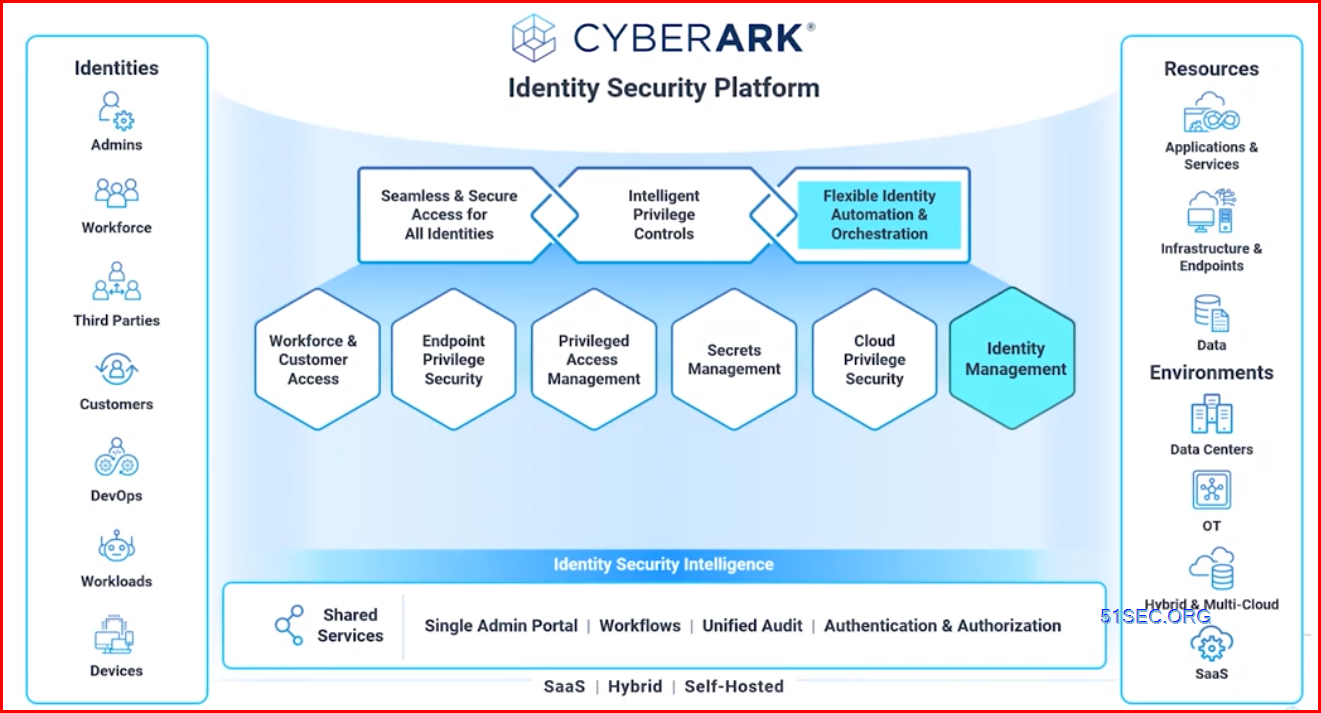
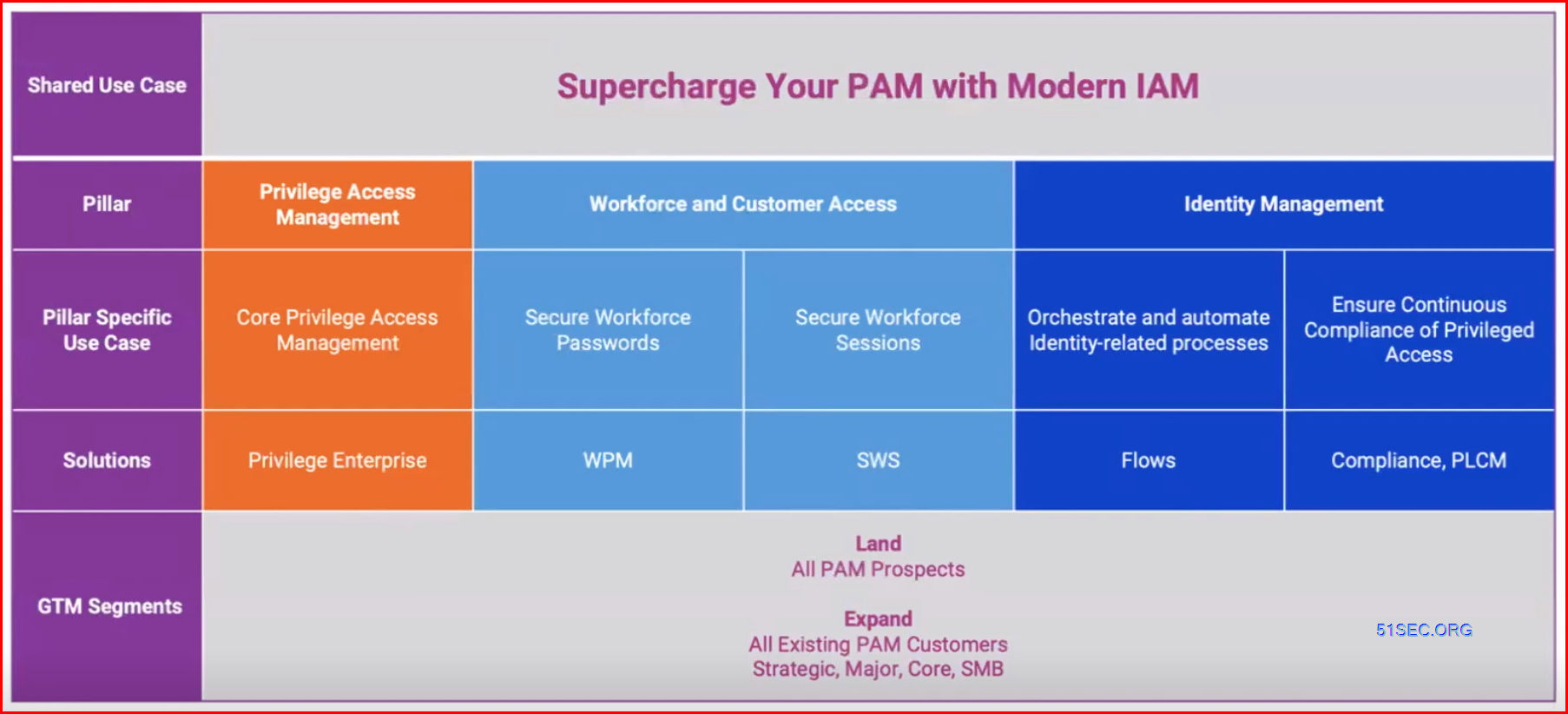
CyberArk's Identity Security approach is built on the security pillars of Access, Privilege, and DevSecOps to deliver authentication, authorization, access, and audit in an integrated, seamless manner — ensuring security at every step in the Identity Security lifecycle. Our intelligent approach balances the need for higher levels of security with making end-users’ access more productive. We do this by using real-time intelligence and analytics to create a context-based, adaptive approach to the Identity Security lifecycle. CyberArk does this for all identities, across all systems and apps, using any device.
IDENTITY MANAGEMENT FOR EVERY ORGANIZATION
Orchestrate and automate the administration and governance of digital identities.
All Identities can be privileged under certain contditions
Features
Zero Trust Security Model:
- Verify Every User CyberArk Identity provides secure access to any user--whether it is the IT Admin, DevOps engineer, Application or any workforce team member
- Validate Every Device CyberArk Identity includes ability to create policies for establishing context from anywhere using any device
- Intelligently Limit Access CyberArk Identity follows RBAC Best Practices when users/devices are accessing any application or system-- from SaaS applications to cloud workloads and on-prem applications and systems
END-TO-END IDENTITY MANAGEMENT :Centrally grant, maintain, and analyze access to right-size permissions on the journey to least privilege.
Automated Access Provisioning: Dynamically provision and revoke access to corporate resources
Identity Orchestration: Simplify and automate complex identity processes
Compliance Controls: Establish organization-wide compliance and access attestation controls
Comprehensive Reporting: Use audit reports and detailed dashboards to gain visibility into access permissions and entitlements
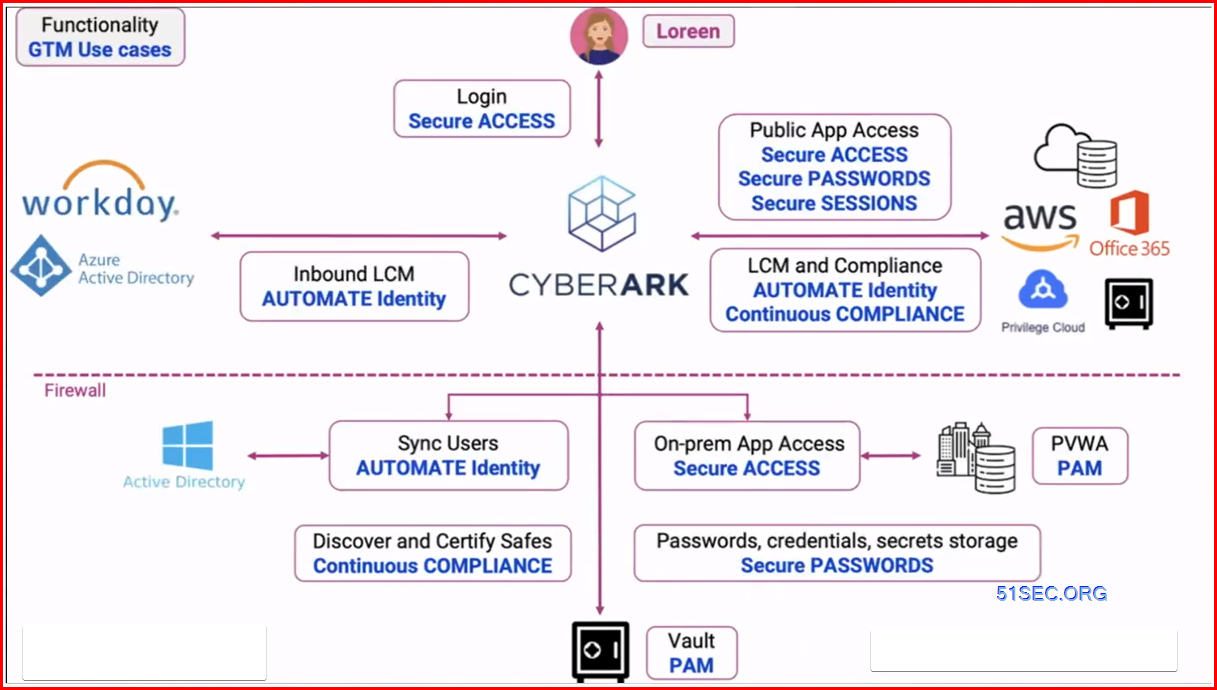
REDUCE RELIANCE ON MANUAL PROCESSES: Automate Identity Lifecycle and Compliance Management for all User Accounts and Privileges.
Lifecycle Management: Streamline identity lifecycle events and automate access for workforce and privileged users joining, moving roles and leaving the organization.
Identity Compliance: Consolidate access rights data, streamline access recertification processes and enforce access compliance across your enterprise.
Identity Flows: Automate identity management tasks through no-code app integrations and workflows for identity data, processes and events.
Directory Services: Manage identities, groups and devices on-premises or in the cloud.
Four Core Capabilities
- MFA and Passwordless authentication
- Secured SSO
- Identity Lifecycle Management
- Directory Services
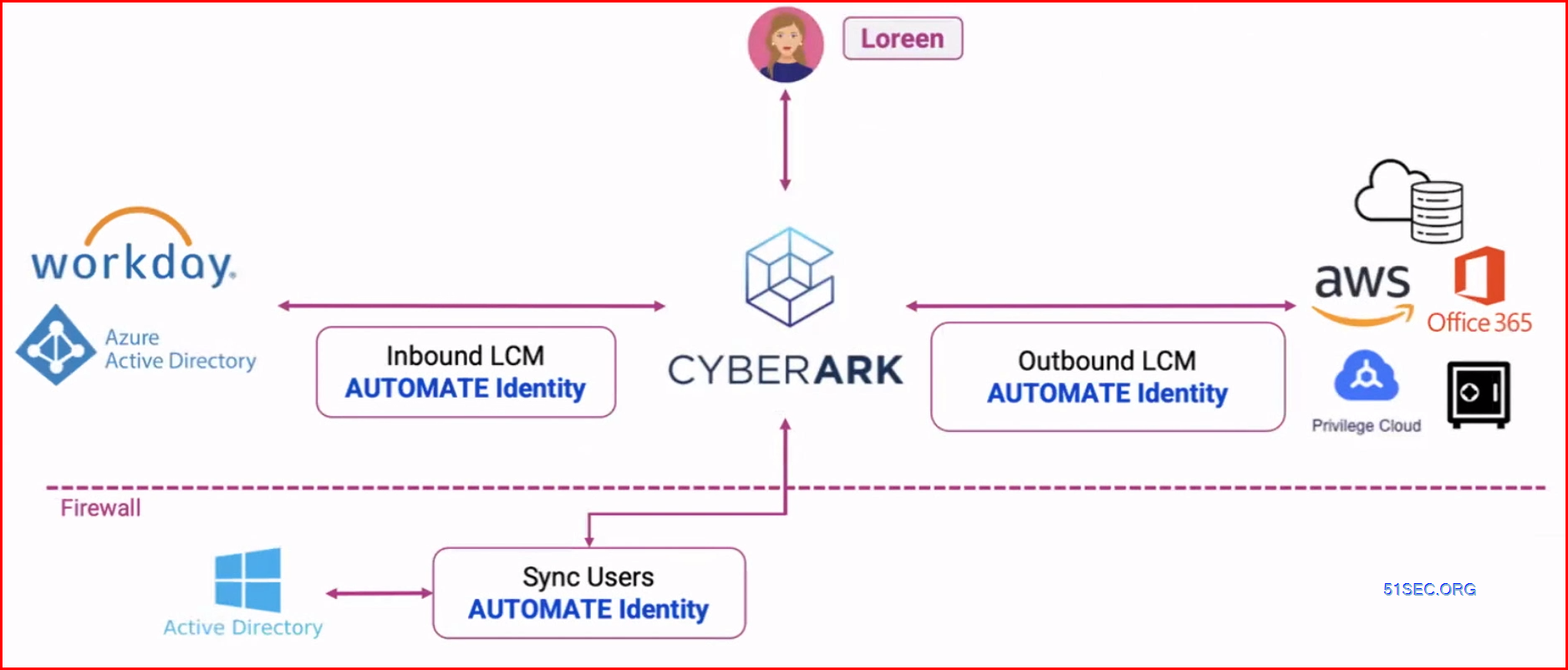
Diagram
LCM = LifeCycle Management
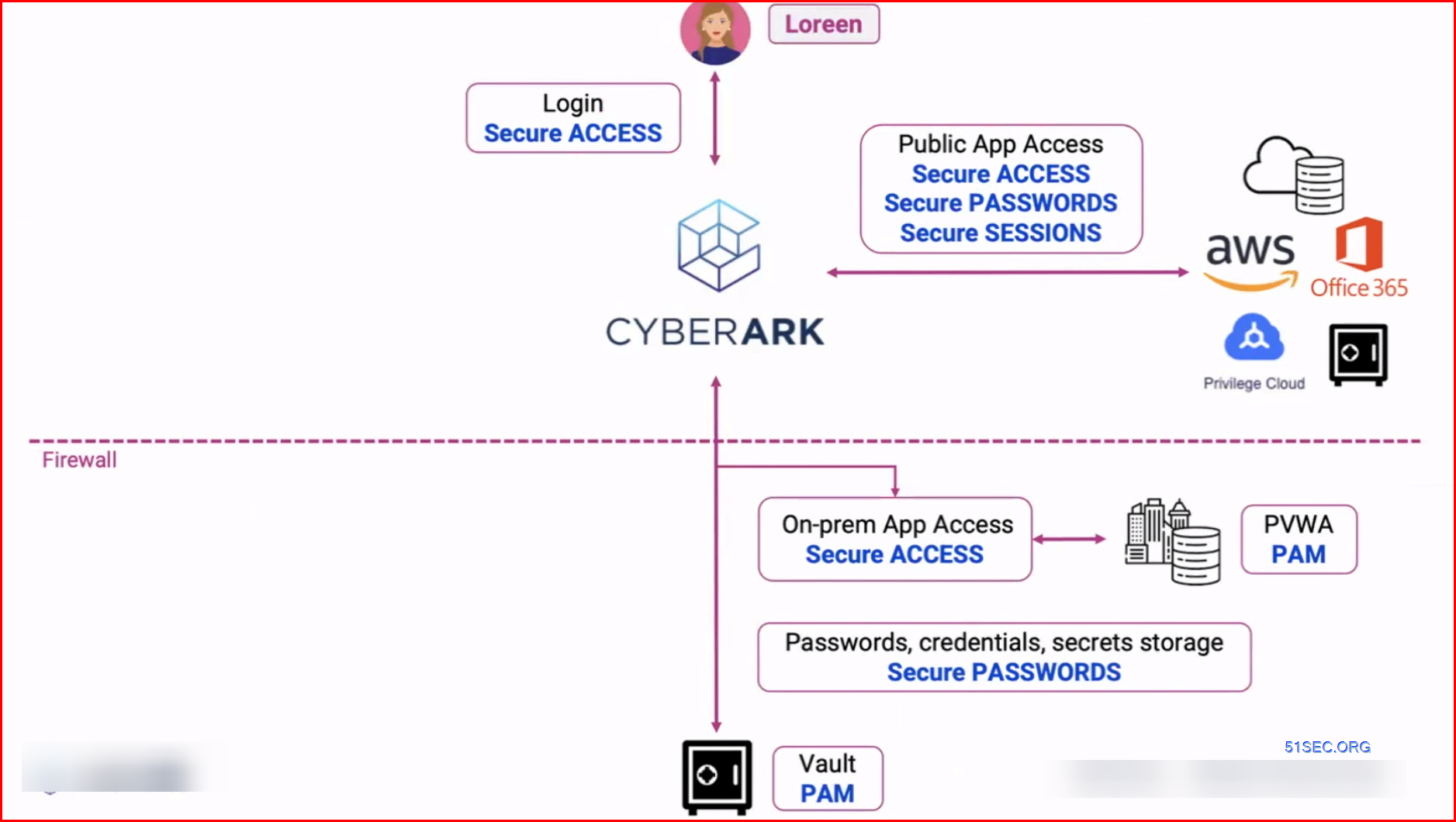
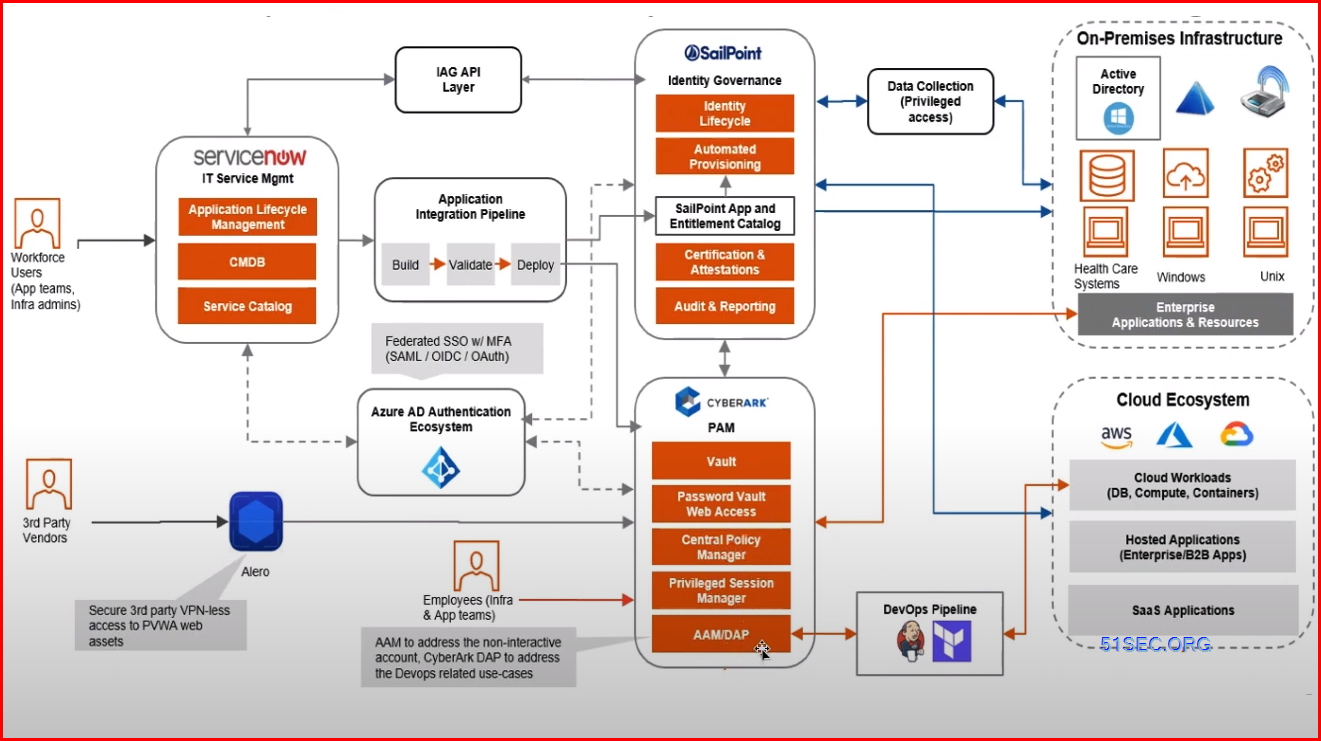
Architecture Examples
One High - Level Architecture
Note:https://www.youtube.com/watch?v=rlxCrnuzva4
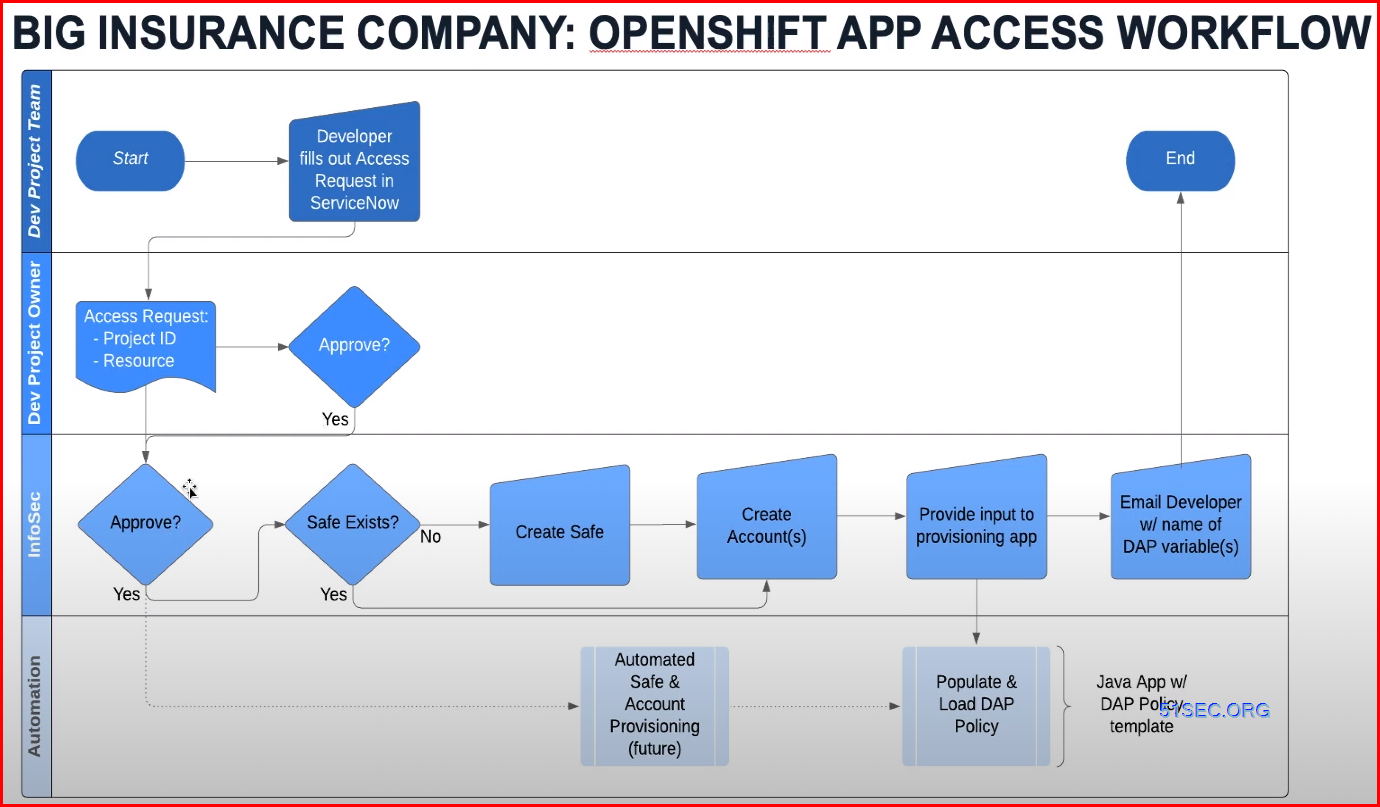
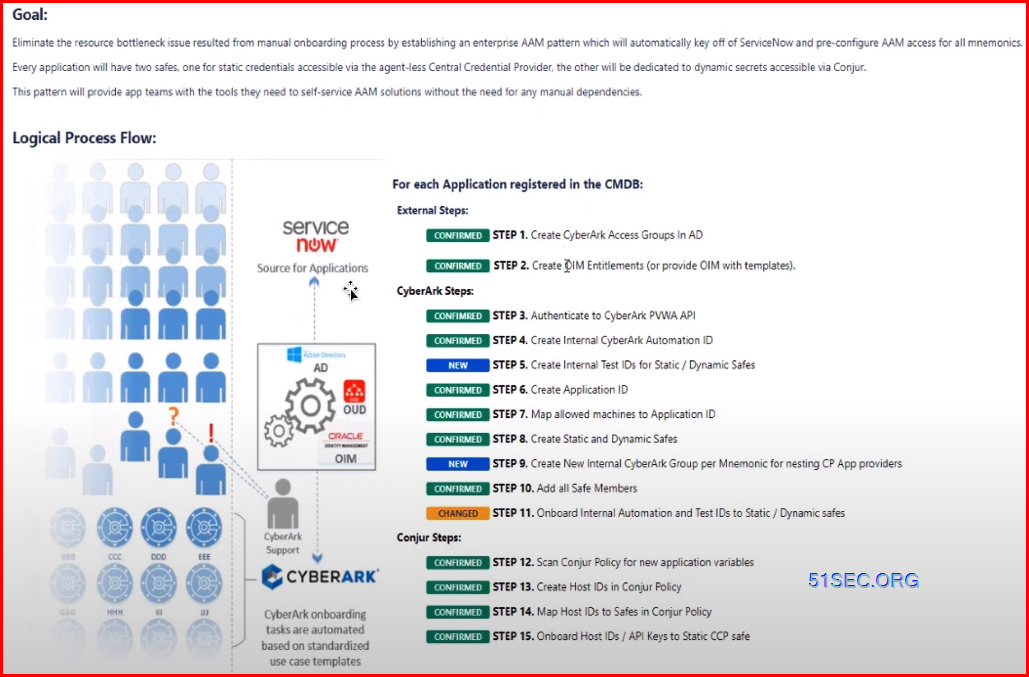
Automated Secret on-boarding flow:
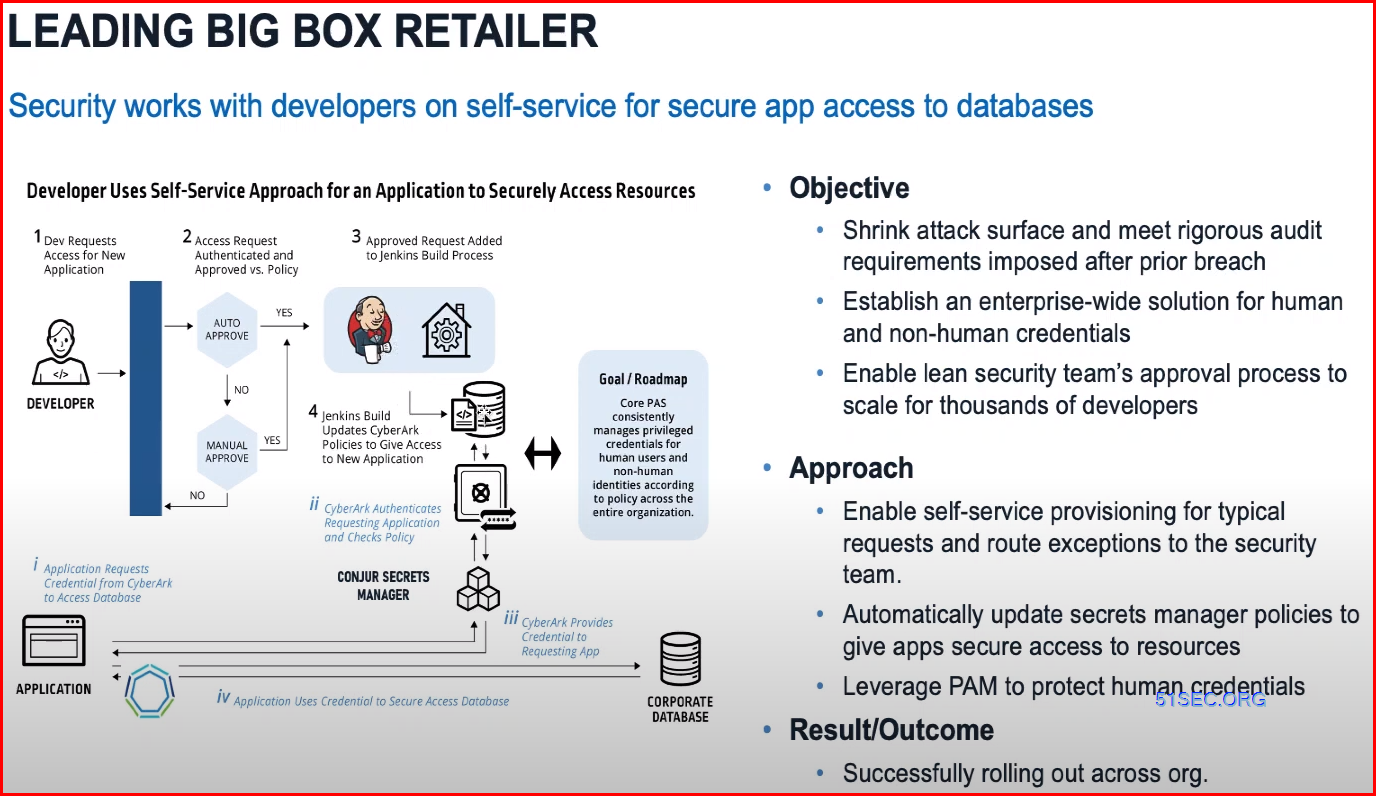
Self-service for secure app access to db
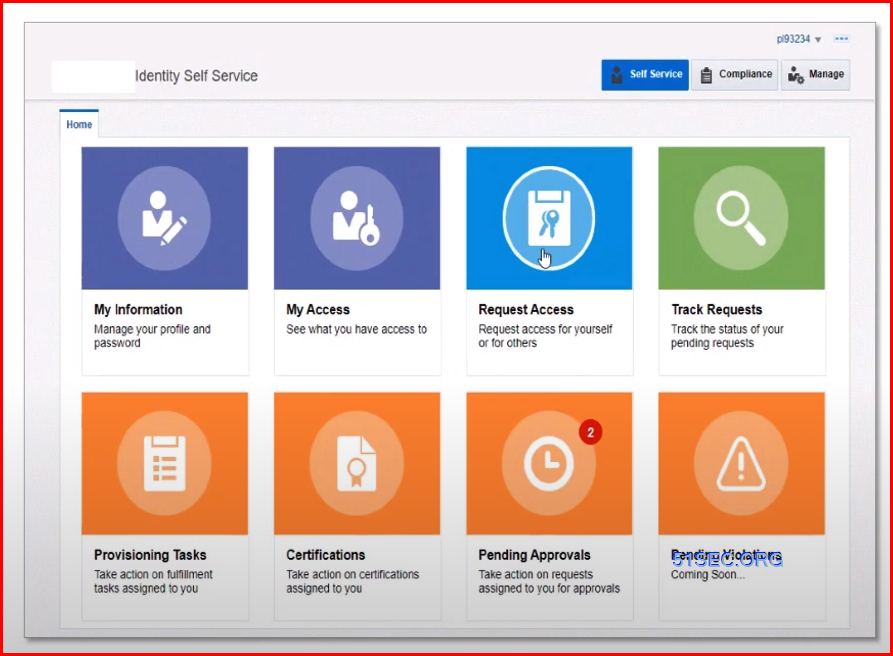
Large Bank: Self Service Portal:
Large Bank: Onboarding tasks
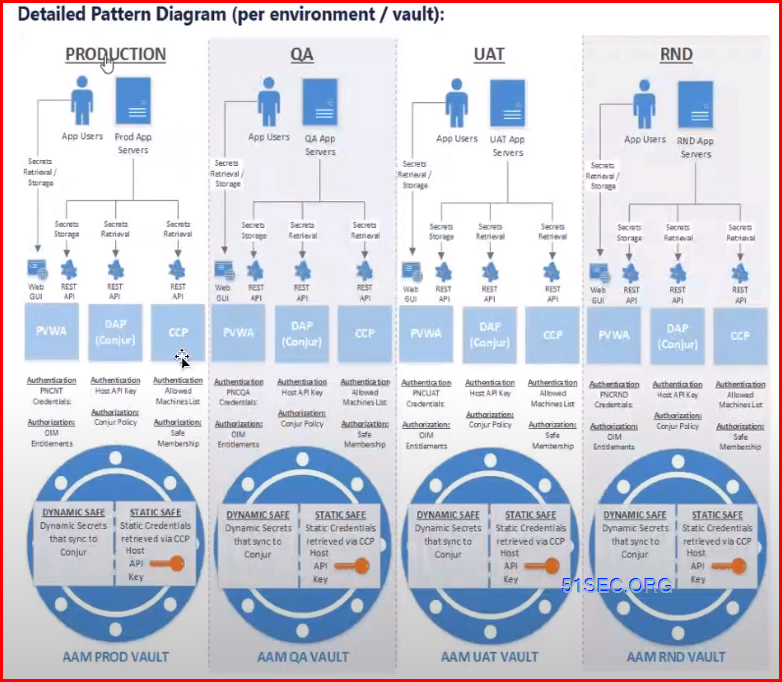
A vault for each environment: (Large bank)
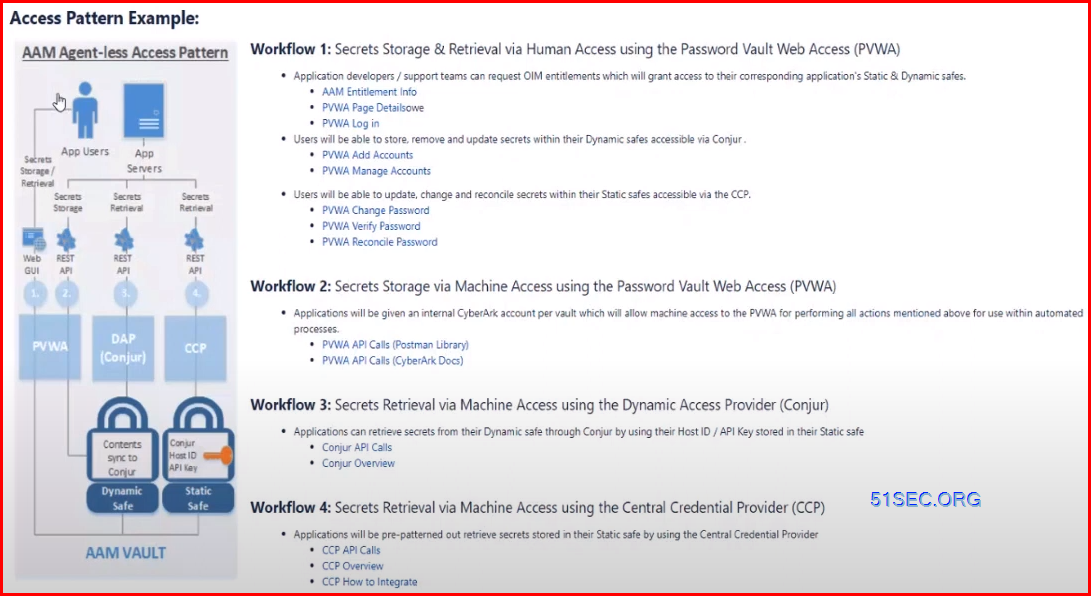
Large Bank : Workflows
References







No comments:
Post a Comment