Palo Alto VM-Series Firewall Special Configuration in Azure & How to Register VM with Credits
Netsec
11/03/2022
0 Comments
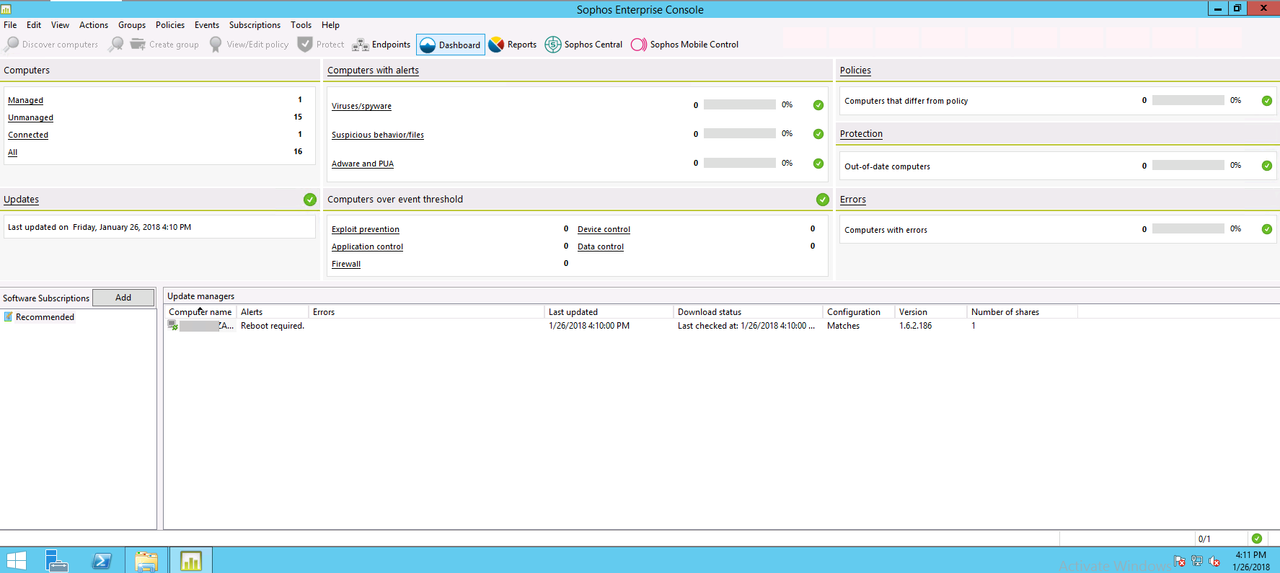
There are some configuration on Azure network to get your Palo Alto firewall working well for the passing through traffic. Especially for pi...
Read More