This post is to record all steps to configure a ipsec site to site IPSec VPN tunnel between Palo Alto Firewall and Fortigate Firewall,
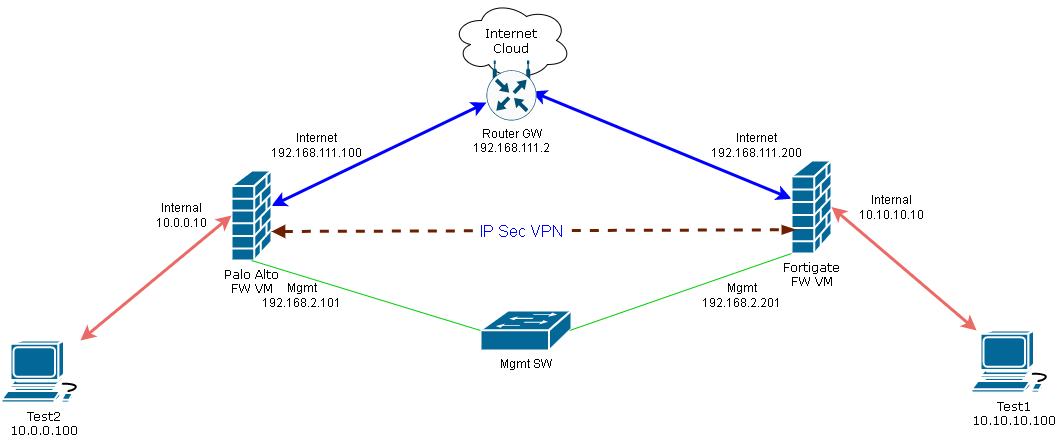
Diagram
Online Updated Diagram:Configure Basic settings of Palo Alto Firewall
More details can be found from following posts:1 Download Palo Alto Image
2 Import Image and Configure VM
3 Connect to Mgmt Interface
4 Configure Internal/Internet interfaces.
5 Configure Security Zone and Virtual Router
6 Configure Security policy and NAT
7 Test
Configure Basic settings of Fortigate Firewall
More details can be found from this post: https://blog.51sec.org/2022/01/download-and-launch-fortigate-virtual.html1 Download VM image
2 Import into VMWare Workstation lab environment
3 Configure static ip and http access for mgmt interface and using HTTP to connect to mgmt interface
4 Config LAN/WAN/DMZ interfaces
5 Config basic security policy and nat
6 TestConfigure VPN tunnel in Palo Alto Firewall
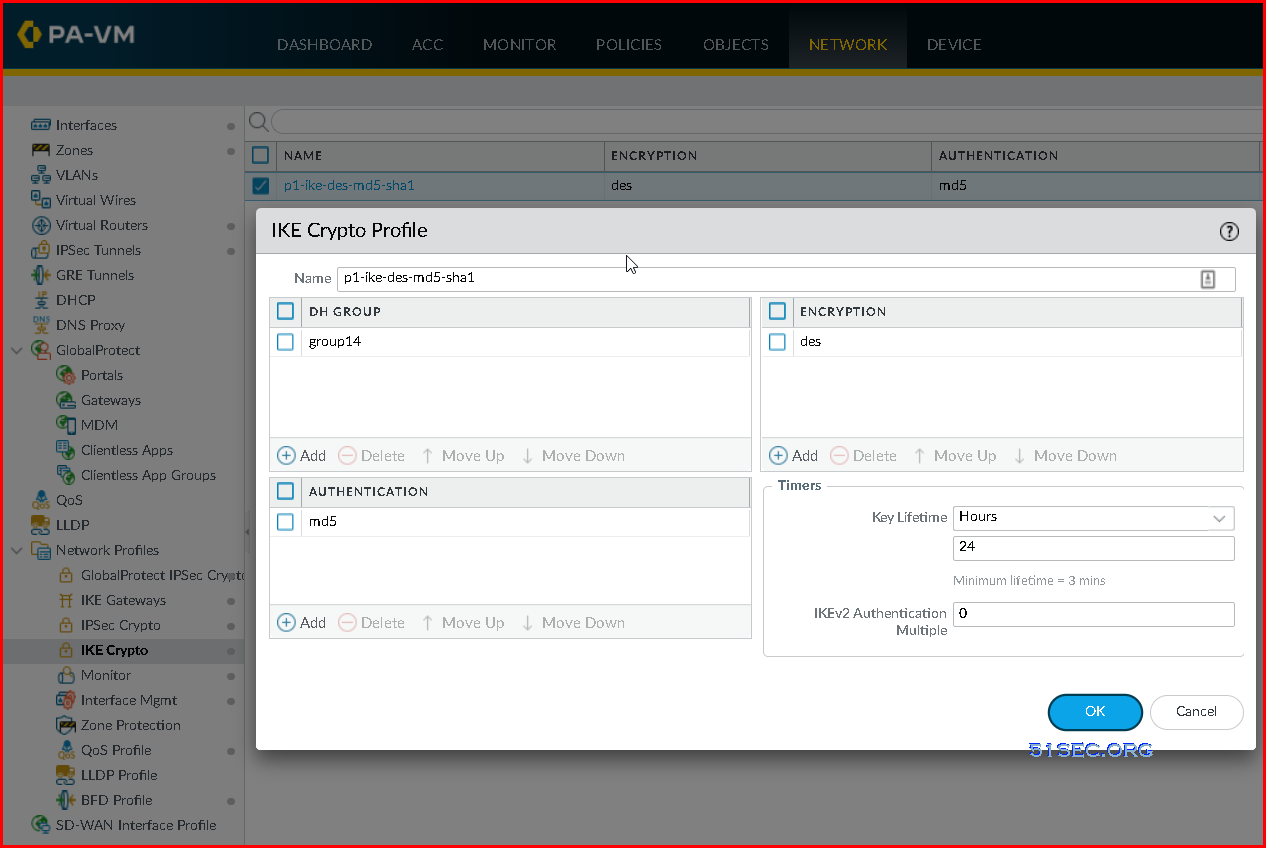
1 Create IKE Crypto Profile
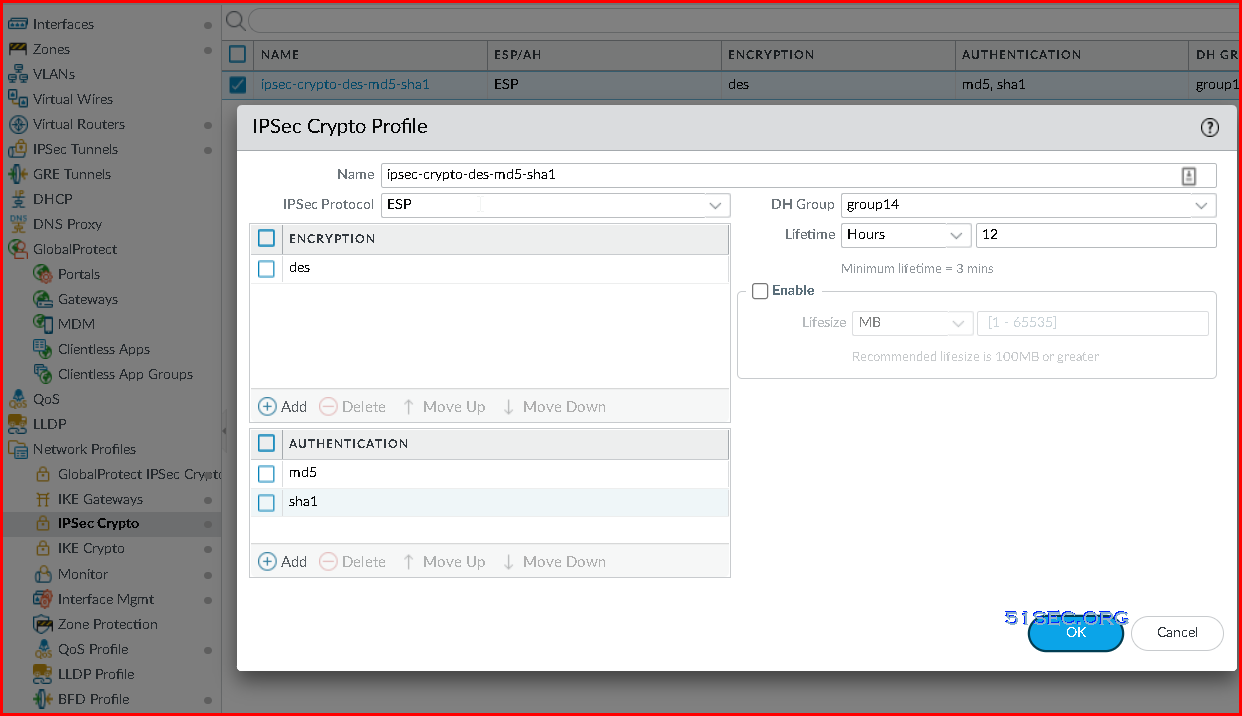
2 Create IPSec Crypto Profile
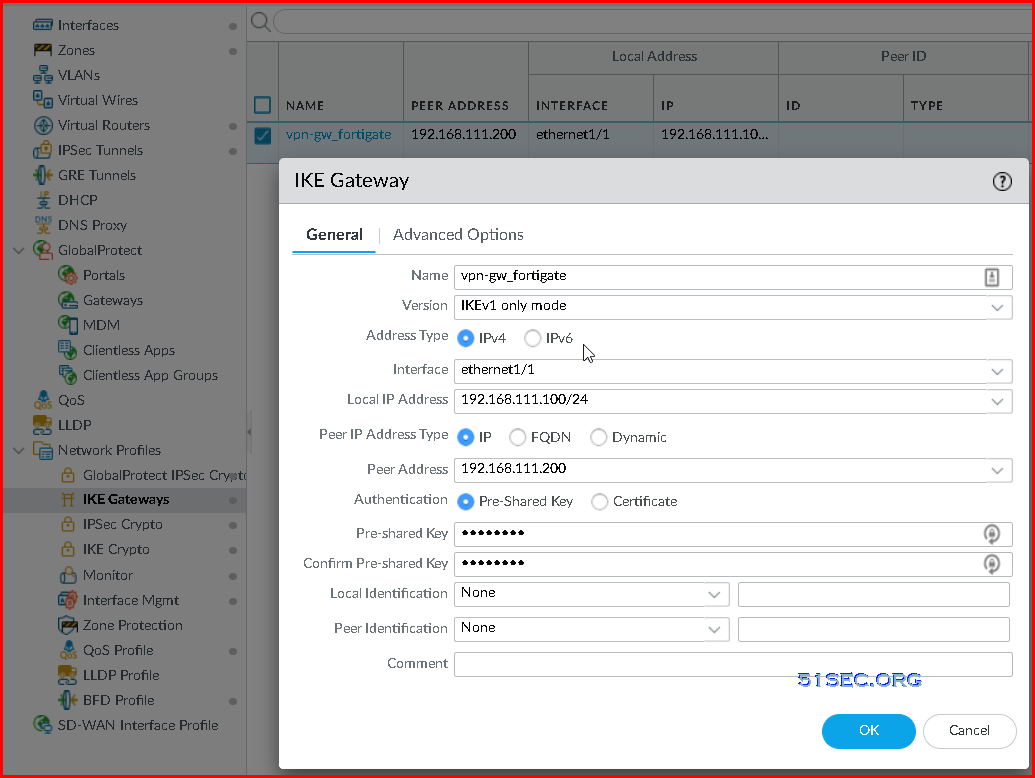
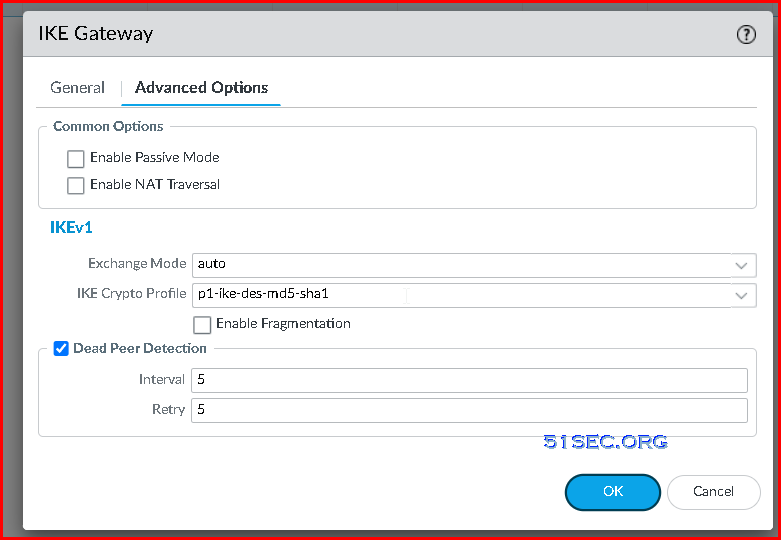
3 Create IKE Gateway
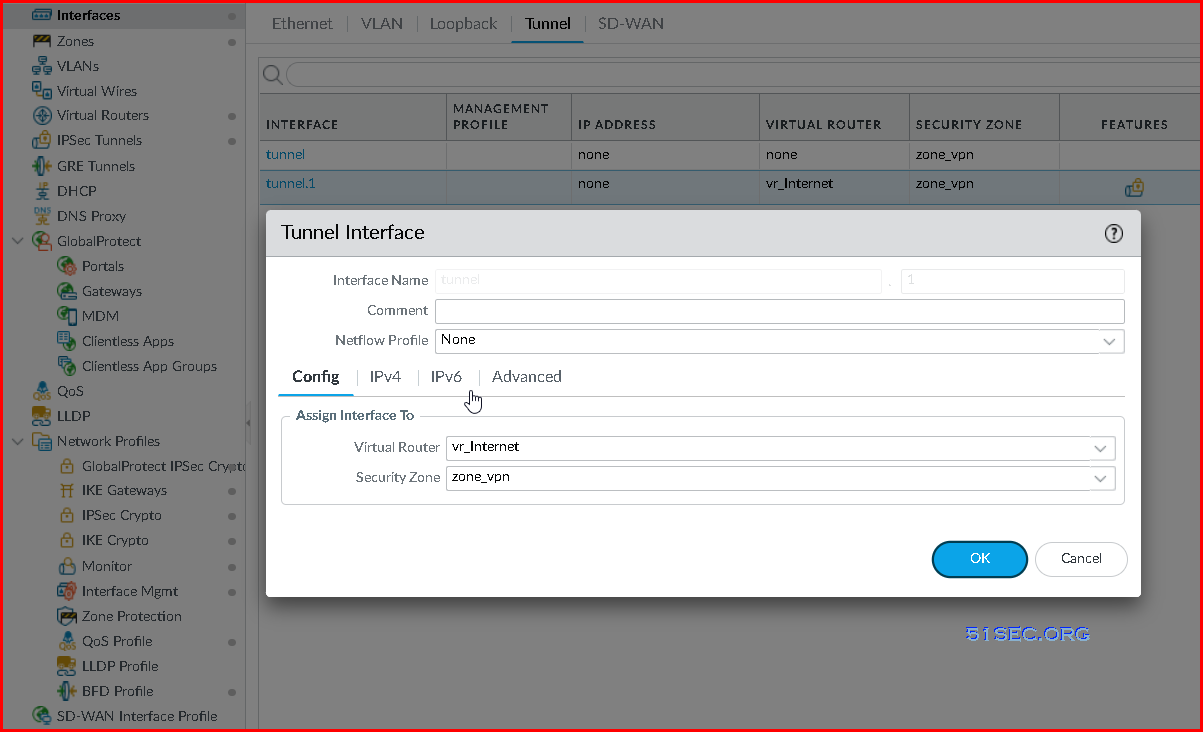
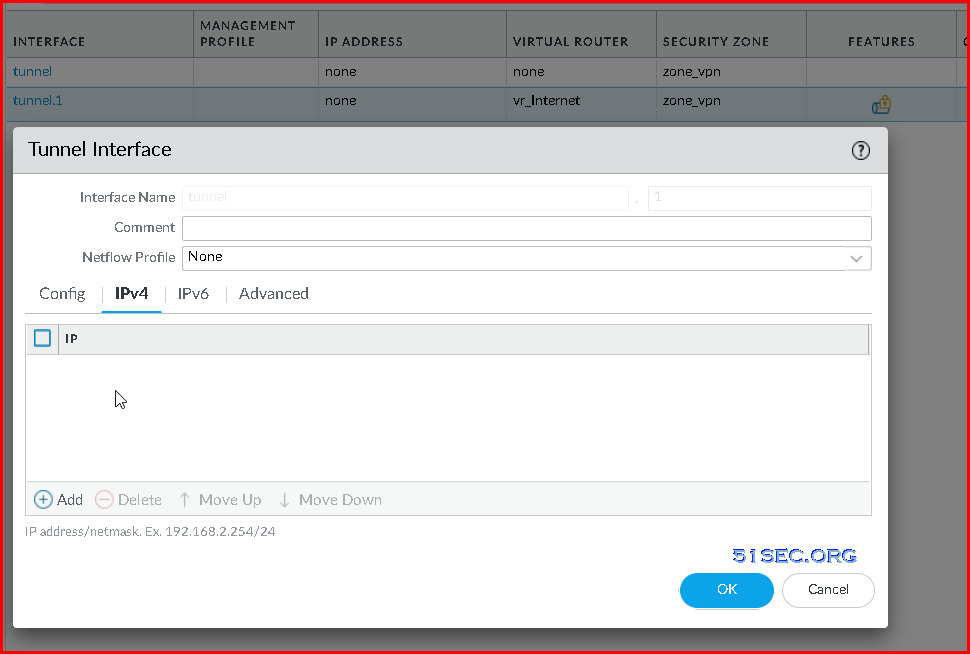
4 Create tunnel interface
You do not have to assign an ip address for your tunnel interface. But if assigned, it can be used to monitor tunnel.
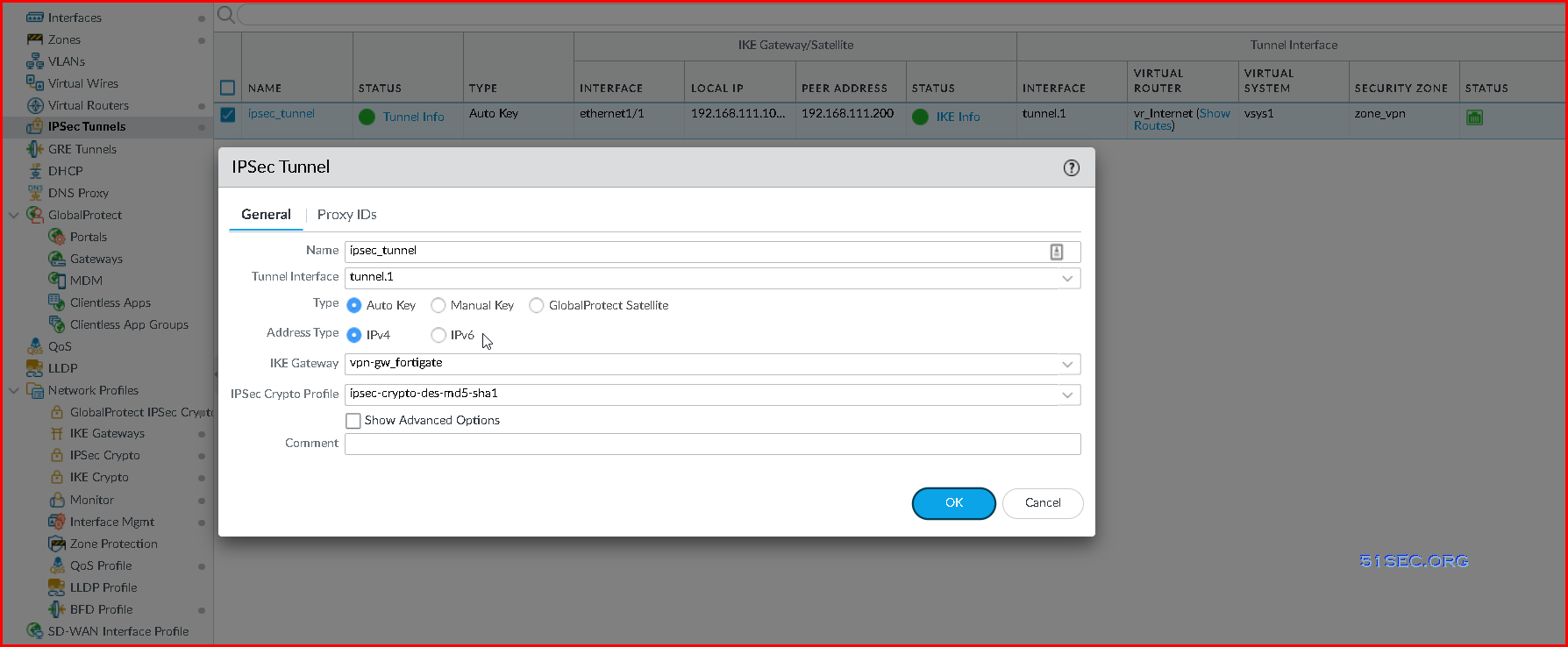
5 Create IPSec Tunnel
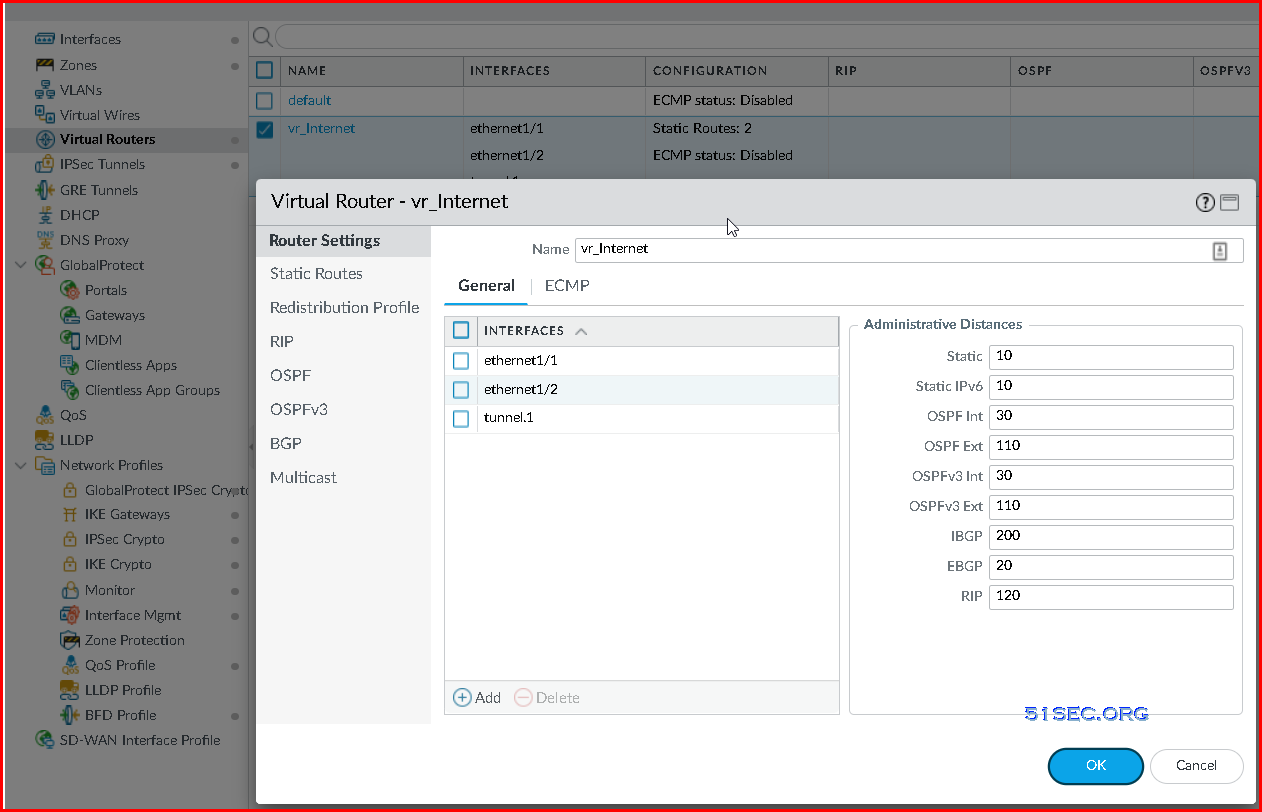
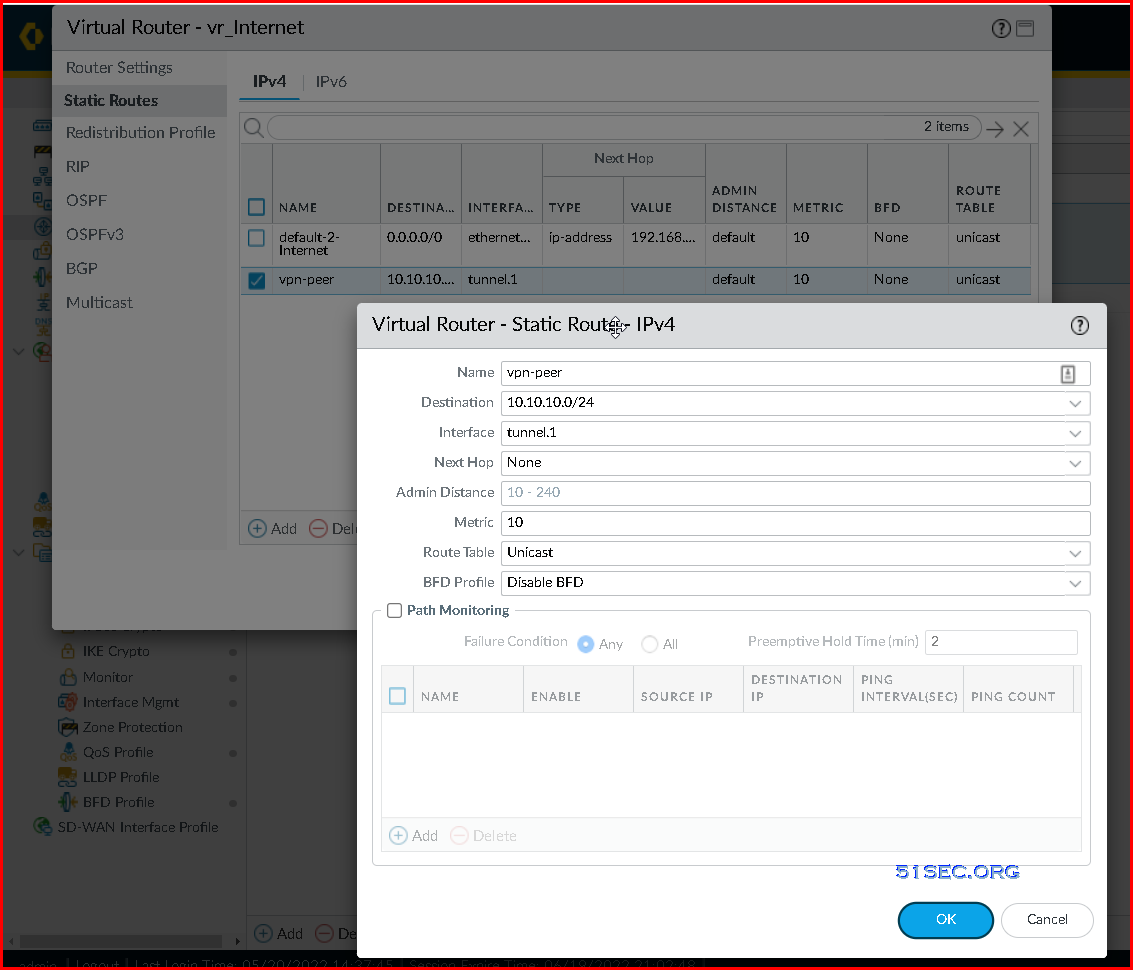
6 Virtual Router Static Route configuration
Depends on how you routing your traffic, after you add your tunnel interface into your virtual router, you might need to create a couple static routes.
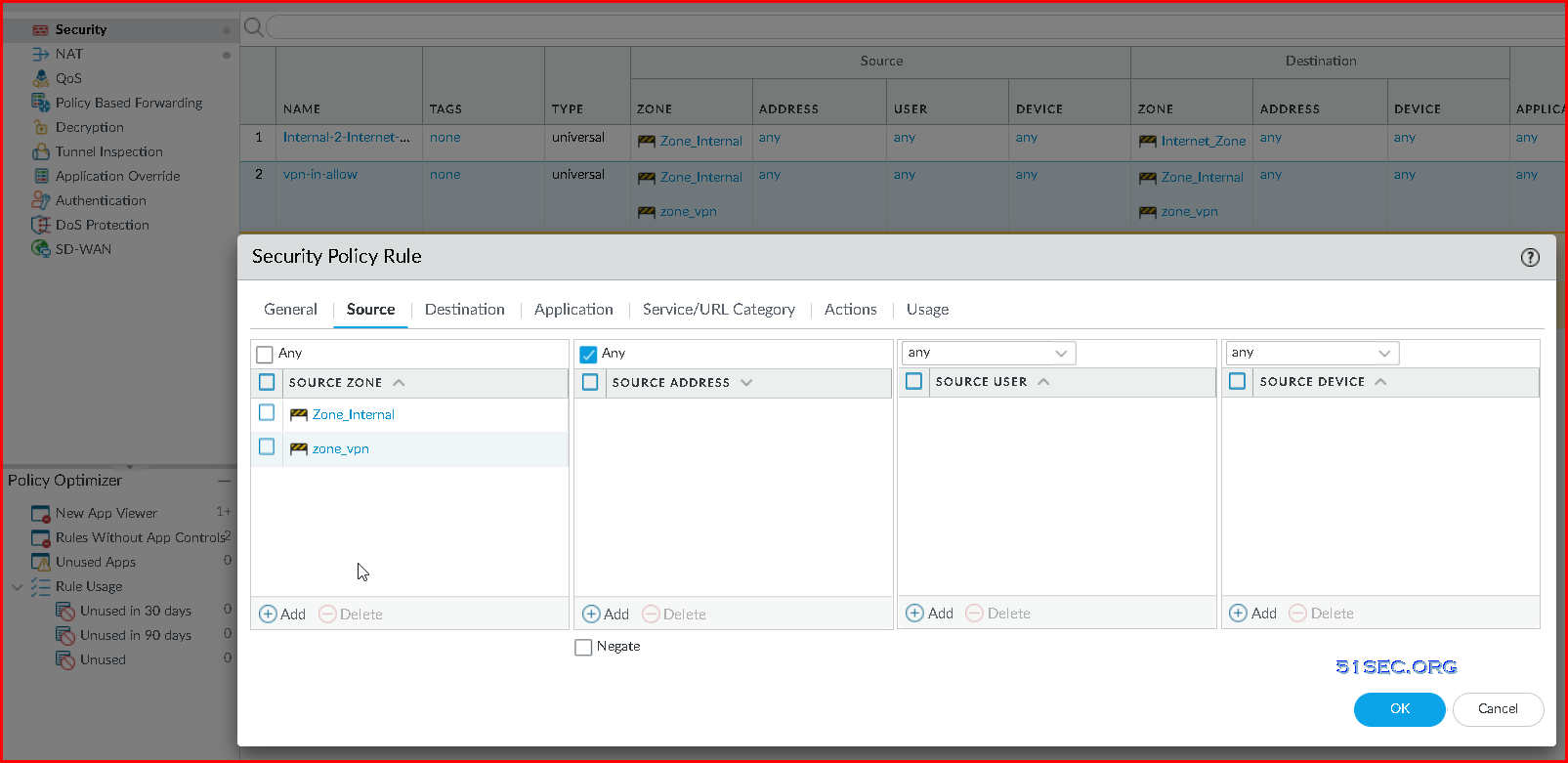
7 Create security policy rule to allow VPN networks to access each other.
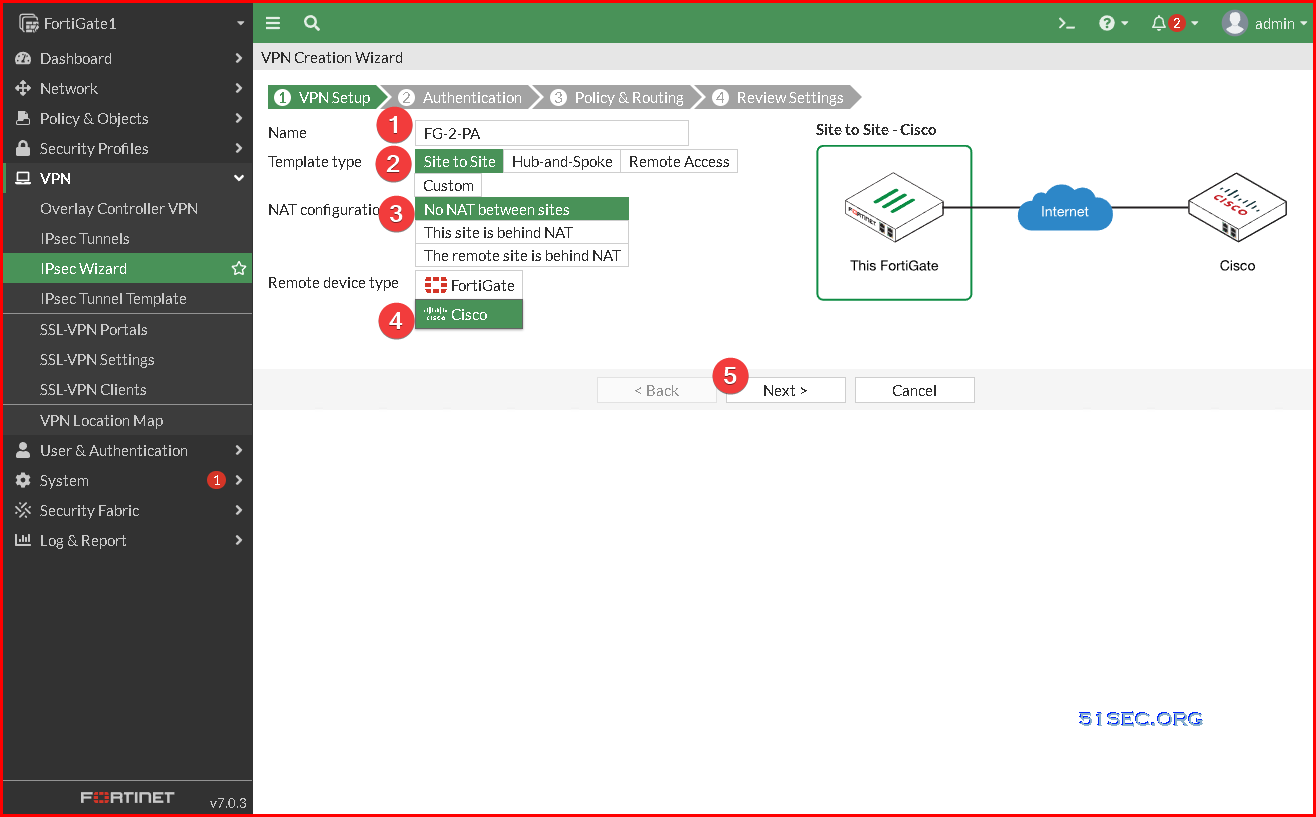
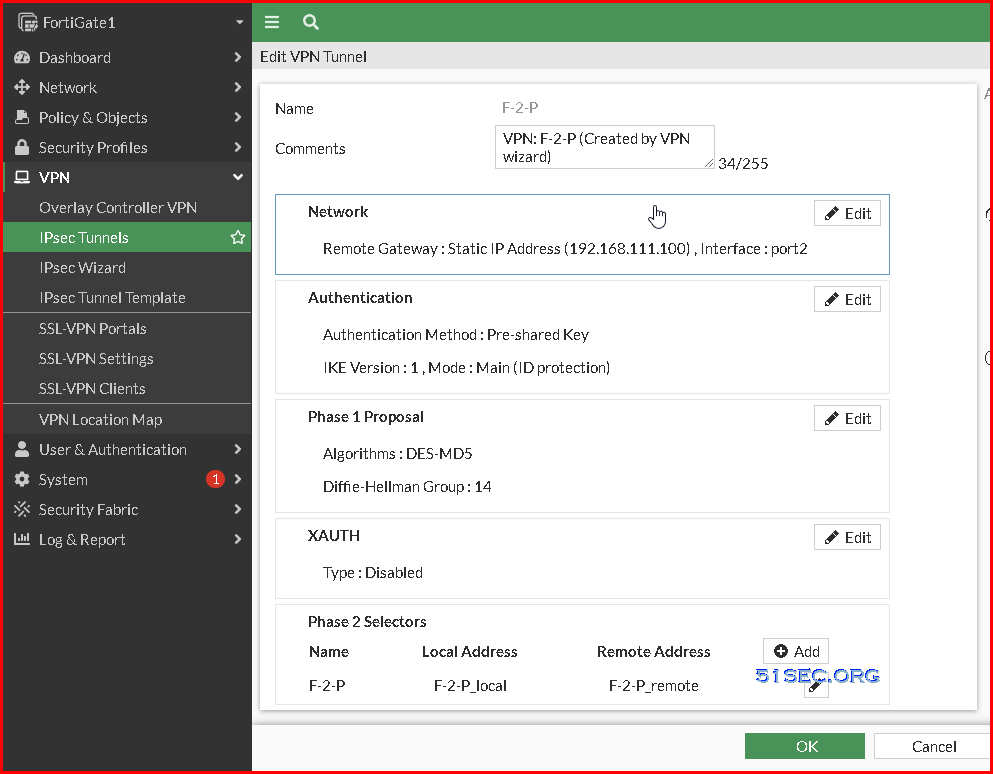
Configure VPN tunnel in Fortigate Firewall
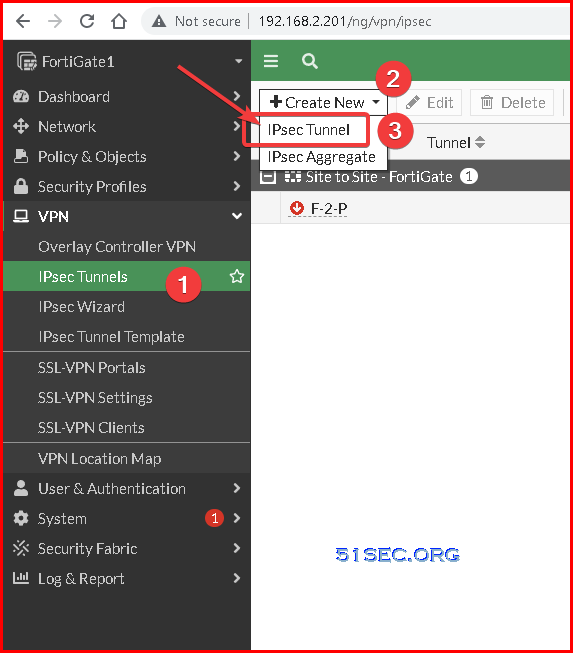
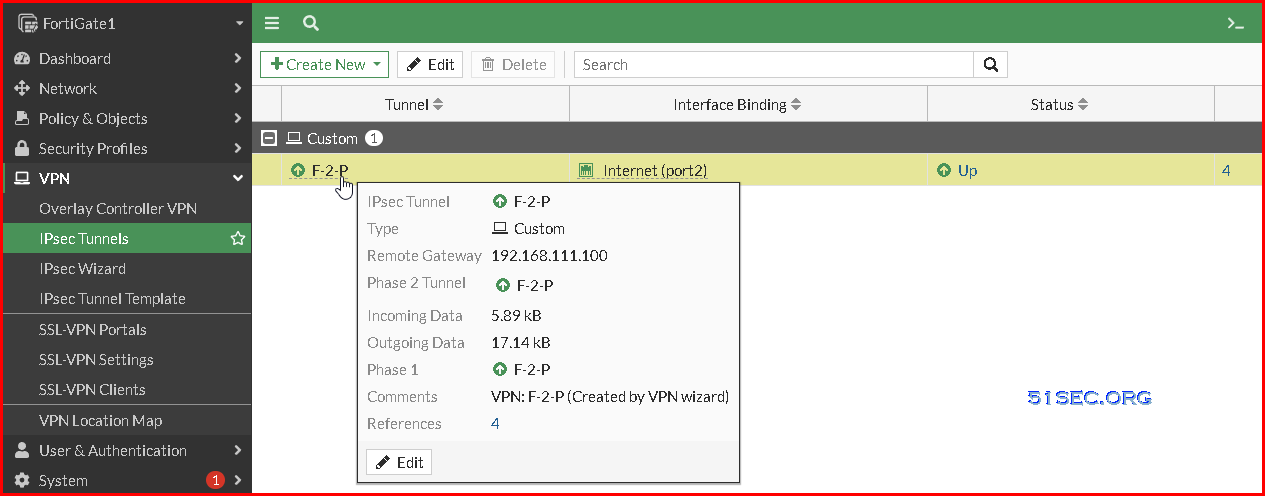
1 Go to VPN section, choose IPsec Tunnels and click Create New IPsec Tunnel
2 Start VPN setup. Put name, choose template type, if need NAT, and select remote device type
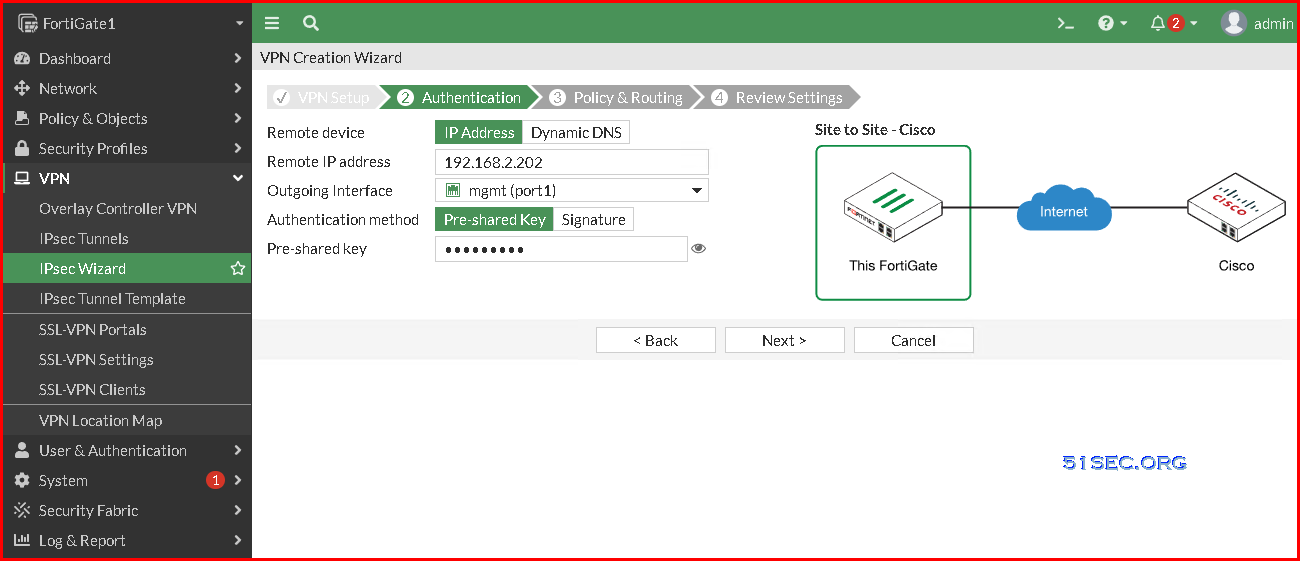
3 Configure Authentication method and remote gateway information
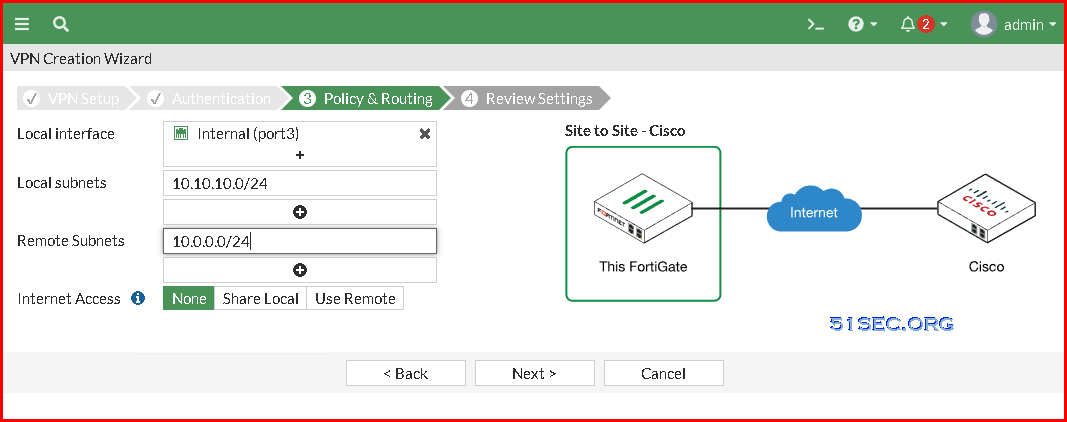
4 Choose local ip segment and configure remote ip segment. This traffic will be your interest traffic which will be sent to VPN tunnel.
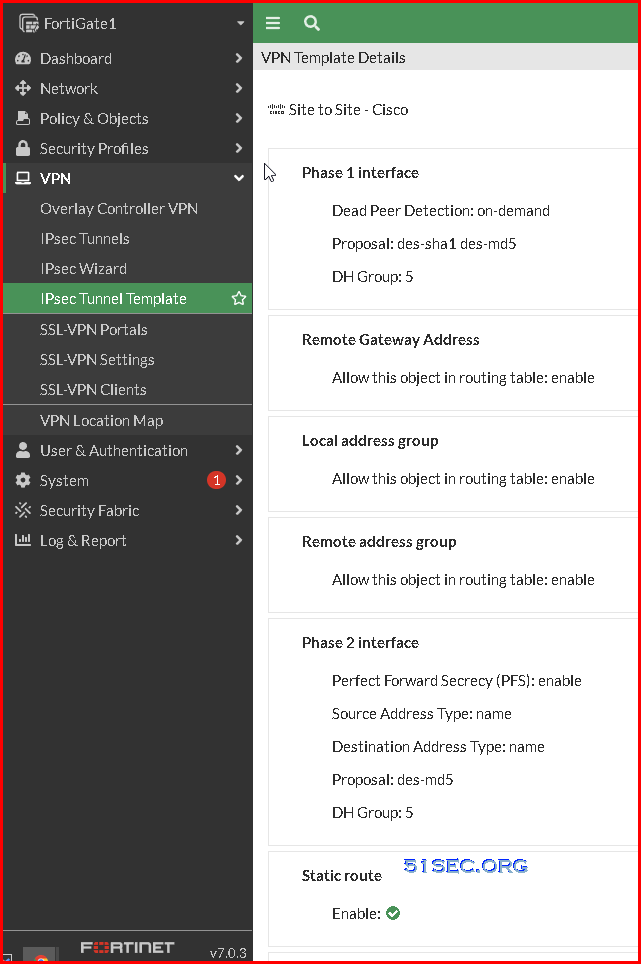
5 Review and create tunnel configuration
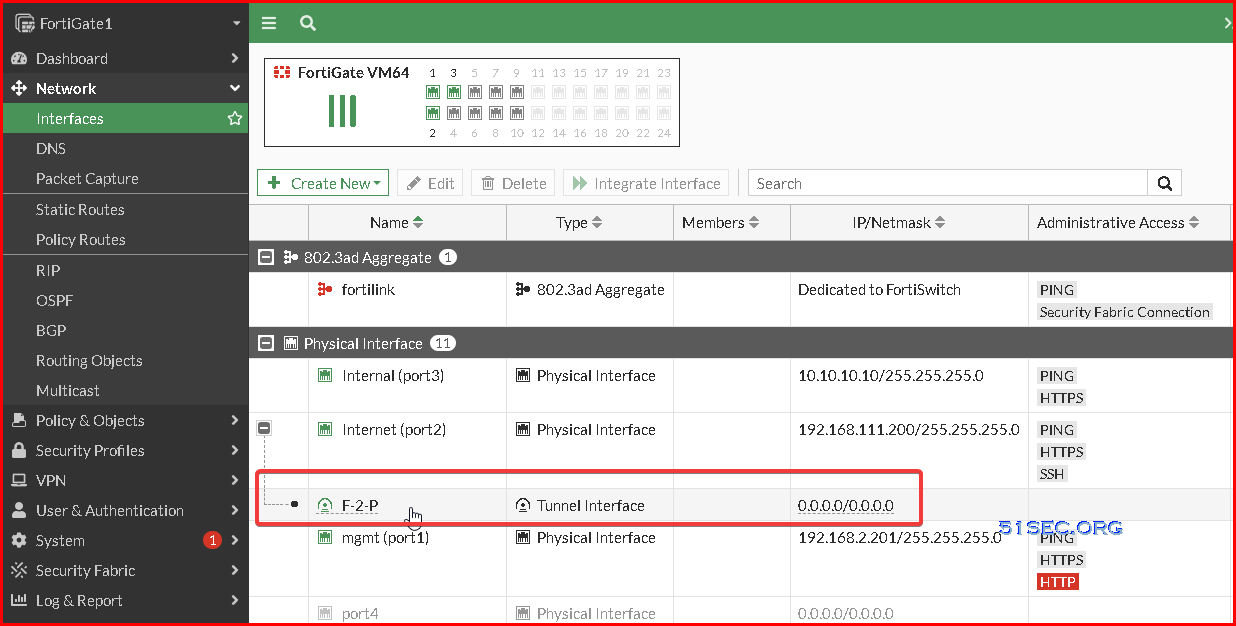
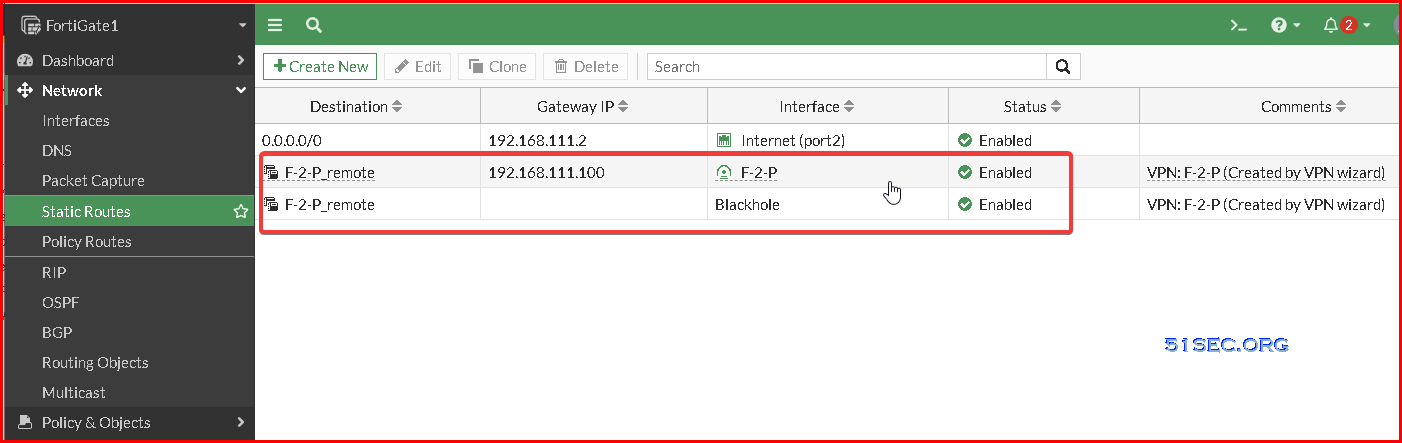
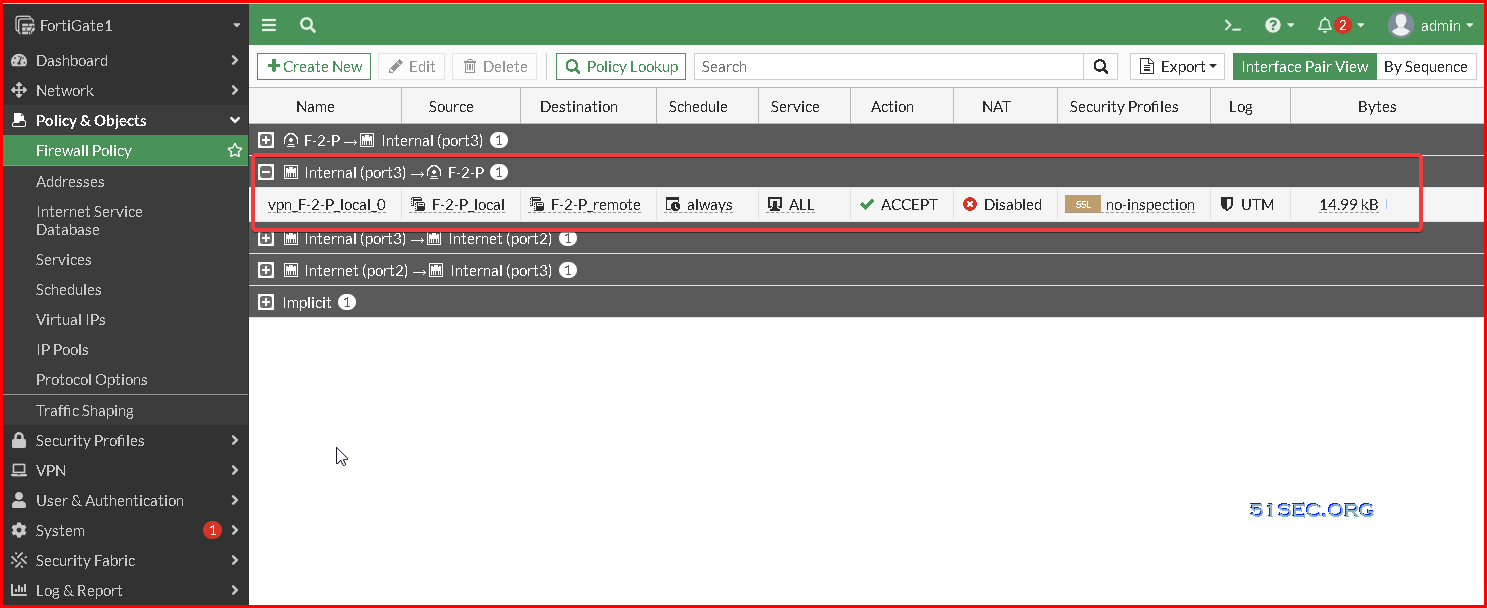
6 Fortigate VPN Wizard will auto-generate tunnel interface, static route to tunnel, and policy rule to allow traffic between vpn networks.
Test
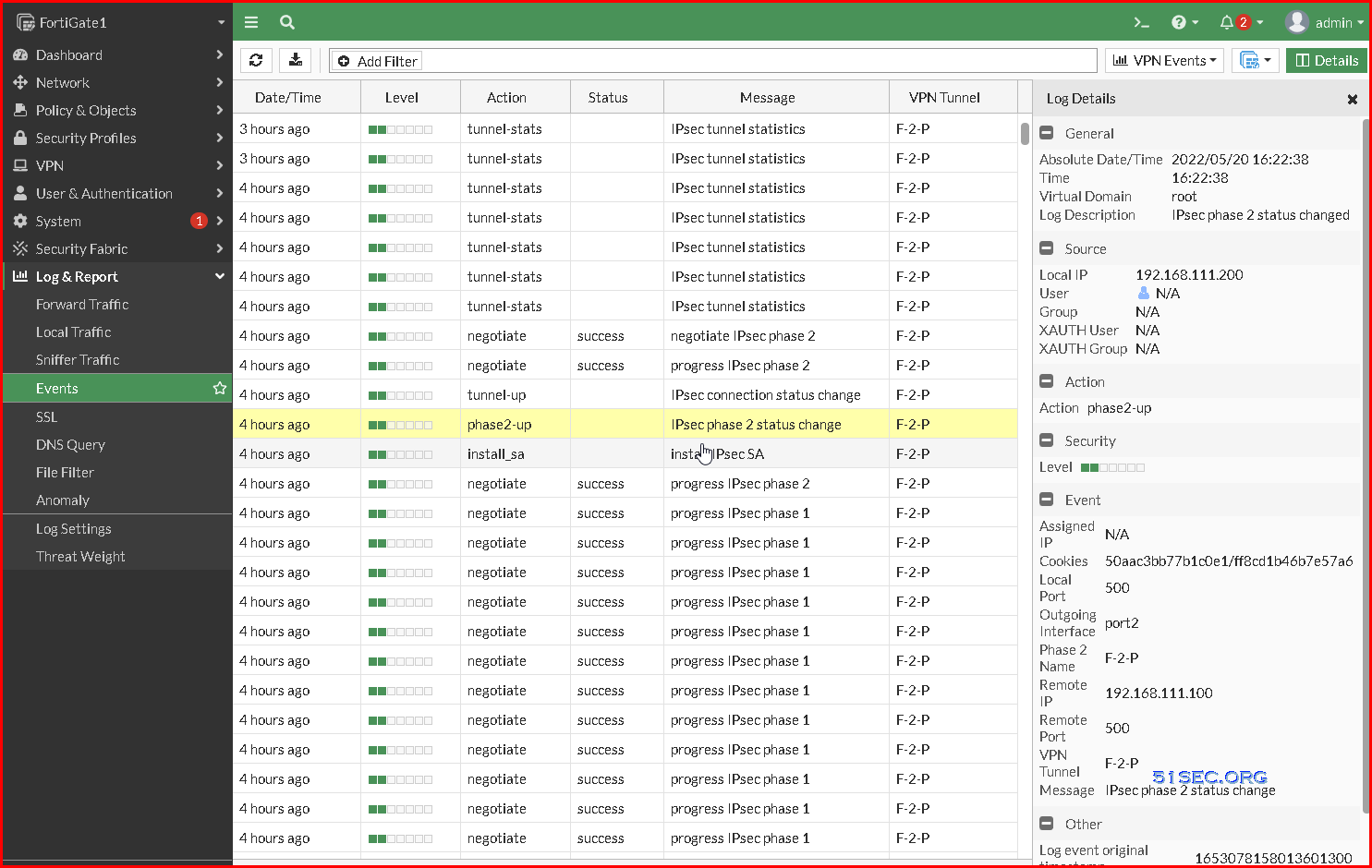
On Fortigate,
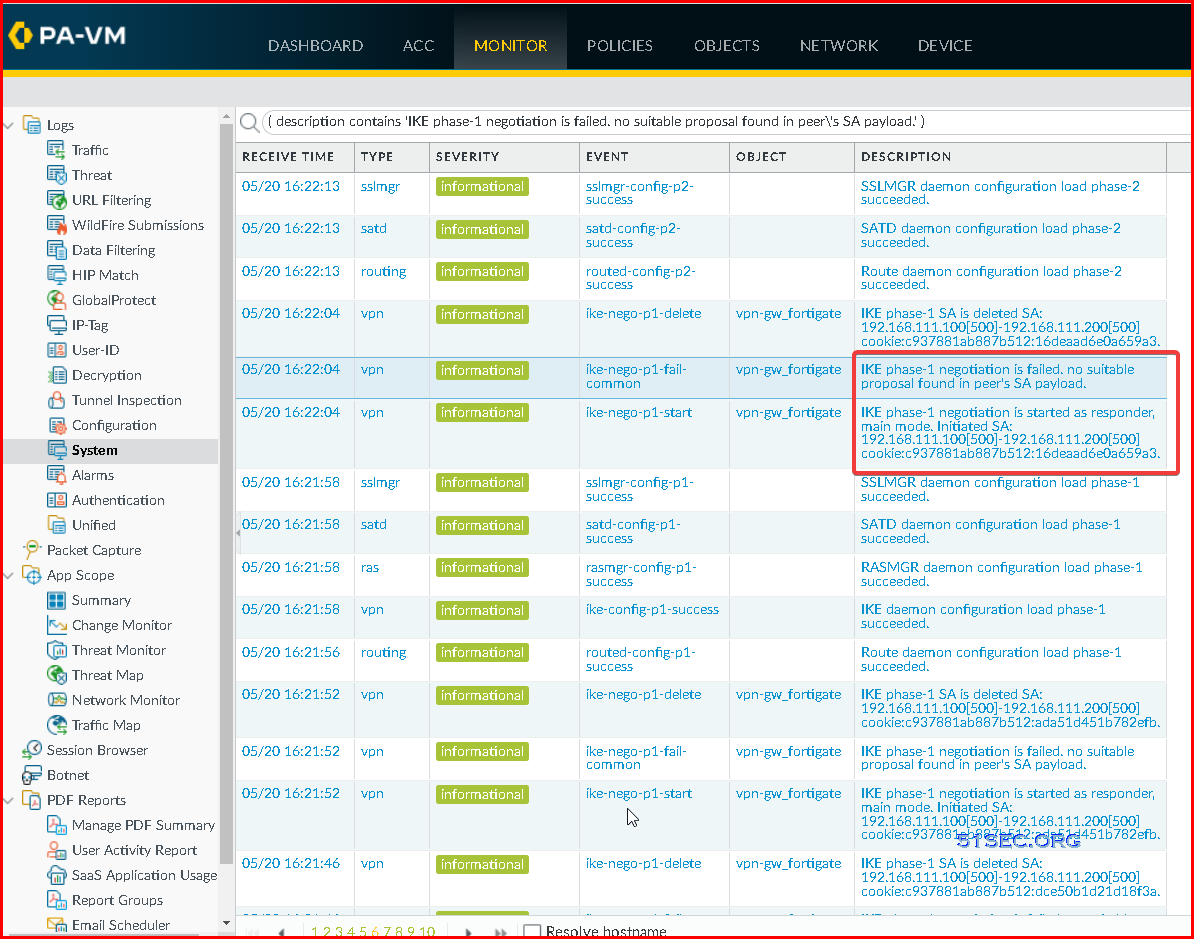
On Palo Alto:
Videos
IPSec VPN Tunnel Setup:








No comments:
Post a Comment