Qualys Community Edition is a free version of the Qualys Cloud Platform designed for the security community.
- Discover IT assets.
- Manage vulnerabilities.
- Scan web apps.
- Inventory cloud assets.
Qualys Community Edition Getting Started Guide: https://www.qualys.com/docs/qualys-community-edition-user-guide.pdf
Related Posts:
- Register Free Qualys Community Edition For Your Own Cloud Vulnerability Scan
- Register Free Nessus Scanner Essentials and Execute a Vulnerability Scan
- OpenVAS Virtual Appliance / GreenBone Installation
- Install OpenVAS on Ubuntu
- Metasploit Installation on Windows 7 and 10
- AWVS (Acunetix Web Vulnerability Scanner) Docker Installation
Features
Qualys Community
Edition gives you these great capabilities at no cost:
- Monitor up to 16 assets with
Qualys Cloud Agent
- Scan up to 16 internal and 3
external IPs with Vulnerability Management
- Scan 1 URL with Web Application
Scanning.
- Deploy a Virtual Scanner Appliance
within your internal network.
- Gain visibility within your
cloud environments.
- Generate reports and assess results quickly and easily.
To summarize the limitations:
Only the scanning of 16 IP addresses (internal or public) is allowed, and only 1 Web application Scanner is available. Furthermore, only one local appliance can be deployed, so only one internal network can be scanned.Similar product: Tsunami Security Scanner
Tsunami is a general purpose network security scanner with an extensible plugin system for detecting high severity vulnerabilities with high confidence.
URLs:
- https://github.com/google/tsunami-security-scanner
- https://github.com/google/tsunami-security-scanner/blob/master/docs/index.md
- https://github.com/google/tsunami-security-scanner-plugins
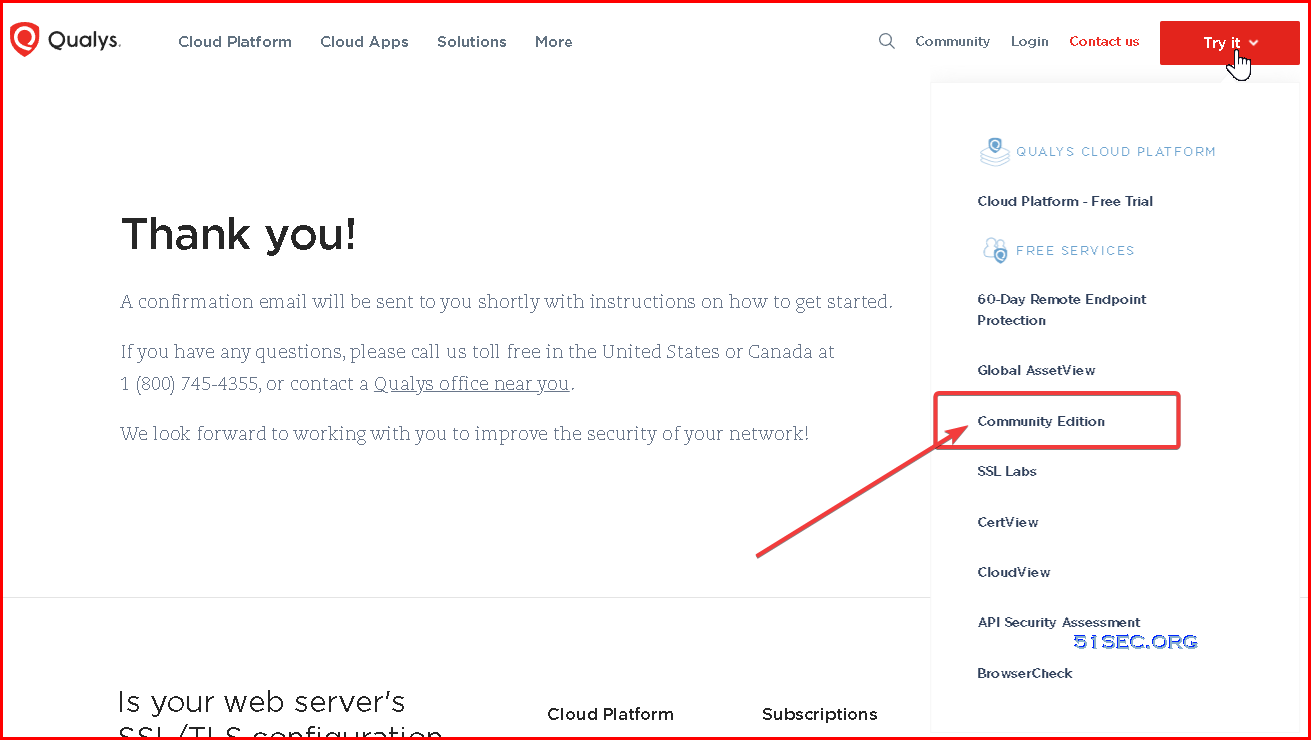
Registration
Registration can be done here
1. Registration
Quick Start
To scan your internal network you will need to download the virtual appliance, and register it with the Qualys Platform.
Use the Discovery scan to get a list of assets (hosts) present on you local network, and check the open ports.
Operations
Vulnerability Scan
This is where it gets interesting. Select up to 16 internal or external IP addresses to be scanned. This is the basis for either an on-demand scan, or future scheduled scans. There are many options to choose from, but often the defaults are fine. To scan the internal network, select the virtual appliance you downloaded earlier. I also recommend performing some external scans using the external (Qualys) scanner, targeting your external IP address, to see what is vulnerable from the outside. The internal scan took about 35 minutes on my network, but it probably depends on the number of open ports.Web Application scanning
Qualys Community Edition package also includes Web Application scanning, although the CE is limited to one web application only. There are many settings to tweak the scan to your needs. Even complicated Selenium scripts can be included in the scans. It is unfortunate that contrary to the vulnerability scans, the Web Application Scans cannot be scheduled.Cloud agents
A different way to scan the infrastructure is the use of cloud agents. These are small programs that are installed on the computers of the network. Agents can be downloaded for Linux, Windows, IBM AIX, and OSX. From the inside of the computer, they can detect things that cannot be detected easily from the outside. The agents can for instance detect software that needs updating.Results
By default, both the vulnerability scan and web application scans may give a lot vulnerabilities. And this is where things get more complicated. What are false positives, what can be ignored, and what should be rectified immediately? Of course, all vulnerabilities are ranked by threat level, and Qualys does an excellent job at giving additional information about the vulnerabilities found. One the other hand, the discovery scan only sees devices which respond to ICMP (ping) messages, so rogue devices can still be hiding in your network without being detected. The cloud agents work really well, the day after Adobe reported a vulnerability I could see which of my system contained the problem. Scanning from the outside proved useful, and pointed out that some application used uPnP to unintentionally forward a port on my router.A Step-by-Step Guide to Securing Your System
Mastering the Art of Vulnerability Scanning: A Step-by-Step Guide to Securing Your System
1. The Importance of Vulnerability Scanning.
As IT professionals, we understand the importance of keeping our networks secure.
However, with the ever-evolving threat landscape, it can be challenging to stay ahead of potential vulnerabilities.
This is where vulnerability scanning comes in.
Vulnerability scanning is a critical component of any comprehensive security strategy.
It allows us to identify weaknesses in our network before they can be exploited by malicious actors.
By conducting regular vulnerability scans, we can proactively address potential threats and prevent costly data breaches.
But vulnerability scanning isnt just about preventing external attacks.
It also helps us identify internal vulnerabilities that could lead to accidental data leaks or other security incidents.
By identifying these vulnerabilities, we can take steps to mitigate them and ensure that our network remains secure from all angles.
In short, vulnerability scanning is an essential tool for any IT professional looking to keep their network secure.
By understanding the importance of vulnerability scanning and implementing it as part of our overall security strategy, we can protect our organizations sensitive data and maintain the trust of our customers and stakeholders.
2. Understanding the Vulnerability Scanning Process.
Understanding the Vulnerability Scanning Process is critical to successfully securing your network.
Vulnerability scanning is a process of identifying and assessing security vulnerabilities in your network, systems, and applications.
It involves using automated tools to scan your network for potential weaknesses that could be exploited by attackers.
The vulnerability scanning process typically involves three stages: discovery, mapping, and analysis.
During the discovery phase, the scanner identifies all devices on the network, including servers, workstations, routers, switches, and other network devices.
In the mapping phase, the scanner maps out the network topology and identifies the relationships between devices.
Finally, during the analysis phase, the scanner performs a detailed analysis of each device to identify any vulnerabilities that may exist.
Its important to note that vulnerability scanning is not a one-time event but rather an ongoing process.
New vulnerabilities are discovered every day, and its essential to stay up-to-date with the latest threats and vulnerabilities.
Regular vulnerability scanning can help you identify and address vulnerabilities before they can be exploited by attackers.
In summary, understanding the vulnerability scanning process is crucial to securing your network.
By regularly scanning your network for vulnerabilities, you can identify and address potential weaknesses before they can be exploited by attackers.
3. Choosing the Right Vulnerability Scanner.
When it comes to choosing the right vulnerability scanner for your network, there are a few key factors to consider.
First and foremost, youll want to ensure that the scanner is capable of detecting all types of vulnerabilities, including those that may be specific to your organizations unique infrastructure and applications.
Additionally, youll want to look for a scanner that provides detailed reporting and analysis capabilities, allowing you to easily identify and prioritize vulnerabilities based on their severity and potential impact.
Another important consideration is the scanners ease of use and integration with your existing IT systems.
Ideally, youll want a scanner that can be seamlessly integrated into your network and automated to run on a regular basis without requiring significant manual intervention.
This will help to ensure that your vulnerability scanning practices remain consistent and effective over time.
Finally, its important to choose a scanner that is backed by a reputable vendor with a strong track record in the security industry.
Look for a vendor that offers ongoing support and updates to ensure that your scanner remains up-to-date and effective against emerging threats.
By carefully considering these factors, you can choose a vulnerability scanner that meets your organizations unique needs and helps to keep your network secure.
4. Preparing for a Successful Vulnerability Scan.
Before conducting a vulnerability scan, it is crucial to prepare your network and systems to ensure a successful outcome.
The first step in preparing for a vulnerability scan is to identify all the assets that need to be scanned.
This includes servers, workstations, routers, switches, firewalls, and any other devices connected to the network.
Once you have identified all the assets, it is important to ensure that they are up-to-date with the latest security patches and updates.
Outdated software and operating systems can leave vulnerabilities that can be exploited by attackers.
Make sure to install all necessary updates before conducting the scan.
Another important aspect of preparation is to inform all relevant stakeholders about the upcoming scan.
This includes IT staff, system administrators, and business owners.
It is important to communicate the purpose and scope of the scan, as well as any potential disruptions that may occur during the process.
In addition, it is recommended to create a backup of all critical data and systems before conducting the scan.
This ensures that in case of any unforeseen issues, you can quickly restore your systems to their previous state.
Finally, it is important to set clear objectives for the vulnerability scan.
Determine what you want to achieve from the scan, such as identifying and addressing specific vulnerabilities or assessing overall network security.
Having clear objectives will help you focus your efforts and make the most out of the scan.
By following these steps, you can ensure that your vulnerability scan is conducted smoothly and effectively, providing valuable insights into your networks security posture.
5. Analyzing and Addressing Vulnerabilities Found.
Once the vulnerability scan is complete, its time to analyze and address the vulnerabilities found.
This step is crucial in ensuring that your network remains secure and protected from potential threats.
Firstly, prioritize the vulnerabilities based on their severity level.
Focus on addressing the high-risk vulnerabilities first, as they pose the greatest threat to your network.
Next, identify the root cause of each vulnerability and determine the best course of action to address it.
This may involve installing software patches, updating configurations, or implementing new security measures.
Its important to document all actions taken to address the vulnerabilities found during the scan.
This will help you keep track of your progress and ensure that no vulnerabilities are left unaddressed.
Finally, once all vulnerabilities have been addressed, conduct another vulnerability scan to ensure that all issues have been resolved.
Remember, vulnerability scanning is an ongoing process, and regular scans should be conducted to maintain a secure network.
By properly analyzing and addressing vulnerabilities found during a vulnerability scan, you can significantly reduce the risk of a security breach and protect your organizations sensitive data.
6. Maintaining Ongoing Vulnerability Scanning Practices.
Once you have executed a successful vulnerability scan and addressed the vulnerabilities found, it is important to maintain ongoing vulnerability scanning practices.
This means regularly conducting scans to ensure that your network remains secure and protected against potential threats.
Maintaining ongoing vulnerability scanning practices involves keeping your vulnerability scanner up-to-date with the latest security patches and updates.
It also means staying informed about new threats and vulnerabilities that may arise and adjusting your scanning practices accordingly.
Regularly reviewing and analyzing the results of your vulnerability scans can help you identify trends and patterns in your networks security posture.
This information can be used to make informed decisions about how to improve your networks security and prevent future vulnerabilities from occurring.
By maintaining ongoing vulnerability scanning practices, you can ensure that your network remains secure and protected against potential threats.
This not only helps to safeguard your organizations sensitive data and assets but also helps to build trust with your customers and stakeholders.
Video
A Step-by-Step Guide to Securing Your System:
Here is a video to show you how to register a community edition and install virutal appliance on your local network to execute internal scanning:







No comments:
Post a Comment