1 | 5 | Tracks System Changes—A process is in place to track system changes prior to implementation. |
217 | Change Management | CC8.1 | 6 | Configures Software—A process is in place to select and implement the configuration parameters used to control the functionality of software. |
218 | Change Management | CC8.1 | 7 | Tests System Changes—A process is in place to test system changes prior to implementation. |
219 | Change Management | CC8.1 | 8 | Approves System Changes—A process is in place to approve system changes prior to implementation. |
220 | Change Management | CC8.1 | 9 | Deploys System Changes—A process is in place to implement system changes. |
221 | Change Management | CC8.1 | 10 | Identifies and Evaluates System Changes—Objectives affected by system changes are identified, and the ability of the modified system to meet the objectives is evaluated throughout the system development life cycle. |
222 | Change Management | CC8.1 | 11 | Identifies Changes in Infrastructure, Data, Software, and Procedures Required to Remediate Incidents—Changes in infrastructure, data, software, and procedures required to remediate incidents to continue to meet objectives are identified, and the change process is initiated upon identification. |
223 | Change Management | CC8.1 | 12 | Creates Baseline Configuration of IT Technology—A baseline configuration of IT and control systems is created and maintained. |
224 | Change Management | CC8.1 | 13 | Provides for Changes Necessary in Emergency Situations —A process is in place for authorizing, designing, testing, approving and implementing changes necessary in emergency situations (that is, changes that need to be implemented in an urgent timeframe). |
225 | Change Management | CC8.1 | 14 | Protects Confidential Information—The entity protects confidential information during system design, development, testing, implementation, and change processes to meet the entity’s objectives related to confidentiality. |
226 | Change Management | CC8.1 | 15 | Protects Personal Information—The entity protects personal information during system design, development, testing, implementation, and change processes to meet the entity’s objectives related to privacy. |
227 | Risk Mitigation | CC9.1 | | The entity identifies, selects, and develops risk mitigation activities for risks arising from potential business disruptions. |
228 | Risk Mitigation | CC9.1 | 1 | Considers Mitigation of Risks of Business Disruption—Risk mitigation activities include the development of planned policies, procedures, communications, and alternative processing solutions to respond to, mitigate, and recover from security events that disrupt business operations. Those policies and procedures include monitoring processes and information and communications to meet the entity's objectives during response, mitigation, and recovery efforts. |
229 | Risk Mitigation | CC9.1 | 2 | Considers the Use of Insurance to Mitigate Financial Impact Risks—The risk management activities consider the use of insurance to offset the financial impact of loss events that would otherwise impair the ability of the entity to meet its objectives. |
230 | Risk Mitigation | CC9.2 | | The entity assesses and manages risks associated with vendors and business partners. |
231 | Risk Mitigation | CC9.2 | 1 | Establishes Requirements for Vendor and Business Partner Engagements—The entity establishes specific requirements for a vendor and business partner engagement that includes (1) scope of services and product specifications, (2) roles and responsibilities, (3) compliance requirements, and (4) service levels. |
232 | Risk Mitigation | CC9.2 | 2 | Assesses Vendor and Business Partner Risks—The entity assesses, on a periodic basis, the risks that vendors and business partners (and those entities’ vendors and business partners) represent to the achievement of the entity's objectives. |
233 | Risk Mitigation | CC9.2 | 3 | Assigns Responsibility and Accountability for Managing Vendors and Business Partners—The entity assigns responsibility and accountability for the management of risks associated with vendors and business partners. |
234 | Risk Mitigation | CC9.2 | 4 | Establishes Communication Protocols for Vendors and Business Partners—The entity establishes communication and resolution protocols for service or product issues related to vendors and business partners. |
235 | Risk Mitigation | CC9.2 | 5 | Establishes Exception Handling Procedures From Vendors and Business Partners —The entity establishes exception handling procedures for service or product issues related to vendors and business partners. |
236 | Risk Mitigation | CC9.2 | 6 | Assesses Vendor and Business Partner Performance—The entity periodically assesses the performance of vendors and business partners. |
237 | Risk Mitigation | CC9.2 | 7 | Implements Procedures for Addressing Issues Identified During Vendor and Business Partner Assessments—The entity implements procedures for addressing issues identified with vendor and business partner relationships. |
238 | Risk Mitigation | CC9.2 | 8 | Implements Procedures for Terminating Vendor and Business Partner Relationships — The entity implements procedures for terminating vendor and business partner relationships. |
239 | Risk Mitigation | CC9.2 | 9 | Obtains Confidentiality Commitments from Vendors and Business Partners—The entity obtains confidentiality commitments that are consistent with the entity’s confidentiality commitments and requirements from vendors and business partners who have access to confidential information. |
240 | Risk Mitigation | CC9.2 | 10 | Assesses Compliance With Confidentiality Commitments of Vendors and Business Partners — On a periodic and as-needed basis, the entity assesses compliance by vendors and business partners with the entity’s confidentiality commitments and requirements. |
241 | Risk Mitigation | CC9.2 | 11 | Obtains Privacy Commitments from Vendors and Business Partners—The entity obtains privacy commitments, consistent with the entity’s privacy commitments and requirements, from vendors and business partners who have access to personal information. |
242 | Risk Mitigation | CC9.2 | 12 | Assesses Compliance with Privacy Commitments of Vendors and Business Partners— On a periodic and as-needed basis, the entity assesses compliance by vendors and business partners with the entity’s privacy commitments and requirements and takes corrective action as necessary. |
243 | Additional Criteria For Availability | A1.1 | | The entity maintains, monitors, and evaluates current processing capacity and use of system components (infrastructure, data, and software) to manage capacity demand and to enable the implementation of additional capacity to help meet its objectives. |
244 | Additional Criteria For Availability | A1.1 | 1 | Measures Current Usage—The use of the system components is measured to establish a baseline for capacity management and to use when evaluating the risk of impaired availability due to capacity constraints. |
245 | Additional Criteria For Availability | A1.1 | 2 | Forecasts Capacity—The expected average and peak use of system components is forecasted and compared to system capacity and associated tolerances. Forecasting considers capacity in the event of the failure of system components that constrain capacity. |
246 | Additional Criteria For Availability | A1.1 | 3 | Makes Changes Based on Forecasts—The system change management process is initiated when forecasted usage exceeds capacity tolerances. |
247 | Additional Criteria For Availability | A1.2 | | The entity authorizes, designs, develops or acquires, implements, operates, approves, maintains, and monitors environmental protections, software, data back-up processes, and recovery infrastructure to meet its objectives. |
248 | Additional Criteria For Availability | A1.2 | 1 | Identifies Environmental Threats—As part of the risk assessment process, management identifies environmental threats that could impair the availability of the system, including threats resulting from adverse weather, failure of environmental control systems, electrical discharge, fire, and water. |
249 | Additional Criteria For Availability | A1.2 | 2 | Designs Detection Measures—Detection measures are implemented to identify anomalies that could result from environmental threat events. |
250 | Additional Criteria For Availability | A1.2 | 3 | Implements and Maintains Environmental Protection Mechanisms— Management implements and maintains environmental protection mechanisms to prevent and mitigate against environmental events. |
251 | Additional Criteria For Availability | A1.2 | 4 | Implements Alerts to Analyze Anomalies—Management implements alerts that are communicated to personnel for analysis to identify environmental threat events. |
252 | Additional Criteria For Availability | A1.2 | 5 | Responds to Environmental Threat Events—Procedures are in place for responding to environmental threat events and for evaluating the effectiveness of those policies and procedures on a periodic basis. This includes automatic mitigation systems (for example, uninterruptable power system and generator back-up subsystem). |
253 | Additional Criteria For Availability | A1.2 | 6 | Communicates and Reviews Detected Environmental Threat Events—Detected environmental threat events are communicated to and reviewed by the individuals responsible for the management of the system, and actions are taken, if necessary. |
254 | Additional Criteria For Availability | A1.2 | 7 | Determines Data Requiring Backup—Data is evaluated to determine whether backup is required. |
255 | Additional Criteria For Availability | A1.2 | 8 | Performs Data Backup—Procedures are in place for backing up data, monitoring to detect back-up failures, and initiating corrective action when such failures occur. |
256 | Additional Criteria For Availability | A1.2 | 9 | Addresses Offsite Storage—Back-up data is stored in a location at a distance from its principal storage location sufficient that the likelihood of a security or environmental threat event affecting both sets of data is reduced to an appropriate level. |
257 | Additional Criteria For Availability | A1.2 | 10 | Implements Alternate Processing Infrastructure—Measures are implemented for migrating processing to alternate infrastructure in the event normal processing infrastructure becomes unavailable. |
258 | Additional Criteria For Availability | A1.3 | | The entity tests recovery plan procedures supporting system recovery to meet its objectives. |
259 | Additional Criteria For Availability | A1.3 | 1 | Implements Business Continuity Plan Testing—Business continuity plan testing is performed on a periodic basis. The testing includes (1) development of testing scenarios based on threat likelihood and magnitude; (2) consideration of system components from across the entity that can impair the availability; (3) scenarios that consider the potential for the lack of availability of key personnel; and (4) revision of continuity plans and systems based on test results. |
260 | Additional Criteria For Availability | A1.3 | 2 | Tests Integrity and Completeness of Back-Up Data—The integrity and completeness of back-up information is tested on a periodic basis. |
261 | Additional Criteria For Confidentiality | C1.1 | | The entity identifies and maintains confidential information to meet the entity’s objectives related to confidentiality. |
262 | Additional Criteria For Confidentiality | C1.1 | 1 | Identifies Confidential information—Procedures are in place to identify and designate confidential information when it is received or created and to determine the period over which the confidential information is to be retained. |
263 | Additional Criteria For Confidentiality | C1.1 | 2 | Protects Confidential Information from Destruction—Procedures are in place to protect confidential information from erasure or destruction during the specified retention period of the information. |
264 | Additional Criteria For Confidentiality | C1.2 | | The entity disposes of confidential information to meet the entity’s objectives related to confidentiality. |
265 | Additional Criteria For Confidentiality | C1.2 | 1 | Identifies Confidential Information for Destruction—Procedures are in place to identify confidential information requiring destruction when the end of the retention period is reached. |
266 | Additional Criteria For Confidentiality | C1.2 | 2 | Destroys Confidential Information—Procedures are in place to erase or otherwise destroy confidential information that has been identified for destruction. |
267 | Additional Criteria For Processing Integrity | PI1.1 | | The entity obtains or generates, uses, and communicates relevant, quality information regarding the objectives related to processing, including definitions of data processed and product and service specifications, to support the use of products and services. |
268 | Additional Criteria For Processing Integrity | PI1.1 | | Identifies Information Specifications—The entity identifies information specifications required to support the use of products and services. |
269 | Additional Criteria For Processing Integrity | PI1.1 | | Defines Data Necessary to Support a Product or Service—When data is provided as part of a service or product or as part of a reporting obligation related to a product or service: |
270 | Additional Criteria For Processing Integrity | PI1.1 | | (1) The definition of the data is available to the users of the data |
271 | Additional Criteria For Processing Integrity | PI1.1 | | (2) The definition of the data includes the following information: |
272 | Additional Criteria For Processing Integrity | PI1.1 | | — The population of events or instances included in the data |
273 | Additional Criteria For Processing Integrity | PI1.1 | | — The nature of each element (for example, field) of the data (that is, the event or instance to which the data element relates, for example, transaction price of a sale of XYZ Corporation stock for the last trade in that stock on a given day) |
274 | Additional Criteria For Processing Integrity | PI1.1 | | — Source(s) of the data |
275 | Additional Criteria For Processing Integrity | PI1.1 | | — The unit(s) of measurement of data elements (for example, fields) |
276 | Additional Criteria For Processing Integrity | PI1.1 | | — The accuracy/correctness/precision of measurement |
277 | Additional Criteria For Processing Integrity | PI1.1 | | — The uncertainty or confidence interval inherent in each data element and in the population of those elements |
278 | Additional Criteria For Processing Integrity | PI1.1 | | — The date the data was observed or the period of time during which the events relevant to the data occurred |
279 | Additional Criteria For Processing Integrity | PI1.1 | | — The factors in addition to the date and period of time used to determine the inclusion and exclusion of items in the data elements and population |
280 | Additional Criteria For Processing Integrity | PI1.1 | | (3) The definition is complete and accurate. |
281 | Additional Criteria For Processing Integrity | PI1.1 | | (4) The description of the data identifies any information that is necessary to understand each data element and the population in a manner consistent with its definition and intended purpose (meta-data) that has not been included within the data. |
282 | Additional Criteria For Processing Integrity | PI1.2 | | The entity implements policies and procedures over system inputs, including controls over completeness and accuracy, to result in products, services, and reporting to meet the |
283 | Additional Criteria For Processing Integrity | PI1.2 | 1 | Defines Characteristics of Processing Inputs—The characteristics of processing inputs that are necessary to meet requirements are defined. |
284 | Additional Criteria For Processing Integrity | PI1.2 | 2 | Evaluates Processing Inputs—Processing inputs are evaluated for compliance with defined input requirements. |
285 | Additional Criteria For Processing Integrity | PI1.2 | 3 | Creates and Maintains Records of System Inputs—Records of system input activities are created and maintained completely and accurately in a timely manner. |
286 | Additional Criteria For Processing Integrity | PI1.3 | | The entity implements policies and procedures over system processing to result in products, services, and reporting to meet the entity’s objectives. |
287 | Additional Criteria For Processing Integrity | PI1.3 | 1 | Defines Processing Specifications—The processing specifications that are necessary to meet product or service requirements are defined. |
288 | Additional Criteria For Processing Integrity | PI1.3 | 2 | Defines Processing Activities—Processing activities are defined to result in products or services that meet specifications. |
289 | Additional Criteria For Processing Integrity | PI1.3 | 3 | Detects and Corrects Production Errors—Errors in the production process are detected and corrected in a timely manner. |
290 | Additional Criteria For Processing Integrity | PI1.3 | 4 | Records System Processing Activities—System processing activities are recorded completely and accurately in a timely manner. |
291 | Additional Criteria For Processing Integrity | PI1.3 | 5 | Processes Inputs—Inputs are processed completely, accurately, and timely as authorized in accordance with defined processing activities. |
292 | Additional Criteria For Processing Integrity | PI1.4 | | The entity implements policies and procedures to make available or deliver output completely, accurately, and timely in accordance with specifications to meet the entity’s objectives. |
293 | Additional Criteria For Processing Integrity | PI1.4 | 1 | Protects Output—Output is protected when stored or delivered, or both, to prevent theft, destruction, corruption, or deterioration that would prevent output from meeting specifications. |
294 | Additional Criteria For Processing Integrity | PI1.4 | 2 | Distributes Output Only to Intended Parties—Output is distributed or made available only to intended parties. |
295 | Additional Criteria For Processing Integrity | PI1.4 | 3 | Distributes Output Completely and Accurately—Procedures are in place to provide for the completeness, accuracy, and timeliness of distributed output. |
296 | Additional Criteria For Processing Integrity | PI1.4 | 4 | Creates and Maintains Records of System Output Activities—Records of system output activities are created and maintained completely and accurately in a timely manner. |
297 | Additional Criteria For Processing Integrity | PI1.5 | | The entity implements policies and procedures to store inputs, items in processing, and outputs completely, accurately, and timely in accordance with system specifications to meet the entity’s objectives. |
298 | Additional Criteria For Processing Integrity | PI1.5 | 1 | Protects Stored Items—Stored items are protected to prevent theft, corruption, destruction, or deterioration that would prevent output from meeting specifications. |
299 | Additional Criteria For Processing Integrity | PI1.5 | 2 | Archives and Protects System Records—System records are archived, and archives are protected against theft, corruption, destruction, or deterioration that would prevent them from being used. |
300 | Additional Criteria For Processing Integrity | PI1.5 | 3 | Stores Data Completely and Accurately—Procedures are in place to provide for the complete, accurate, and timely storage of data. |
301 | Additional Criteria For Processing Integrity | PI1.5 | 4 | Creates and Maintains Records of System Storage Activities—Records of system storage activities are created and maintained completely and accurately in a timely manner. |
302 | Additional Criteria For Privacy | P1.0 | | Privacy Criteria Related to Notice and Communication of Objectives Related to Privacy |
303 | Additional Criteria For Privacy | P1.1 | | The entity provides notice to data subjects about its privacy practices to meet the entity’s objectives related to privacy. The notice is updated and communicated to data subjects in a timely manner for changes to the entity’s privacy practices, including changes in the use of personal information, to meet the entity’s objectives related to privacy. |
304 | Additional Criteria For Privacy | | | Communicates to Data Subjects—Notice is provided to data subjects regarding the following: |
305 | Additional Criteria For Privacy | | | — Purpose for collecting personal information |
306 | Additional Criteria For Privacy | | | — Choice and consent |
307 | Additional Criteria For Privacy | | | — Types of personal information collected |
308 | Additional Criteria For Privacy | | | — Methods of collection (for example, use of cookies or other tracking techniques) |
309 | Additional Criteria For Privacy | | | — Use, retention, and disposal |
310 | Additional Criteria For Privacy | | | — Access |
311 | Additional Criteria For Privacy | | | — Disclosure to third parties |
312 | Additional Criteria For Privacy | | | — Security for privacy |
313 | Additional Criteria For Privacy | | | — Quality, including data subjects’ responsibilities for quality |
314 | Additional Criteria For Privacy | | | — Monitoring and enforcement |
315 | Additional Criteria For Privacy | | | If personal information is collected from sources other than the individual, such sources are described in the privacy notice. |
316 | Additional Criteria For Privacy | | | Provides Notice to Data Subjects—Notice is provided to data subjects (1) at or before the time personal information is collected or as soon as practical thereafter, (2) at or before the entity changes its privacy notice or as soon as practical thereafter, or (3) before personal information is used for new purposes not previously identified. |
317 | Additional Criteria For Privacy | | | Covers Entities and Activities in Notice —An objective description of the entities and activities covered is included in the entity’s privacy notice. |
318 | Additional Criteria For Privacy | | | Uses Clear and Conspicuous Language—The entity’s privacy notice is conspicuous and uses clear language. |
319 | Additional Criteria For Privacy | P2.0 | | Privacy Criteria Related to Choice and Consent |
320 | Additional Criteria For Privacy | P2.1 | | The entity communicates choices available regarding the collection, use, retention, disclosure, and disposal of personal information to the data subjects and the consequences, if any, of each choice. Explicit consent for the collection, use, retention, disclosure, and disposal of personal information is obtained from data subjects or other authorized persons, if required. Such consent is obtained only for the intended purpose of the information to meet the entity’s objectives related to privacy. The entity’s basis for determining implicit consent for the collection, use, retention, disclosure, and disposal of personal information is documented. |
321 | Additional Criteria For Privacy | P2.1 | 1 | Communicates to Data Subjects—Data subjects are informed (a) about the choices available to them with respect to the collection, use, and disclosure of personal information and (b) that implicit or explicit consent is required to collect, use, and disclose personal information, unless a law or regulation specifically requires or allows otherwise. |
322 | Additional Criteria For Privacy | P2.1 | 2 | Communicates Consequences of Denying or Withdrawing Consent—When personal information is collected, data subjects are informed of the consequences of refusing to provide personal information or denying or withdrawing consent to use personal information for purposes identified in the notice. |
323 | Additional Criteria For Privacy | P2.1 | 3 | Obtains Implicit or Explicit Consent—Implicit or explicit consent is obtained from data subjects at or before the time personal information is collected or soon thereafter. The individual’s preferences expressed in his or her consent are confirmed and implemented. |
324 | Additional Criteria For Privacy | P2.1 | 4 | Documents and Obtains Consent for New Purposes and Uses—If information that was previously collected is to be used for purposes not previously identified in the privacy notice, the new purpose is documented, the data subject is notified, and implicit or explicit consent is obtained prior to such new use or purpose. |
325 | Additional Criteria For Privacy | P2.1 | 5 | Obtains Explicit Consent for Sensitive Information—Explicit consent is obtained directly from the data subject when sensitive personal information is collected, used, or disclosed, unless a law or regulation specifically requires otherwise. |
326 | Additional Criteria For Privacy | P2.1 | 6 | Obtains Consent for Data Transfers—Consent is obtained before personal information is transferred to or from an individual’s computer or other similar device. |
327 | Additional Criteria For Privacy | P3.0 | | Privacy Criteria Related to Collection |
328 | Additional Criteria For Privacy | P3.1 | | Personal information is collected consistent with the entity’s objectives related to privacy. |
329 | Additional Criteria For Privacy | P3.1 | 1 | Limits the Collection of Personal Information—The collection of personal information is limited to that necessary to meet the entity’s objectives. |
330 | Additional Criteria For Privacy | P3.1 | 2 | Collects Information by Fair and Lawful Means—Methods of collecting personal information are reviewed by management before they are implemented to confirm that personal information is obtained (a) fairly, without intimidation or deception, and (b) lawfully, adhering to all relevant rules of law, whether derived from statute or common law, relating to the collection of personal information. |
331 | Additional Criteria For Privacy | P3.1 | 3 | Collects Information From Reliable Sources—Management confirms that third parties from whom personal information is collected (that is, sources other than the individual) are reliable sources that collect information fairly and lawfully. |
332 | Additional Criteria For Privacy | P3.1 | 4 | Informs Data Subjects When Additional Information Is Acquired—Data subjects are informed if the entity develops or acquires additional information about them for its use. |
333 | Additional Criteria For Privacy | P3.2 | | For information requiring explicit consent, the entity communicates the need for such consent, as well as the consequences of a failure to provide consent for the request for personal information, and obtains the consent prior to the collection of the information to meet the entity’s objectives related to privacy. |
334 | Additional Criteria For Privacy | P3.2 | 1 | Obtains Explicit Consent for Sensitive Information—Explicit consent is obtained directly from the data subject when sensitive personal information is collected, used, or disclosed, unless a law or regulation specifically requires otherwise. |
335 | Additional Criteria For Privacy | P3.2 | 2 | Documents Explicit Consent to Retain Information–Documentation of explicit consent for the collection, use, or disclosure of sensitive personal information is retained in accordance with objectives related to privacy. |
336 | Additional Criteria For Privacy | P4.0 | | Privacy Criteria Related to Use, Retention, and Disposal |
337 | Additional Criteria For Privacy | P4.1 | | The entity limits the use of personal information to the purposes identified in the entity’s objectives related to privacy. |
338 | Additional Criteria For Privacy | P4.1 | 1 | Uses Personal Information for Intended Purposes—Personal information is used only for the intended purposes for which it was collected and only when implicit or explicit consent has been obtained unless a law or regulation specifically requires otherwise. |
339 | Additional Criteria For Privacy | P4.2 | | The entity retains personal information consistent with the entity’s objectives related to privacy. |
340 | Additional Criteria For Privacy | P4.2 | 1 | Retains Personal Information—Personal information is retained for no longer than necessary to fulfill the stated purposes, unless a law or regulation specifically requires otherwise. |
341 | Additional Criteria For Privacy | P4.2 | 2 | Protects Personal Information—Policies and procedures have been implemented to protect personal information from erasure or destruction during the specified retention period of the information. |
342 | Additional Criteria For Privacy | P4.3 | | The entity securely disposes of personal information to meet the entity’s objectives related to privacy |
343 | Additional Criteria For Privacy | P4.3 | 1 | Captures, Identifies, and Flags Requests for Deletion—Requests for deletion of personal information are captured, and information related to the requests is identified and flagged for destruction to meet the entity’s objectives related to privacy. |
344 | Additional Criteria For Privacy | P4.3 | 2 | Disposes of, Destroys, and Redacts Personal Information—Personal information no longer retained is anonymized, disposed of, or destroyed in a manner that prevents loss, theft, misuse, or unauthorized access. |
345 | Additional Criteria For Privacy | P4.3 | 3 | Destroys Personal Information—Policies and procedures are implemented to erase or otherwise destroy personal information that has been identified for destruction. |
346 | Additional Criteria For Privacy | P5.0 | | Privacy Criteria Related to Access |
347 | Additional Criteria For Privacy | P5.1 | | The entity grants identified and authenticated data subjects the ability to access their stored personal information for review and, upon request, provides physical or electronic copies of that information to data subjects to meet the entity’s objectives related to privacy. If access is denied, data subjects are informed of the denial and reason for such denial, as required, to meet the entity’s objectives related to privacy. |
348 | Additional Criteria For Privacy | P5.1 | 1 | Authenticates Data Subjects’ Identity—The identity of data subjects who request access to their personal information is authenticated before they are given access to that information. |
349 | Additional Criteria For Privacy | P5.1 | 2 | Permits Data Subjects Access to Their Personal Information—Data subjects are able to determine whether the entity maintains personal information about them and, upon request, may obtain access to their personal information. |
350 | Additional Criteria For Privacy | P5.1 | 3 | Provides Understandable Personal Information Within Reasonable Time—Personal information is provided to data subjects in an understandable form, in a reasonable time frame, and at a reasonable cost, if any. |
351 | Additional Criteria For Privacy | P5.1 | 4 | Informs Data Subjects If Access Is Denied—When data subjects are denied access to their personal information, the entity informs them of the denial and the reason for the denial in a timely manner, unless prohibited by law or regulation. |
352 | Additional Criteria For Privacy | P5.2 | | The entity corrects, amends, or appends personal information based on information provided by data subjects and communicates such information to third parties, as committed or required, to meet the entity’s objectives related to privacy. If a request for correction is denied, data subjects are informed of the denial and reason for such denial to meet the entity’s objectives related to privacy. |
353 | Additional Criteria For Privacy | P5.2 | 1 | Communicates Denial of Access Requests—Data subjects are informed, in writing, of the reason a request for access to their personal information was denied, the source of the entity’s legal right to deny such access, if applicable, and the individual’s right, if any, to challenge such denial, as specifically permitted or required by law or regulation. |
354 | Additional Criteria For Privacy | P5.2 | 2 | Permits Data Subjects to Update or Correct Personal Information—Data subjects are able to update or correct personal information held by the entity. The entity provides such updated or corrected information to third parties that were previously provided with the data subject’s personal information consistent with the entity’s objective related to privacy. |
355 | Additional Criteria For Privacy | P5.2 | 3 | Communicates Denial of Correction Requests—Data subjects are informed, in writing, about the reason a request for correction of personal information was denied and how they may appeal. |
356 | Additional Criteria For Privacy | P6.0 | | Privacy Criteria Related to Disclosure and Notification |
357 | Additional Criteria For Privacy | P6.1 | | The entity discloses personal information to third parties with the explicit consent of data subjects, and such consent is obtained prior to disclosure to meet the entity’s objectives related to privacy |
358 | Additional Criteria For Privacy | P6.1 | 1 | Communicates Privacy Policies to Third Parties—Privacy policies or other specific instructions or requirements for handling personal information are communicated to third parties to whom personal information is disclosed. |
359 | Additional Criteria For Privacy | P6.1 | 2 | Discloses Personal Information Only When Appropriate—Personal information is disclosed to third parties only for the purposes for which it was collected or created and only when implicit or explicit consent has been obtained from the data subject, unless a law or regulation specifically requires otherwise. |
360 | Additional Criteria For Privacy | P6.1 | 3 | Discloses Personal Information Only to Appropriate Third Parties—Personal information is disclosed only to third parties who have agreements with the entity to protect personal information in a manner consistent with the relevant aspects of the entity’s privacy notice or other specific instructions or requirements. The entity has procedures in place to evaluate that the third parties have effective controls to meet the terms of the agreement, instructions, or requirements. |
361 | Additional Criteria For Privacy | P6.1 | 4 | Discloses Information to Third Parties for New Purposes and Uses—Personal information is disclosed to third parties for new purposes or uses only with the prior implicit or explicit consent of data subjects. |
362 | Additional Criteria For Privacy | P6.2 | | The entity creates and retains a complete, accurate, and timely record of authorized disclosures of personal information to meet the entity’s objectives related to privacy |
363 | Additional Criteria For Privacy | P6.2 | 1 | Creates and Retains Record of Authorized Disclosures—The entity creates and maintains a record of authorized disclosures of personal information that is complete, accurate, and timely. |
364 | Additional Criteria For Privacy | P6.3 | | The entity creates and retains a complete, accurate, and timely record of detected or reported unauthorized disclosures (including breaches) of personal information to meet the entity’s objectives related to privacy. |
365 | Additional Criteria For Privacy | P6.3 | 1 | Creates and Retains Record of Detected or Reported Unauthorized Disclosures—The entity creates and maintains a record of detected or reported unauthorized disclosures of personal information that is complete, accurate, and timely. |
366 | Additional Criteria For Privacy | P6.4 | | The entity obtains privacy commitments from vendors and other third parties who have access to personal information to meet the entity’s objectives related to privacy. The entity assesses those parties’ compliance on a periodic and as-needed basis and takes corrective action, if necessary. |
367 | Additional Criteria For Privacy | P6.4 | 1 | Discloses Personal Information Only to Appropriate Third Parties—Personal information is disclosed only to third parties who have agreements with the entity to protect personal information in a manner consistent with the relevant aspects of the entity’s privacy notice or other specific instructions or requirements. The entity has procedures in place to evaluate that the third parties have effective controls to meet the terms of the agreement, instructions, or requirements. |
368 | Additional Criteria For Privacy | P6.4 | 2 | Remediates Misuse of Personal Information by a Third Party —The entity takes remedial action in response to misuse of personal information by a third party to whom the entity has transferred such information. |
369 | Additional Criteria For Privacy | P6.5 | | The entity obtains commitments from vendors and other third parties with access to personal information to notify the entity in the event of actual or suspected unauthorized disclosures of personal information. Such notifications are reported to appropriate personnel and acted on in |
370 | Additional Criteria For Privacy | P6.5 | 1 | Remediates Misuse of Personal Information by a Third Party—The entity takes remedial action in response to misuse of personal information by a third party to whom the entity has transferred such information. |
371 | Additional Criteria For Privacy | P6.5 | 2 | Reports Actual or Suspected Unauthorized Disclosures—A process exists for obtaining commitments from vendors and other third parties to report to the entity actual or suspected unauthorized disclosures of personal information. |
372 | Additional Criteria For Privacy | P6.6 | | The entity provides notification of breaches and incidents to affected data subjects, regulators, and others to meet the entity’s objectives related to privacy. |
373 | Additional Criteria For Privacy | P6.6 | 1 | Remediates Misuse of Personal Information by a Third Party—The entity takes remedial action in response to misuse of personal information by a third party to whom the entity has transferred such information. |
374 | Additional Criteria For Privacy | P6.6 | 2 | Provides Notice of Breaches and Incidents—The entity has a process for providing notice of breaches and incidents to affected data subjects, regulators, and others to meet the entity’s objectives related to privacy. |
375 | Additional Criteria For Privacy | P6.7 | | The entity provides data subjects with an accounting of the personal information held and disclosure of the data subjects’ personal information, upon the data subjects’ request, to meet the entity’s objectives related to privacy. |
376 | Additional Criteria For Privacy | P6.7 | 1 | Identifies Types of Personal Information and Handling Process—The types of personal information and sensitive personal information and the related processes, systems, and third parties involved in the handling of such information are identified. |
377 | Additional Criteria For Privacy | P6.7 | 2 | Captures, Identifies, and Communicates Requests for Information—Requests for an accounting of personal information held and disclosures of the data subjects’ personal information are captured, and information related to the requests is identified and communicated to data subjects to meet the entity’s objectives related to privacy. |
378 | Additional Criteria For Privacy | P7.0 | | Privacy Criteria Related to Quality |
379 | Additional Criteria For Privacy | P7.1 | | The entity collects and maintains accurate, up-to-date, complete, and relevant personal information to meet the entity’s objectives related to privacy |
380 | Additional Criteria For Privacy | P7.1 | 1 | Ensures Accuracy and Completeness of Personal Information—Personal information is accurate and complete for the purposes for which it is to be used. |
381 | Additional Criteria For Privacy | P7.1 | 2 | Ensures Relevance of Personal Information—Personal information is relevant to the purposes for which it is to be used. |
382 | Additional Criteria For Privacy | P8.0 | | Privacy Criteria Related to Monitoring and Enforcement |
383 | Additional Criteria For Privacy | P8.1 | | The entity implements a process for receiving, addressing, resolving, and communicating the resolution of inquiries, complaints, and disputes from data subjects and others and periodically monitors compliance to meet the entity’s objectives related to privacy. Corrections and other necessary actions related to identified deficiencies are made or taken in a timely manner. |
384 | Additional Criteria For Privacy | P8.1 | 1 | Communicates to Data Subjects—Data subjects are informed about how to contact the entity with inquiries, complaints, and disputes. |
385 | Additional Criteria For Privacy | P8.1 | 2 | Addresses Inquiries, Complaints, and Disputes—A process is in place to address inquiries, complaints, and disputes. |
386 | Additional Criteria For Privacy | P8.1 | 3 | Documents and Communicates Dispute Resolution and Recourse—Each complaint is addressed, and the resolution is documented and communicated to the individual. |
387 | Additional Criteria For Privacy | P8.1 | 4 | Documents and Reports Compliance Review Results—Compliance with objectives related to privacy are reviewed and documented, and the results of such reviews are reported to management. If problems are identified, remediation plans are developed and implemented. |
388 | Additional Criteria For Privacy | P8.1 | 5 | Documents and Reports Instances of Noncompliance—Instances of noncompliance with objectives related to privacy are documented and reported and, if needed, corrective and disciplinary measures are taken on a timely basis. |
389 | Additional Criteria For Privacy | P8.1 | 6 | Performs Ongoing Monitoring—Ongoing procedures are performed for monitoring the effectiveness of controls over personal information and for taking timely corrective actions when necessary. |
References
- 2023 Trust Services Criteria (TSCs) for SOC 2 Reports
- SOC2 Simplified : Full Framework Review in Plain English - https://www.youtube.com/watch?v=2rAz9VohEdE
- https://wilsonmar.github.io/soc2/

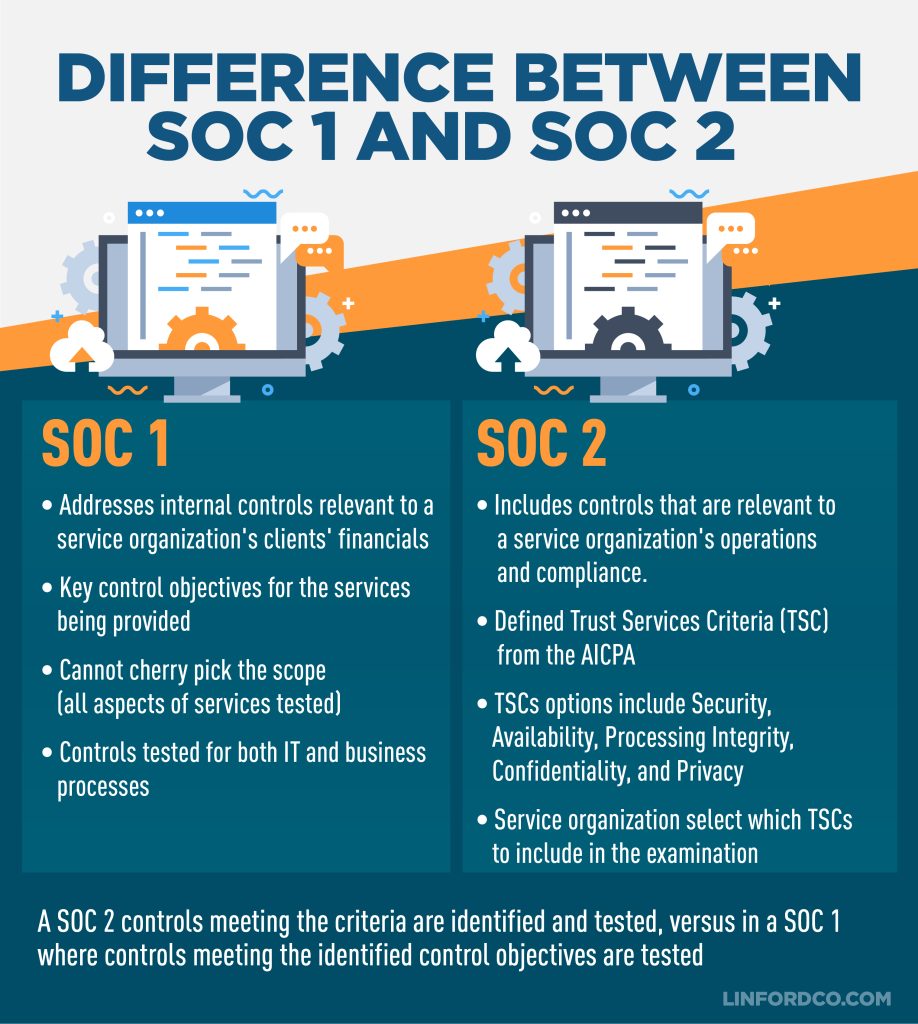








No comments:
Post a Comment