I worked on one IPSec VPN configuration from my vpn gateway fw-ras to customer's gateway. The interesting traffic is from Customer public ip to our server's public ip address 20.153.121.59 which is NAT-ed to internal ip address 10.1.106.59. On my gateway's vpn domain includes this public ip 20.153.121.59 and Internal Segment 10.1.106.x/24.
The VPN works fine. Customer was able to reach us through IPSec VPN Tunnel. By the way I am using default NAT behaviour which is NAT happening on client side. The issue I met is the Partial Overlapping Encryption Domains warning message when I verified and installed policy.
Symptons:
Here is screenshots and copied error / warning messages:"Network Security Policy 'Standard' was prepared on Wed Aug 26 13:36:44 2015.
The following errors and warnings exist: The gateways fw-ras and vpnm have partial overlapping encryption domains. Therefore, Endpoint Connect users will not support MEP configuration SecureRemote/SecureClient users will not be able to create site. If any of the GWs should not be exported to SR/SC, please remove it from the RemoteAccess community or uncheck the exportable for SR box. The overlapping domain include : 10.1.72.14 - 10.1.72.16 The exclusive domain of fw-ras include: 20.153.121.59 - 20.153.121.62 The exclusive domain of vpnm include: 10.1.240.0 - 10.1.240.255"
Basically it mentioned some ip addresses are used in multiple vpn domains, especially in RemoteAccess community. But I double checked both gateways fw-ras and vpnm, their encryption domains are not overlapping at all.
Interesting things, if I removed 20.153.121.59 from vpn encryption domain of gateway fw-ras, this error/warning message disappeared. But IPSec vpn configuration will need this public ip address to make sure the traffic can be encrypted and sent to customer's gateway.
Solutions:
Good thing in the message is it mentioned "If any of the GWs should not be exported to SR/SC, please remove it from the RemoteAccess community or uncheck the exportable for SR box". Since the gateway fw-ras is not in RemoteAccess community, the only option for me is to uncheck the exportable for SR box.
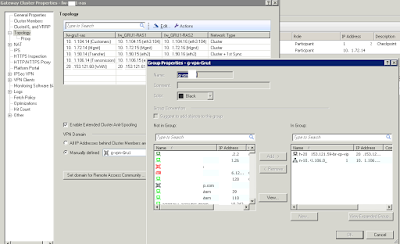
I found the option in the gateway's properties window -> IPSec VPN -> Traditional mode configuration...:
After unchecked the Exportable for SecuRemote/SecureClient, the installation is flawless.









No comments:
Post a Comment