This post will use a typical WiFi in office environment as an example to present related configuration on WLC, Radius (NPS), DHCP Servers.
1. Topology:
1.1 Network Topology
Relate Posts:
- Cisco Wireless Controller 5508 Configuration Step by Step - Part 1 (CLI and GUI) -
- Cisco Wireless Controller 5508 Configuration Step by Step - Part 2 (User/Machine Auth) -
- Cisco Wireless Controller 5508 Configuration Step by Step - Part 3 (Certs Auth and Other Settings)
- Cisco Wireless Controller 5508 Configuration - Tips and Tricks
1.2 Device List:
- Cisco AP 1702i
- Switches
- Radius Server - Microsoft NPS
- DHCP Server
- Cisco WLC5508
1.3 Topology for Wireless Access with Digital Certificate Client Authentication
2. WiFi Access Requirements
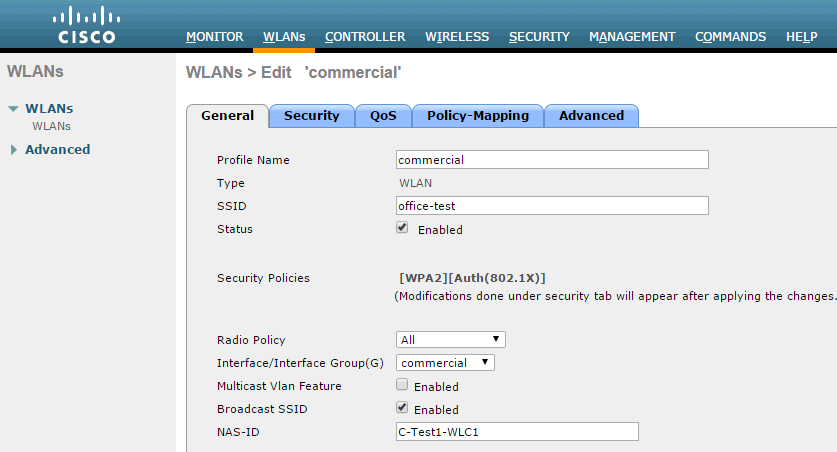
This WiFi access is primarily intended for company laptops which already has client certificate installed on the machine through domain group policy. This WiFi network will be on a separate office VLAN from other office VLAN.
Other WiFi connected devices must not be allowed connecting to this office WiFi. They will connect through Company Guest WiFi. Mobile devices such as BYOD, Blackberry or other PDA and smart phones should not be allowed to connect to Office WiFi.
3. NPS Configuration
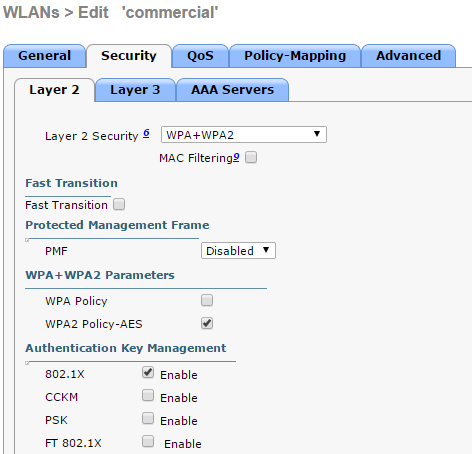
When using WPA2-Enterprise with 802.1x authentication EAP-TLS can be specified as an authentication method. When EAP-TLS is the chosen authentication method both the wireless client and the RADIUS server use certificates to verify their identities to each other and perform mutual authentication. Below are the steps for configuring policy in Windows Network Policy Server to support EAP-TLS.
Creating a Connection Request Policy to support IEEE 802.11 wireless connections.
- Open the Network Policy Server console.
- Navigate to NPS(Local)>Policies>Connection Request Policies.
- Right click Connection Request Policies and select New.
- On Specify Connection Policy Name and Connection Type enter a Policy name: and click Next.
- On Specify Conditions click Add.
- Select NAS Port Type as a condition.
- For NAS Port Type check Wireless - IEEE 802.11 and Wireless - Other click OK.
- Click Next.
- On Specify Connection Request Forwarding leave the defaults and click Next.
- On Specify Authentication Methods leave the defaults and click Next.
- On Configure Settings click Next.
- Review the settings On Completing Connection Request Policy Wizard and click Finish.
- Right click the Connection Policy created and select Move up so its processing order is before any other policies.
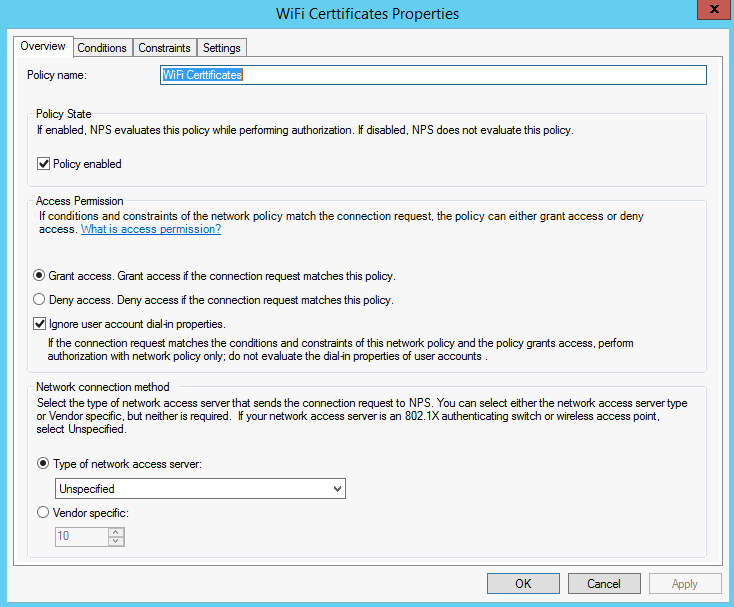
Creating a Network Policy to support EAP-TLS as the authentication method for IEEE 802.11 wireless connections.
- Right click Network Policies and select New.
- On Specify Network Policy Name and Connection Type enter a Policy name: and click Next.
- On Specify Conditions click Add.
- Select NAS Port Type as a condition.
- For NAS Port Type check Wireless - IEEE 802.11 and Wireless - Other click OK.
- Click Next.
- On Specify Access Permissions make sure Access granted is selected and click Next.
- On Configure Authentication Methods click Add and choose Microsoft: Smart Card or other certificate for Add EAP and click OK.
- Uncheck any boxes under Less secure authentication methods.
- Select Microsoft: Smart Card or other certificate for EAP types and click Edit.
- Verify the Certificate issued to: drop down shows the correct certificate and issuer which is the Active Directory CA server. Then click OK.
- Click Next.
- On Configure Constraints click Next.
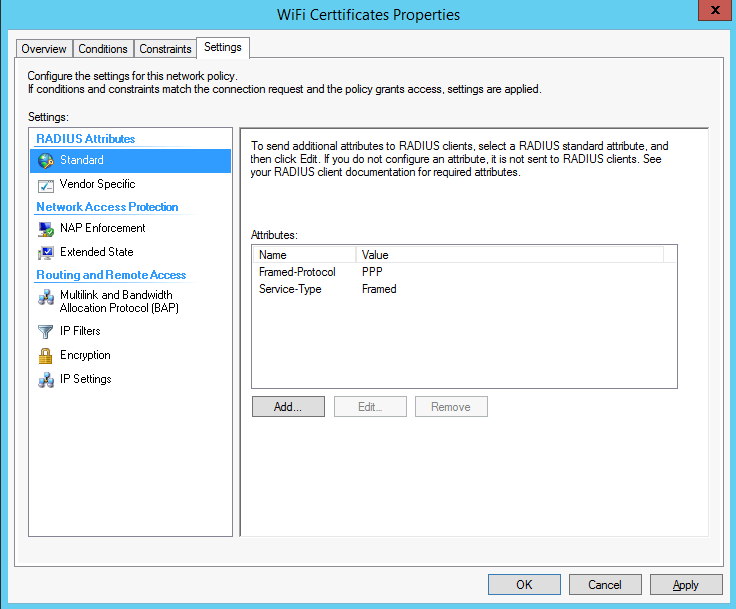
- On Configure Settings choose NAP Enforcement.
- Under Auto-Remediation, uncheck the box Auto-remediation of client computers and click Next.
- Review the settings on Completing New Network Policy and Click Finish.
- Right click the Network Policy created and select Move up so its processing order is before any other policies.
Here are screenshots for NPS Policy:
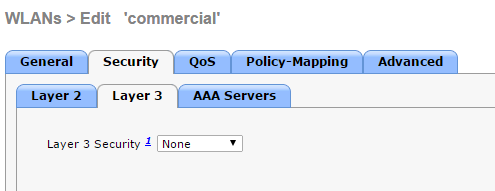
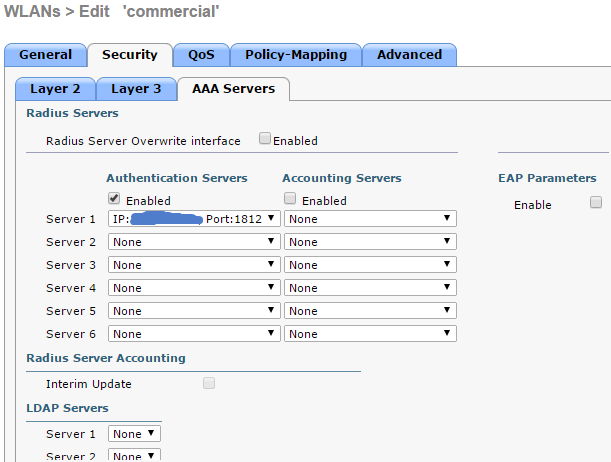
4. WLC Configuration
5. DHCP Option 43 configuration
When you are installing a Layer 3 access point on a different subnet than the Cisco wireless LAN controller, be sure that a DHCP server is reachable from the subnet on which you will be installing the access point, and that the subnet has a route back to the Cisco wireless LAN controller. Also be sure that the route back to the Cisco wireless LAN controller has destination UDP ports 5246 and 5247 open for CAPWAP communications. Ensure that the route back to the primary, secondary, and tertiary wireless LAN controller allows IP packet fragments. Finally, be sure that if address translation is used, that the access point and the Cisco wireless LAN controller have a static 1-to-1 NAT to an outside address. (Port Address Translation is not supported.)
You can use DHCP Option 43 to provide a list of controller IP addresses to the access points, enabling them to find and join a controller.
The access point must be able to find the IP address of the controller. This can be resolved by DHCP Option 43's configuration.
option 43 hex <hex string>
Type is always f1(hex). Length is the number of controller management IP addresses times 4 in hex. Value is the IP address of the controller listed sequentially in hex.
For example, suppose that there are two controllers with management interface IP addresses, 10.126.126.2 and 10.127.127.2. The type is f1(hex). The length is 2 * 4 = 8 = 08 (hex). The IP addresses translate to 0a7e7e02 and 0a7f7f02. Assembling the string then yields f1080a7e7e020a7f7f02. The resulting Cisco IOS command added to the DHCP scope is option 43 hex f1080a7e7e020a7f7f0
IP Address to Hex Converter has a online converter to help you to convert IP address to Hex.Reference:
- 1. Cisco WLC DHCP Option 43
- 2. WiFi Certificate Based Authentication
- 3. EAP-TLS-based Authenticated Wireless Access Design
- 4. RADIUS: Creating a Policy in NPS to support EAP-TLS authentication
- 5. Microsoft NPS as a RADIUS Server for WiFi Networks: Dynamic VLAN Assignment
- 6. Inexpensive 802.1x Solutions
- 7. Configuring NPS on Server 2012 with Cisco WLC: Part 1
- 8. IP Address to Hex Converter
- 9. 亁颐堂现任明教教主融合网络CCNA.第一天.融合网络概述.1













No comments:
Post a Comment