This post is to summarzie the basic knowledge you can start to use Azure Sentinel as fast as possible.
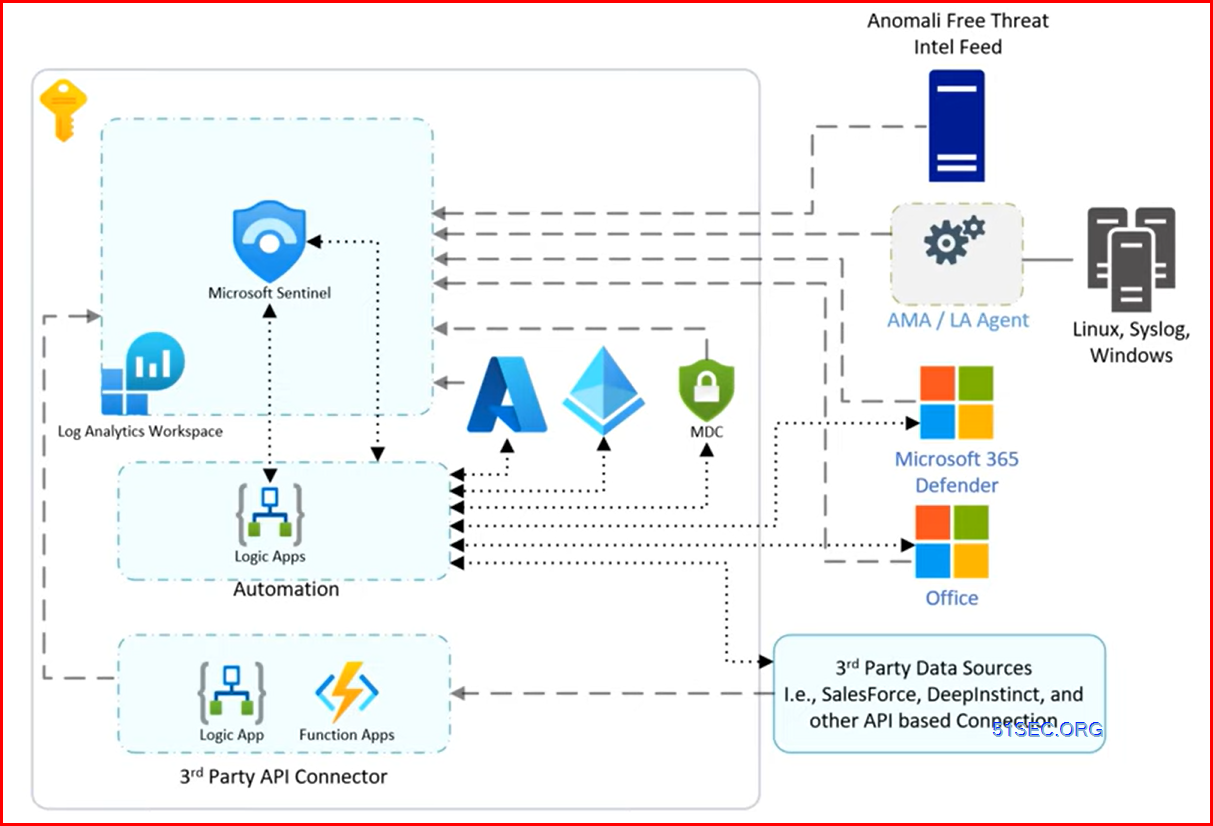
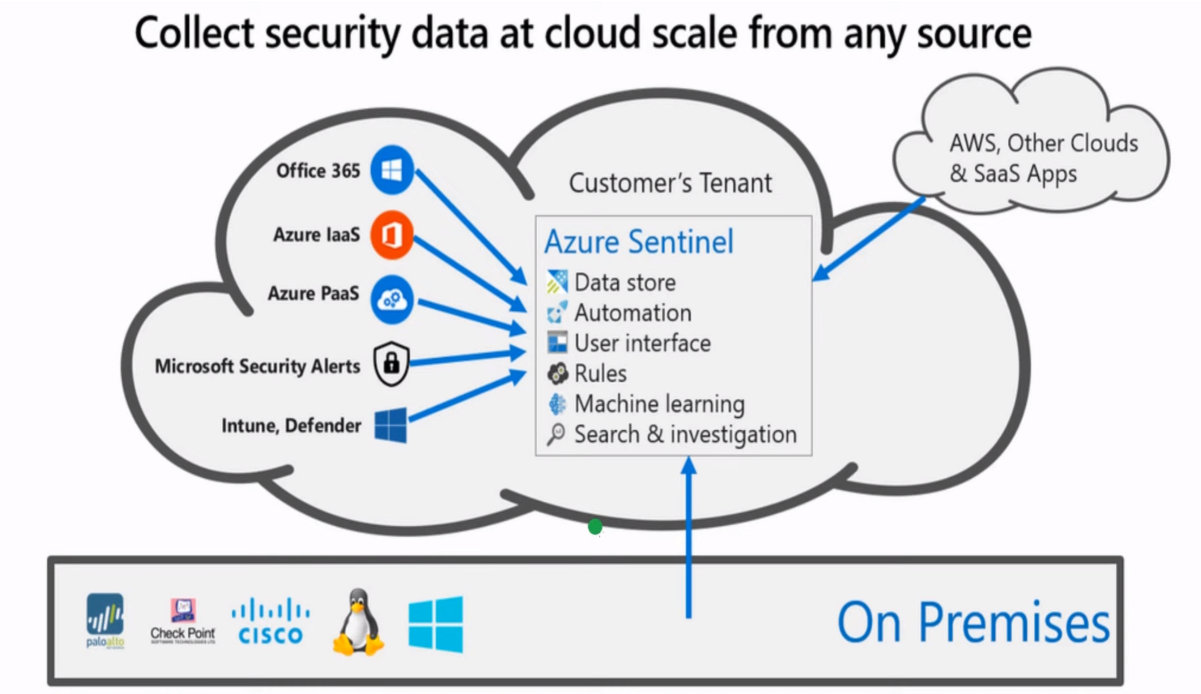
Architecture
Sentinel Workspace, Price and Roles
- https://blog.51sec.org/2023/10/azure-sentinel-101.html
- https://azure.microsoft.com/en-ca/pricing/details/microsoft-sentinel/
| Tier | Microsoft Sentinel Price | Effective Per GB Price1 | Savings Over Pay-As-You-Go |
|---|---|---|---|
| Pay-As-You-Go | $6.95 per GB-ingested | $6.95 per GB-ingested | N/A |
| 100 GB per day | $456.74 per day | $4.57 per GB | 34% |
Microsoft Sentinel Reader can view data, incidents, workbooks, and other Microsoft Sentinel resources.
Microsoft Sentinel Responder can, in addition to the above, manage incidents (assign, dismiss, etc.).
Microsoft Sentinel Contributor can, in addition to the above, install and update solutions from content hub, create and edit workbooks, analytics rules, and other Microsoft Sentinel resources.
Microsoft Sentinel Playbook Operator can list, view, and manually run playbooks.
Microsoft Sentinel Automation Contributor allows Microsoft Sentinel to add playbooks to automation rules. It isn't meant for user accounts.
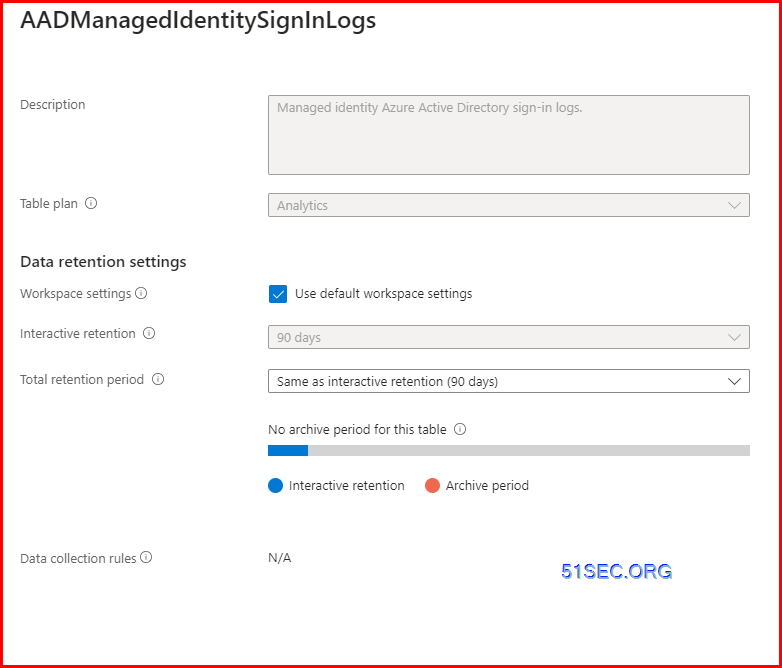
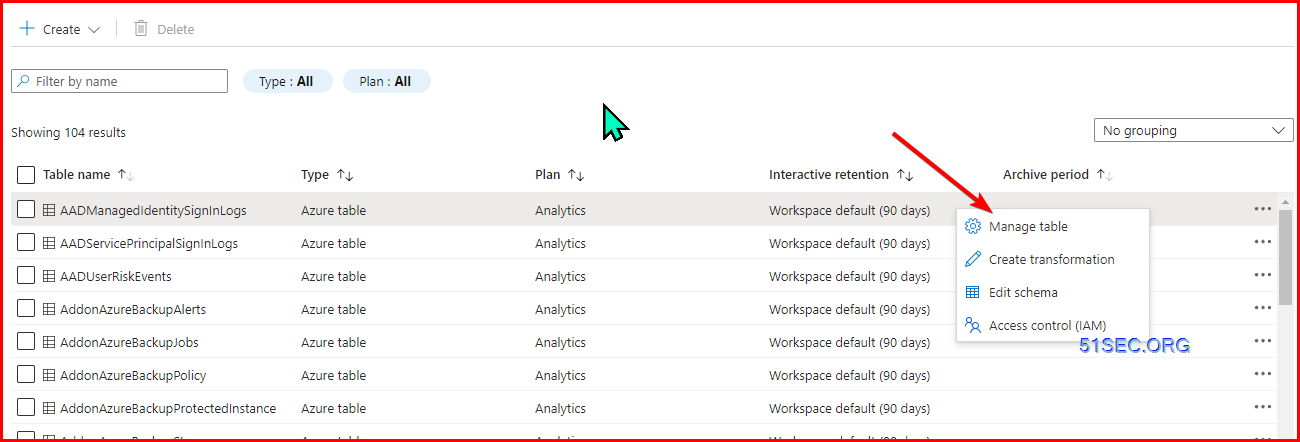
Log Retention
Diagram
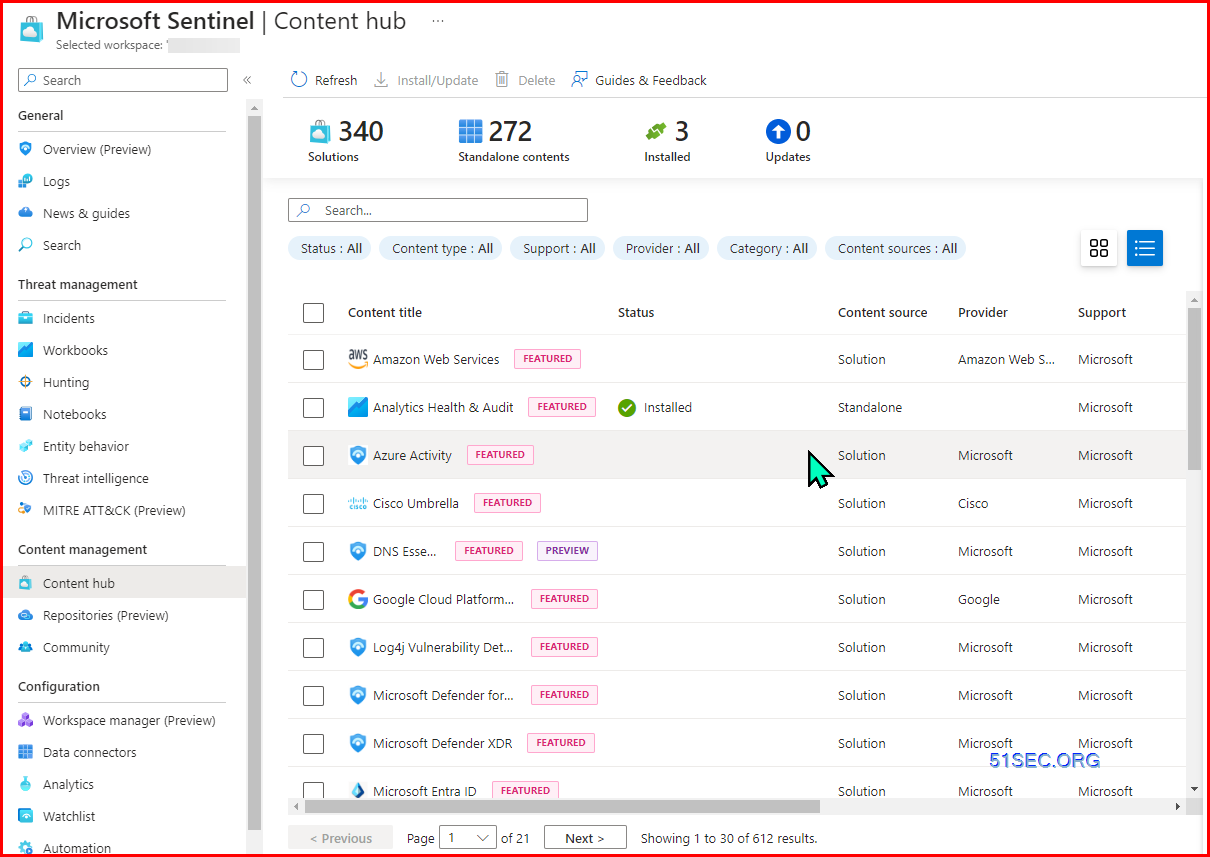
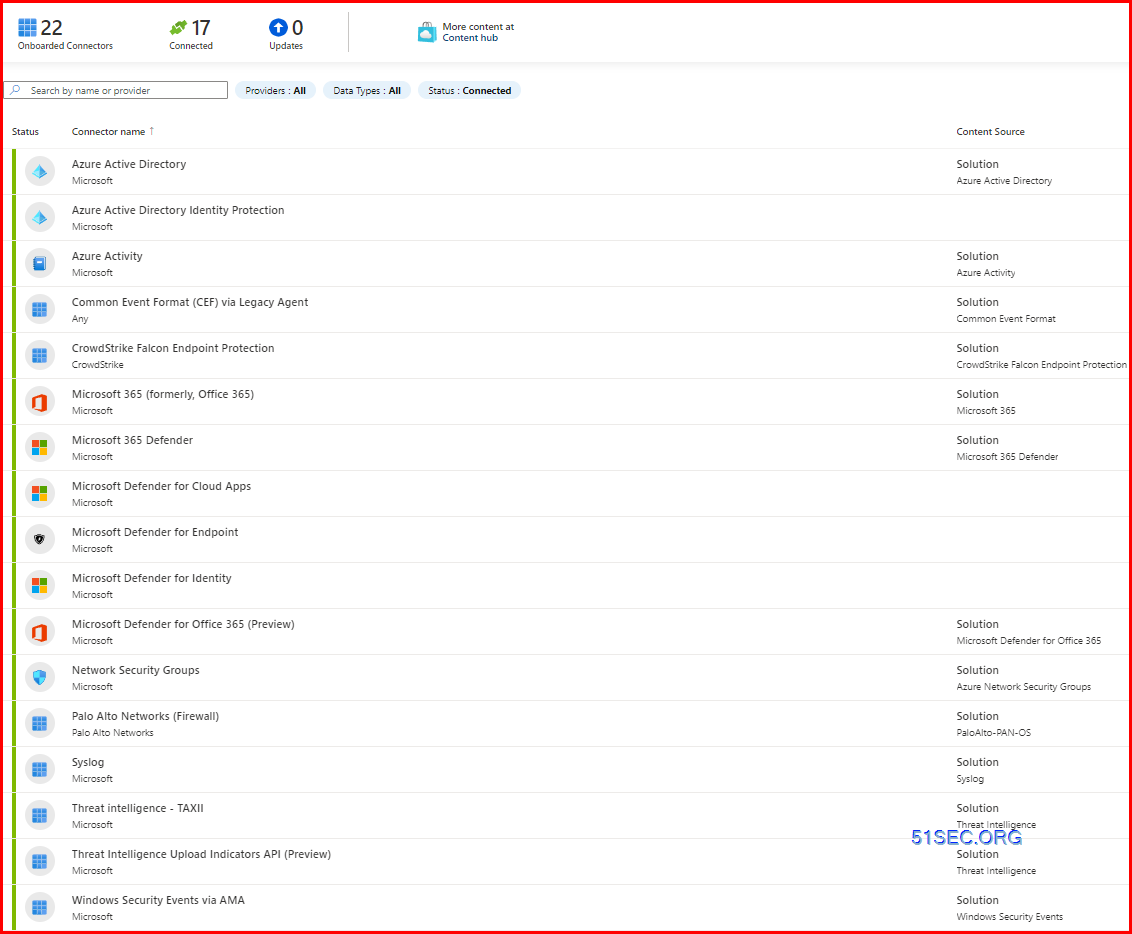
Content Hub & Data Connectors
- Azure Activity
- Network Session Essential
- Azure Active Directory
- Common Event Format
- WIndows Security Events
Microsoft Sysmon For Linux
Common Event Format (CEF) via AMA (Azure Monitor Agent)
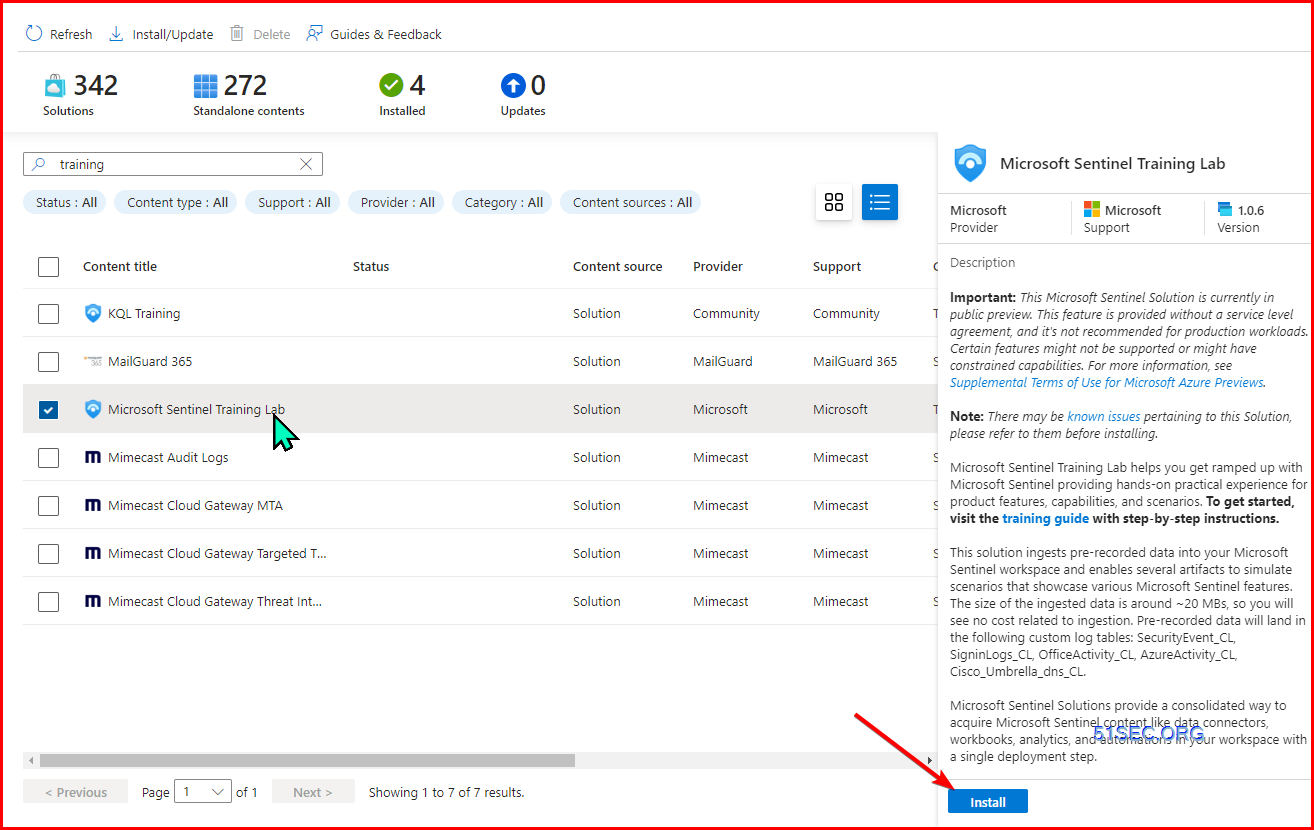
Microsoft Sentinel Training Lab Solution
This solution ingests pre-recorded data into your Microsoft Sentinel workspace and enables several artifacts to simulate scenarios that showcase various Microsoft Sentinel features. The size of the ingested data is around ~20 MBs, so you will see no cost related to ingestion. Pre-recorded data will land in the following custom log tables: SecurityEvent_CL, SigninLogs_CL, OfficeActivity_CL, AzureActivity_CL, Cisco_Umbrella_dns_CL.
Training guide: https://github.com/Azure/Azure-Sentinel/tree/master/Solutions/Training/Azure-Sentinel-Training-Lab
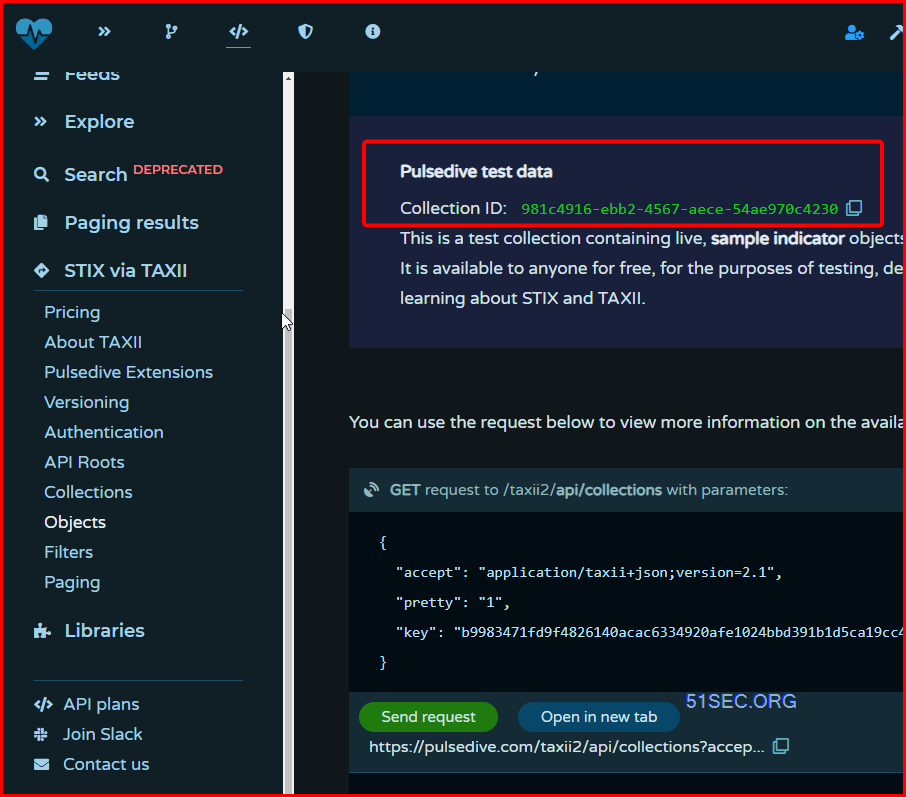
Threat Intelligence
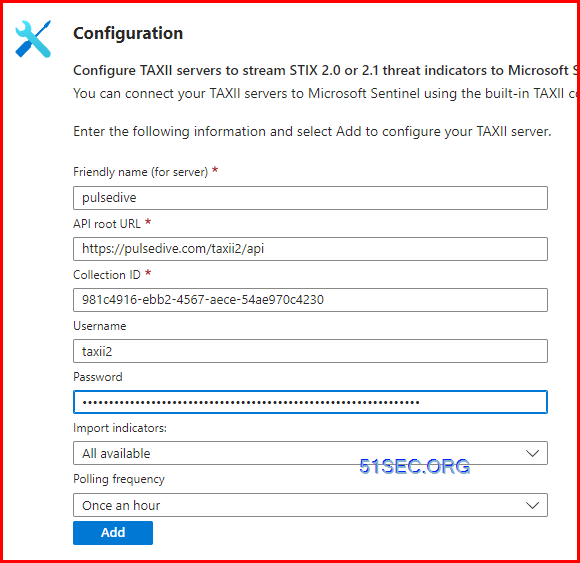
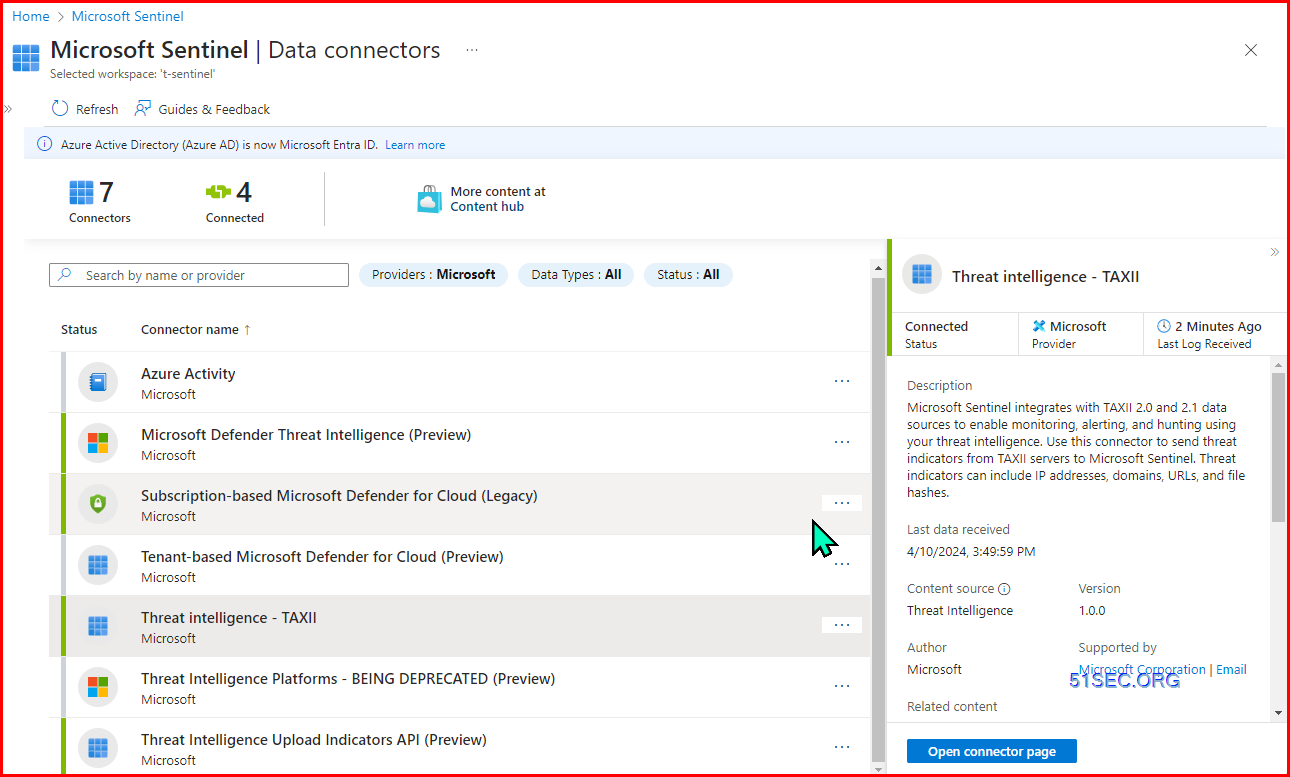
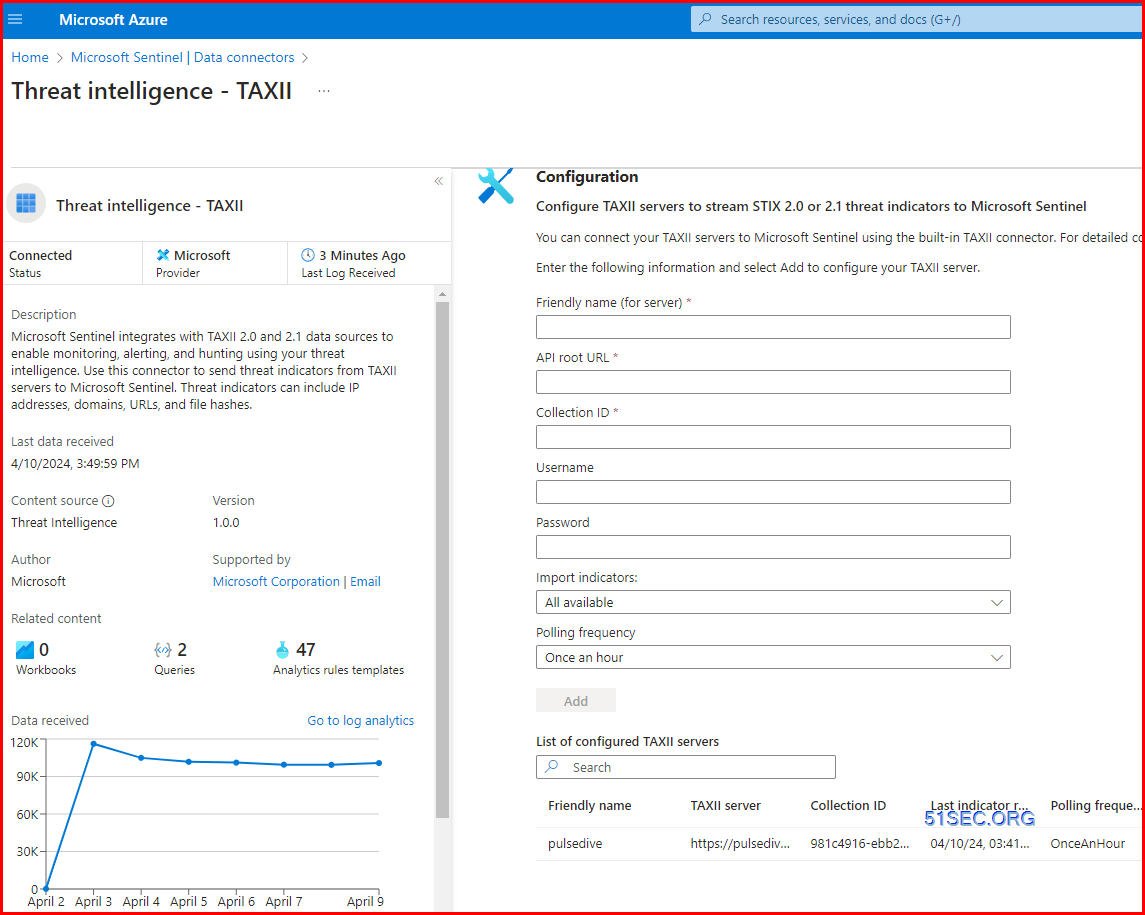
Install Threat Intelligence from Content HubOpen Connector Page from Connector - Threat Intelligence - TAXII
Get free threat intelligence service from https://pulsedive.com/
api root:https://pulsedive.com/taxii2/api
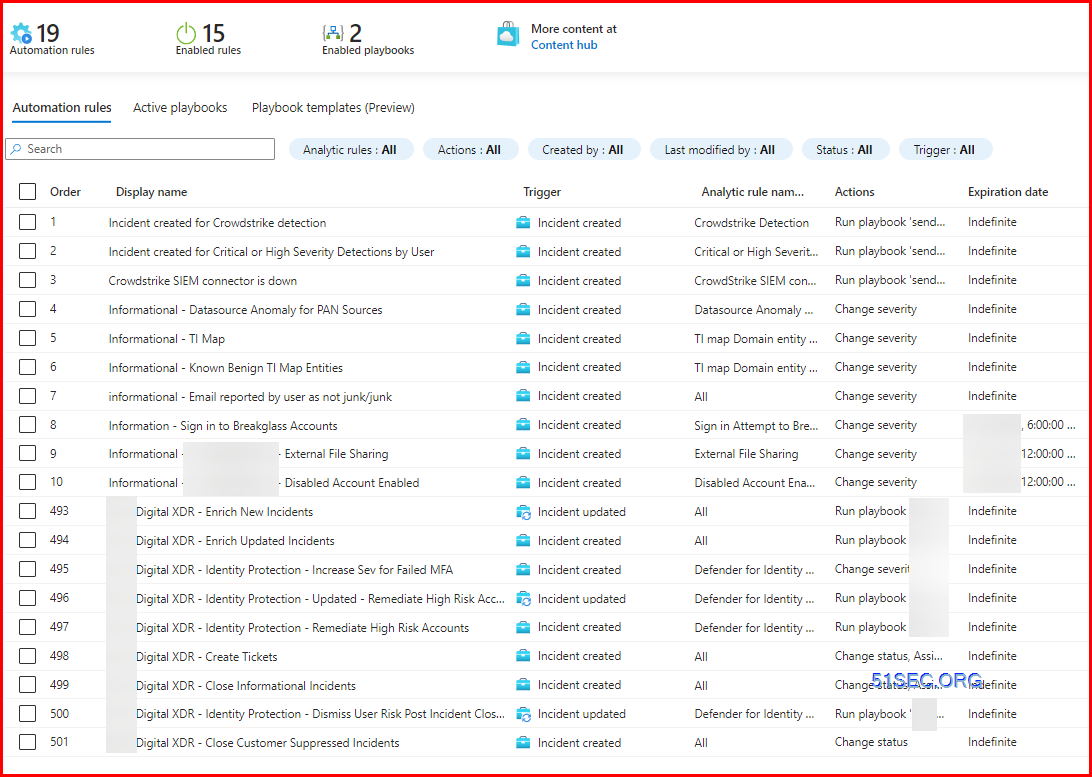
Automation
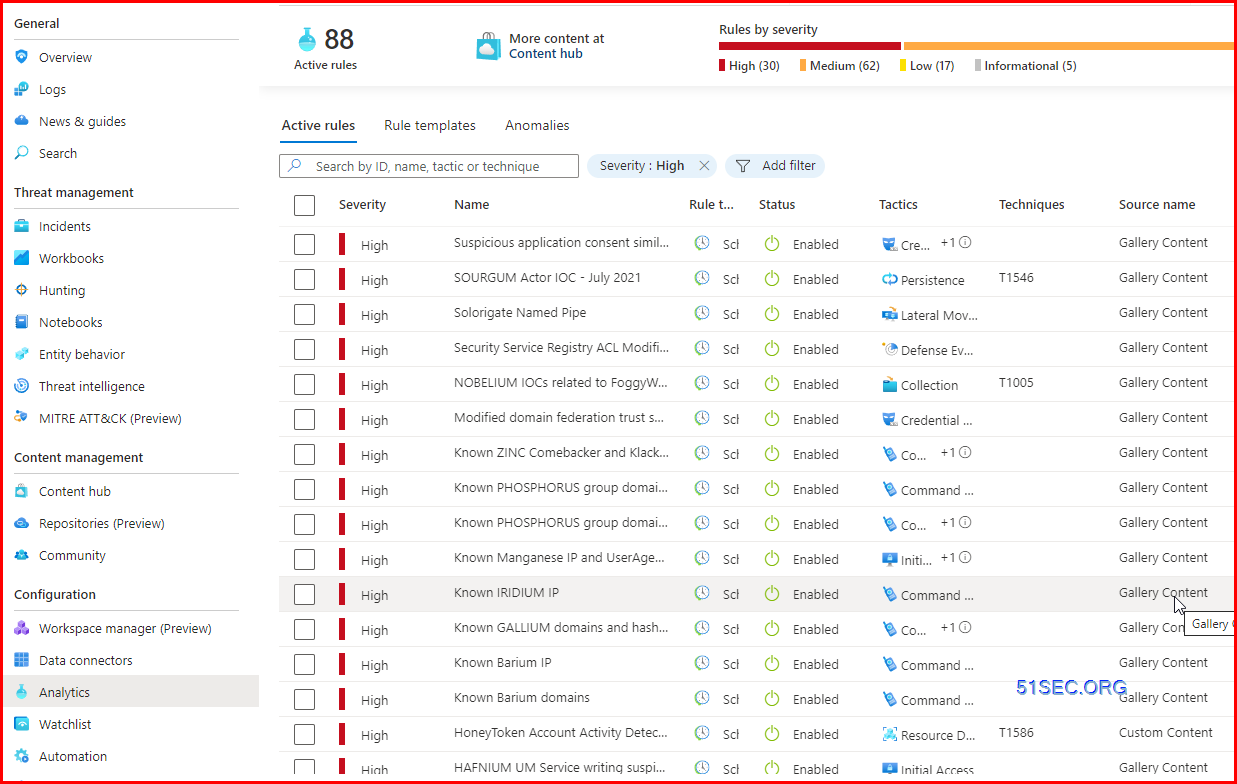
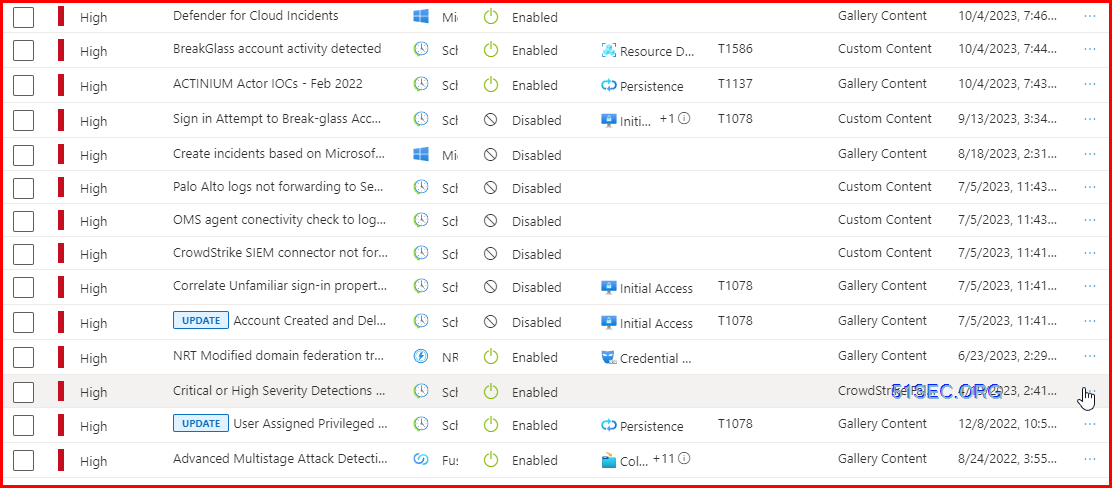
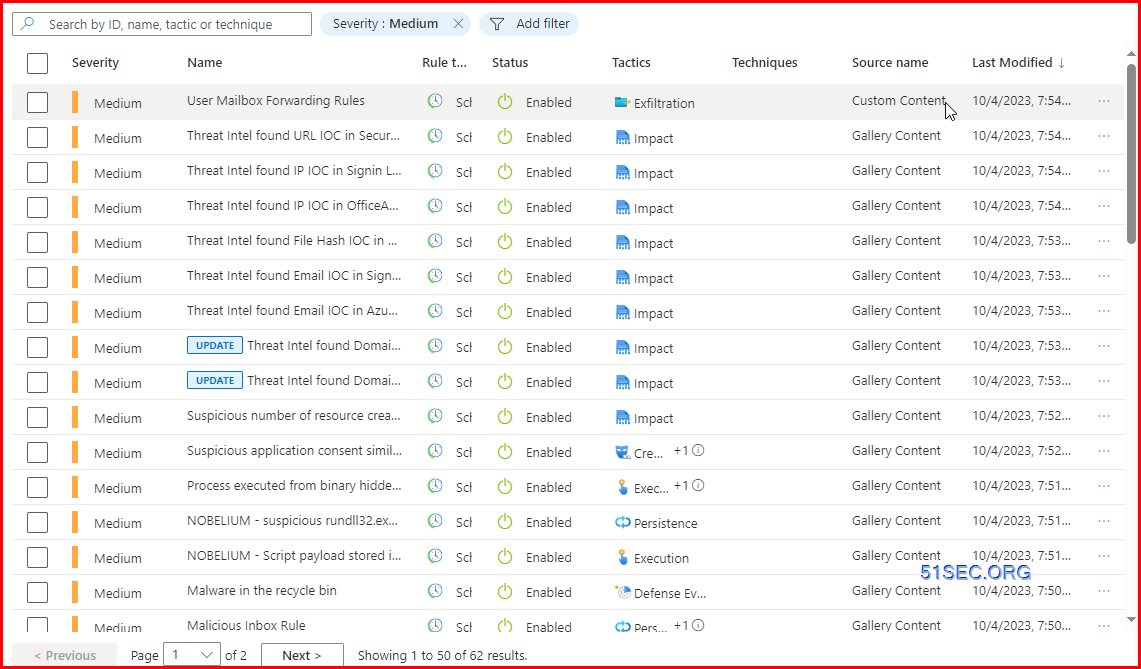
Analytics Rules
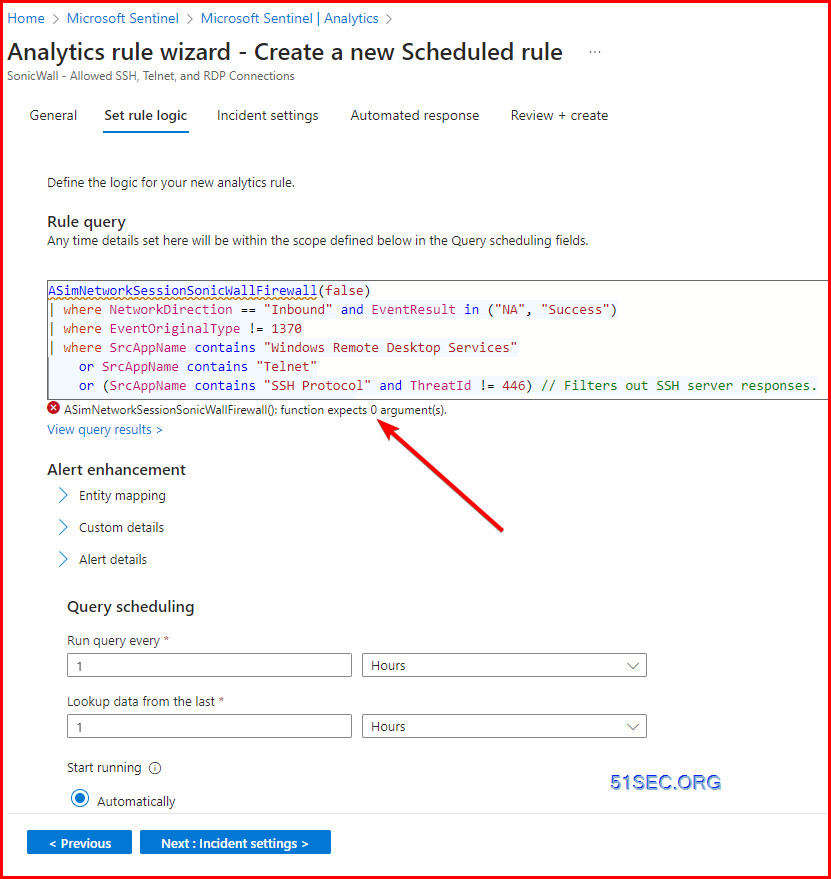
Issuse for Built-in Rule - SonicWall - Allowed SSH, Telnet, and RDP Connections
It shows "ASimNetworkSessionSonicWallFirewall(): function expects 0 argument(s)."ASimNetworkSessionSonicWallFirewall()The error should go away after removed false argement.
KQL - Kusto Query Language
You can practice Kusto Query Language statements - including the ones in this article - in a Log Analytics demo environment in the Azure portal. There is no charge to use this practice environment, but you do need an Azure account to access it.








No comments:
Post a Comment