Some other related posts:
- Troubleshooting Cisco IPSec Site to Site VPN - "reason: Unknown delete reason!" after Phase 1 Completed
- Troubleshooting Cisco IPSec Site to Site VPN - "IPSec policy invalidated proposal with error 32"
- Troubleshooting Cisco IPSec Site to Site VPN - "QM Rejected"
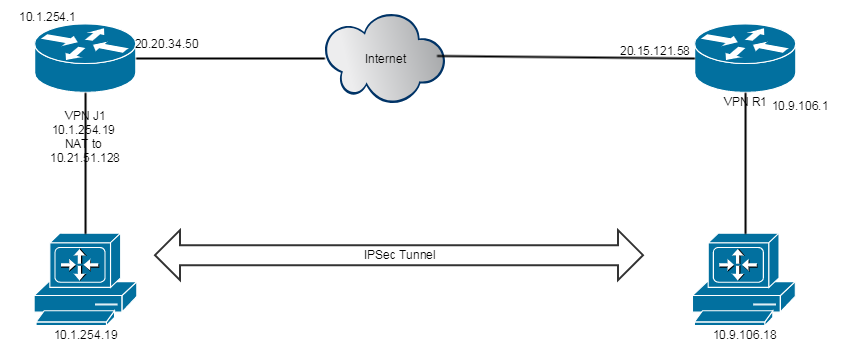
Diagram
1. Enabled Debugging on Cisco IOS Router
vpn-R1#debug crypto ipsec
Crypto IPSEC debugging is on
vpn-R1#debug crypto isakmp
Crypto ISAKMP debugging is on
vpn-R1#debug crypto engine
Crypto Engine debugging is on
vpn-R1#terminal monitor
2. Debugging results
It shows invalidated proposal and ISAKMP deleted node with reason "QM rejected"
003345: Sep 5 10:49:31.279 EDT: ISAKMP (1060): received packet from 20.20.34.50 dport 500 sport 500 Global (R) QM_IDLE 003346: Sep 5 10:49:31.279 EDT: ISAKMP: set new node 1450843075 to QM_IDLE 003347: Sep 5 10:49:31.279 EDT: ISAKMP:(1060): processing HASH payload. message ID = 1450843075 003348: Sep 5 10:49:31.279 EDT: ISAKMP:(1060): processing SA payload. message ID = 1450843075 003349: Sep 5 10:49:31.279 EDT: ISAKMP:(1060):Checking IPSec proposal 1 003350: Sep 5 10:49:31.279 EDT: ISAKMP: transform 0, ESP_3DES 003351: Sep 5 10:49:31.279 EDT: ISAKMP: attributes in transform: 003352: Sep 5 10:49:31.279 EDT: ISAKMP: authenticator is HMAC-SHA 003353: Sep 5 10:49:31.279 EDT: ISAKMP: group is 2 003354: Sep 5 10:49:31.279 EDT: ISAKMP: SA life type in seconds 003355: Sep 5 10:49:31.279 EDT: ISAKMP: SA life duration (VPI) of 0x0 0x0 0xE 0x10 003356: Sep 5 10:49:31.279 EDT: ISAKMP: encaps is 1 (Tunnel) 003357: Sep 5 10:49:31.279 EDT: ISAKMP:(1060):atts are acceptable. 003358: Sep 5 10:49:31.279 EDT: IPSEC(validate_proposal_request): proposal part #1 003359: Sep 5 10:49:31.279 EDT: IPSEC(validate_proposal_request): proposal part #1, (key eng. msg.) INBOUND local= 200.153.121.58:0, remote= 20.20.34.50:0, local_proxy= 10.9.106.18/255.255.255.255/256/0, remote_proxy= 10.21.51.128/255.255.255.255/256/0, protocol= ESP, transform= esp-3des esp-sha-hmac (Tunnel), lifedur= 0s and 0kb, spi= 0x0(0), conn_id= 0, keysize= 0, flags= 0x0 003361: Sep 5 10:49:31.279 EDT: Crypto mapdb : proxy_match src addr : 10.9.106.18 dst addr : 10.21.51.128 protocol : 0 src port : 0 dst port : 0 ....... 003369: Sep 5 10:49:31.283 EDT: map_db_find_best did not find matching map 003370: Sep 5 10:49:31.283 EDT: IPSEC(ipsec_process_proposal): proxy identities not supported 003371: Sep 5 10:49:31.283 EDT: ISAKMP:(1060): IPSec policy invalidated proposal with error 32 003372: Sep 5 10:49:31.283 EDT: ISAKMP:(1060): phase 2 SA policy not acceptable! (local 20.15.121.58 remote 20.20.34.50) 003373: Sep 5 10:49:31.283 EDT: ISAKMP: set new node -2087949406 to QM_IDLE 003374: Sep 5 10:49:31.283 EDT: ISAKMP:(1060):Sending NOTIFY PROPOSAL_NOT_CHOSEN protocol 3 spi 739556696, message ID = 2207017890 003375: Sep 5 10:49:31.283 EDT: ISAKMP:(1060): sending packet to 20.20.34.50 my_port 500 peer_port 500 (R) QM_IDLE 003376: Sep 5 10:49:31.283 EDT: ISAKMP:(1060):Sending an IKE IPv4 Packet. 003377: Sep 5 10:49:31.283 EDT: ISAKMP:(1060):purging node -2087949406 003378: Sep 5 10:49:31.283 EDT: ISAKMP:(1060):deleting node 1450843075 error TRUE reason "QM rejected" 003379: Sep 5 10:49:31.283 EDT: ISAKMP:(1060):Node 1450843075, Input = IKE_MESG_FROM_PEER, IKE_QM_EXCH vpn-router# 003380: Sep 5 10:49:31.283 EDT: ISAKMP:(1060):Old State = IKE_QM_READY New State = IKE_QM_READY
003382: Sep 5 10:50:21.284 EDT: ISAKMP:(1060):purging node 1450843075
3. Checking configuration
Cisco Router's crypto map
vpn-router#show crypto map
Interfaces using crypto map NiStTeSt1:
Crypto Map IPv4 "vpn" 20 ipsec-isakmp
Description: VPN to C
Peer = 20.20.34.50
Extended IP access list C-VPN-List
access-list C-VPN-List permit ip host 10.9.106.18 host 10.1.254.19
Current peer: 20.20.34.50
Security association lifetime: 4608000 kilobytes/3600 seconds
Responder-Only (Y/N): N
PFS (Y/N): Y
DH group: group2
Mixed-mode : Disabled
Transform sets={
Conductor: { esp-3des esp-sha-hmac } ,
}
Peer Juniper SRX 550 configuraiton:
set interfaces st0 unit 22 description Cisco-R
set security ike policy ike-policy-Cisco-R mode main
set security ike policy ike-policy-Cisco-R proposals ike-proposal-Padrao
set security ike policy ike-policy-Cisco-R pre-shared-key ascii-text "$APfTz0O"
set security ike gateway ike-gate-Cisco-R ike-policy ike-policy-Cisco-R
set security ike gateway ike-gate-Cisco-R address 20.15.121.58
set security ike gateway ike-gate-Cisco-R remote-identity inet 20.15.121.58
set security ike gateway ike-gate-Cisco-R external-interface reth0.0
set security ipsec vpn ipsec-vpn-Cisco-R bind-interface st0.22
set security ipsec vpn ipsec-vpn-Cisco-R ike gateway ike-gate-Cisco-R
set security ipsec vpn ipsec-vpn-Cisco-R ike proxy-identity local 10.21.51.128/32
set security ipsec vpn ipsec-vpn-Cisco-R ike proxy-identity remote 10.9.106.18/32
set security ipsec vpn ipsec-vpn-Cisco-R ike proxy-identity service any
set security ipsec vpn ipsec-vpn-Cisco-R ike ipsec-policy ipsec-policy-P
set security ipsec vpn ipsec-vpn-Cisco-R establish-tunnels immediately
set security ike proposal ike-proposal-P authentication-method pre-shared-keys
set security ike proposal ike-proposal-P dh-group group2
set security ike proposal ike-proposal-P authentication-algorithm sha1
set security ike proposal ike-proposal-P encryption-algorithm 3des-cbc
set security ike proposal ike-proposal-P lifetime-seconds 28800
set security ipsec policy ipsec-policy-P perfect-forward-secrecy keys group2
set security ipsec policy ipsec-policy-P proposals ipsec-proposal-Padrao
set security ipsec proposal ipsec-proposal-P protocol esp
set security ipsec proposal ipsec-proposal-P authentication-algorithm hmac-sha1-96
set security ipsec proposal ipsec-proposal-P encryption-algorithm 3des-cbc
set security ipsec proposal ipsec-proposal-P lifetime-seconds 3600
Cisco IOS Router 1900 Configuration:
crypto isakmp policy 2
encr 3des
authentication pre-share
group 2
lifetime 28800
!
crypto isakmp key 76tyYuty!2@ address 20.13.194.17
!crypto isakmp aggressive-mode disable
crypto ipsec transform-set C esp-3des esp-sha-hmac
mode tunnel
crypto map vpn 20 ipsec-isakmp
description VPN to C
set peer 20.20.34.50
set transform-set Conductor
set pfs group2
match address C-VPN-List
ip access-list extended C-VPN-List
permit ip host 10.9.106.18 host 10.1.254.19
interface GigabitEthernet0/0
ip address 20.15.121.58 255.255.255.248
duplex auto
speed auto
crypto map vpn
Solution:
It clearly shows access-list not matching on both end. Juniper SRX has a NAT from 10.1.254.19 to 10.21.51.128. Cisco router only knows their Internal IP 10.1.254.19. Once Cisco router changed access-list to match Juniper. Tunnel is up right away.







At the moment the Inside and DMZ nat are Outside interface (so when it goes out it uses 1.1.1.1) - my DMZ uses an outside DNS Server for name resolution which seems to be fine - I get an error message which looks like it cant communicate to outside address - if i try the samething from internet, it works but i need it to work from DMZ interface as well.. andy michael
ReplyDelete