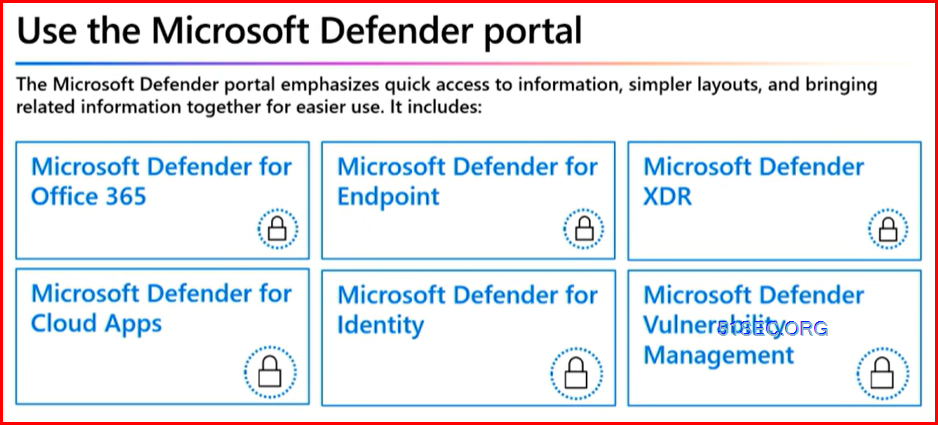
Microsoft Defender for Endpoint (MDE) Deployment and Configuration Steps with Security Policy Details
Netsec
2/13/2025
0 Comments
The following steps is only used for a selected environment to have a simplified deployments which is to target bringing MDE to all devices ...
Read More

![[5 Mins Docker] Deploy a free, simple and safe honeypot with Own Domain - HFISH](https://i.51sec.org/202309/96435237_1481507445353308_3640914368901677056_n.png)