I put some of useful commands or configurations in following two posts:
- FortiOS Configuration for FortiGate Firewalls (Commands) 1
- FortiOS Configuration for FortiGate Firewalls (Commands) 2
1. FGT30D # config system interface
FGT30D (interface) # show config system interface edit "wan" set ip 10.99.142.1 255.255.255.0 set allowaccess ping https ssh snmp http fgfm set type physical set snmp-index 2 next ..... edit "lan" set ip 192.168.100.1 255.255.255.0 set allowaccess ping https ssh http fgfm capwap set type physical set snmp-index 1 next end
FWF60D # show | grep interface config system switch-interface config system interface set alias "SSL VPN interface" set monitor-interface "wan1" set interface "lan" set associated-interface "ssl.root" set associated-interface "lan" set associated-interface "lan"
FWF60D # show | grep -f DMZ2 config system interface edit "wan2" set vdom "root" set ip 172.17.3.1 255.255.255.0 set allowaccess ping https http fgfm set type physical set alias "DMZ2" <--- set role dmz set snmp-index 3 next end
| grep can be used to filter the output to search the string you want.
| grep -f will show you the whole section which matches your searching string.
| grep -f will show you the whole section which matches your searching string.
2. Change System Hostname
FGT30D # config system globalFGT30D (global) # set hostname FGT30D
FGT30D (global) # end
3. Configure System DHCP Server
on Interface "lan":FGT30D # config system dhcp server config system dhcp server edit 1 set default-gateway 192.168.100.1 set dns-service default set interface "lan" config ip-range edit 1 set end-ip 192.168.100.200 set start-ip 192.168.100.80 next end set netmask 255.255.255.0 next end
Get list of DHCP Leased IP’s in Fortigate for lan interface
FWF60D # execute dhcp lease-list lan lan IP MAC-Address Hostname VCI Expiry 192.168.2.165 a8:5c:2c:4a:8f:c7 iPhone Sun Sep 2 13:07:04 2018 192.168.2.54 e4:98:d6:83:ef:6e iPad Sun Sep 2 13:05:39 2018 192.168.2.53 d0:c1:93:02:1d:a0 udhcp 1.10.4 Sun Sep 2 12:56:34 2018 192.168.2.51 02:0f:b5:c9:54:23 H-J-Dell-L1 MSFT 5.0 Sun Sep 2 12:56:14 2018 192.168.2.52 02:0f:b5:73:26:55 ESP_732655 Sun Sep 2 12:52:23 2018 FWF60D4614014474 #
From Web GUI:
4. Configure Firewall Policy
FGT30D # config firewall policy
config firewall policy
edit 1
set srcintf "lan"
set dstintf "wan"
set srcaddr "all"
set dstaddr "all"
set action accept
set schedule "always"
set service "ALL"
set nat enable
next
end
5. Configure static gateway
FGT30D # config router static
config router static
edit 1
set device "wan"
set gateway 10.99.142.6
next
end
FGT30D3X1401796 $ conf router static FGT30D3X1401796 (static) $ edit 2 new entry '2' added FGT30D3X1401796 (2) $ set device "lan" FGT30D3X1401796 (2) $ set dst 10.9.9.0 255.255.255.0 FGT30D3X1401796 (2) $ set gateway 10.9.13.1 FGT30D3X1401796 (2) $ end
6. Configure system DNS host
FGT30D # config system dnsconfig system dns
set primary 208.91.112.53
set secondary 208.91.112.52
end
Configure FortiGate as DNS Server :
6.1 Enable DNS Database Feature
6.2 Configure DNS forwarding to system DNS
7. Set System Users
FGT30D # config system adminconfig system admin
edit admin
set password <psswrd>
config system admin
edit "admin"
set accprofile "super_admin"
....
set password ENC AK1TDEt3tvzlnXWgK7ZjkFDgEisgltyWyK2/lnOYtvcl28=
next
edit "superadmin1"
set accprofile "super_admin"
....
set password ENC AK1eDVLPbT+qARqmQ5r0ituEhnmu9xVwdAbo2puf9TZofo=
next
edit "testadmin"
set accprofile "prof_admin"
set password ENC AK1JB0gM4GKvhld20nMmfFbhnictGo/+oUIqAaGTGlb+vg=
next
end
8. Configure Syslog Settings
config log syslogd(2|3) setting
set status enable
set server 10.99.1.1
set port 514
set facility user
end
diagnose log test // Test logging
9. Execure Command - Ping
FGT30D # execute ping www.google.ca PING www.google.ca (173.194.46.111): 56 data bytes 64 bytes from 173.194.46.111: icmp_seq=0 ttl=57 time=20.7 ms 64 bytes from 173.194.46.111: icmp_seq=1 ttl=57 time=22.7 ms 64 bytes from 173.194.46.111: icmp_seq=2 ttl=57 time=20.6 ms --- www.google.ca ping statistics --- 3 packets transmitted, 3 packets received, 0% packet loss round-trip min/avg/max = 20.6/21.3/22.7 ms
Set Ping Source:
FGT30D # execute ping-options source 192.168.1.1
FGT30D # execute ping-options viewPing Options:
Repeat Count: 5
Data Size: 56
Timeout: 2
Interval: 1
TTL: 64
TOS: 0
DF bit: unset
Source Address: 192.168.1.1
Pattern:
Pattern Size in Bytes: 0
Validate Reply: no
Note: ping-options will reset when session closed
10. Time Out Configuration
FGT30D3X13001834 # show system session-ttl
config system session-ttl set default 30000 config port edit 23 set timeout 72000 next end end |
To avoid the possibility of an administrator walking away from the management computer and leaving it exposed to unauthorized personnel, you can add an idle time-out. That is, if the web-based manager is not used for a specified amount of time, the FortiGate unit will automatically log the administrator out. To continue their work, they must log in again.
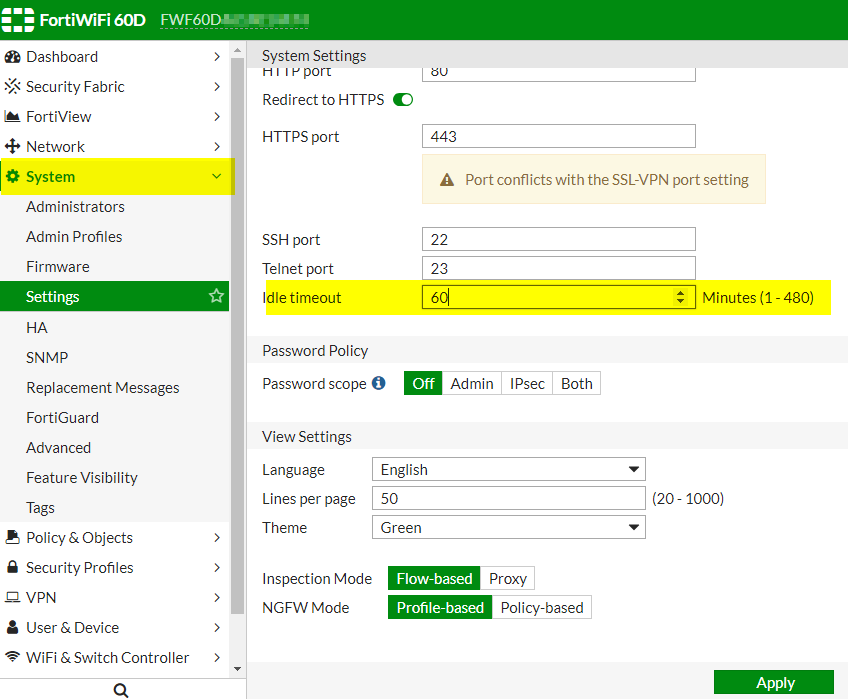 The time-out can be set as high as 480 minutes, or eight hours, although this is not recommend.
The time-out can be set as high as 480 minutes, or eight hours, although this is not recommend.To set the idle time out, go to System > Settings and enter the amount of time for the Idle Timeout. A best practice is to keep the default of 5 min.
When logging into the console using SSH, the default time of inactivity to successfully log into the FortiGate unit is 120 seconds (2 minutes). You can configure the time to be shorter by using the CLI to change the length of time the command prompt remains idle before the FortiGate unit will log the administrator out. The range can be between 10 and 3600 seconds. To set the logout time enter the following CLI commands:
config system global
set admin-ssh-grace-time <number_of_seconds>
end
11. Backup/Restore Configuration to Flash
FGT30D # execute backup config flash
Please wait...
Config backed up to flash disk done.
Setting timestamp
FGT30D # execute revision list config
Last Firmware Version: V0.0.0-build000-REL0
ID TIME ADMIN FIRMWARE VERSION COMMENT
1 2015-02-10 13:39:29 jn V5.0.0-build292-REL0
2 2015-02-10 13:42:15 jn V5.0.0-build292-REL0 20140210
Restore Configuration from Flash:
FGT30D # execute restore config flash <revision> Revision ID on the flash. FGT30D # execute restore config flash 2 This operation will overwrite the current settings! Do you want to continue? (y/n)y Please wait... Get config from local disk OK. File check OK.
12. Reset System to Factory
FGT60D # execute factoryreset This operation will reset the system to factory default! Do you want to continue? (y/n)y System is resetting to factory default... The system is going down NOW !! FGT60D # Please stand by while rebooting the system. Restarting system. FortiGate-60D (10:49-11.12.2014) Ver:04000024 Serial number: FGT60D4P14005710 CPU(00): 800MHz Total RAM: 2GB Initializing boot device... Initializing MAC... nplite#0 Please wait for OS to boot, or press any key to display configuration menu...... Booting OS... Reading boot image... 1278067 bytes. Initializing firewall... System is starting... |
13. Check Interface Status (Speed / Duplex)
FGT30D3X1502126 $ get system interface physical == [onboard] ==[lan] mode: static ip: 10.9.14.8 255.255.255.0 ipv6: ::/0 status: up speed: 1000Mbps (Duplex: full) ==[wan] mode: static ip: 10.9.16.8 255.255.255.0 ipv6: ::/0 status: up speed: 1000Mbps (Duplex: full) ==[modem] mode: pppoe ip: 0.0.0.0 0.0.0.0 ipv6: ::/0 status: down speed: n/a FGT30D3X1502126 $ get hardware nic lan Driver Name :Fortinet NP4Lite Driver Version :1.0.1 Admin :up Current_HWaddr 90:6c:ac:13:45:88 Permanent_HWaddr 90:6c:ac:13:45:88 Status :up Speed :1000 Duplex :Full Host Rx Pkts :1252679 Host Rx Bytes :91142924 Host Tx Pkts :88665 Host Tx Bytes :11744688 Rx Pkts :1211790 Rx Bytes :106073828 Tx Pkts :75589 Tx Bytes :111560468 rx_buffer_len :2048 Hidden :No cmd_in_list : 0 promiscuous : 1
FGT30D3X1502126 $ diag netlink interface list lan
if=lan family=00 type=1 index=3 mtu=1500 link=0 master=0
ref=16 state=start present fw_flags=8000 flags=up broadcast run allmulti multicast
Qdisc=pfifo_fast hw_addr=90:6c:ac:13:45:88 broadcast_addr=ff:ff:ff:ff:ff:ff
stat: rxp=1218030 txp=75593 rxb=106620201 txb=111560708 rxe=0 txe=0 rxd=0 txd=0 mc=0 collision=0
re: rxl=0 rxo=0 rxc=0 rxf=0 rxfi=0 rxm=0
te: txa=0 txc=0 txfi=0 txh=0 txw=0
misc rxc=0 txc=0 stop=0
input_type=0 state=6 arp_entry=5 refcnt=16
14. Time and Date, or NTP
To configure NTP via the CLI
To synchronize with an NTP server, enter the following commands:
config system global
set ntpsync enable
set timezone <timezone_index>
set ntpserver {<server_fqdn> | <server_ipv4>}
end
To manually set the date and time via the CLI
To manually configure the FortiWeb appliance’s system time and disable the connection to an NTP server, enter the following commands:
config system global
set ntpsync disable
set timezone <timezone_index>
set dst {enable | disable}
end
execute time 12:03:01
execute date 2016-10-09











No comments:
Post a Comment