What isn’t as well known is why most enterprises need all three of these protocols to protect their email infrastructures. Like much in the IT world, the multiple solutions don’t all necessarily overlap. Actually, they are quite complementary to each other, and chances are good that the average business will need all three of them.
SPF
1 a policy framework as its name implies
2 an authentication method
3 specialized headers in the actual email itself that convey this information
Create or update your SPF TXT record
Ensure that you're familiar with the SPF syntax in the following table.
Element If you're using... Common for customers? Add this... 1 Any email system (required) Common. All SPF TXT records start with this value v=spf12 Exchange Online Common include:spf.protection.outlook.com3 Exchange Online dedicated only Not common ip4:23.103.224.0/19ip4:206.191.224.0/19ip4:40.103.0.0/16include:spf.protection.outlook.com4 Office 365 Germany, Microsoft Cloud Germany only Not common include:spf.protection.outlook.de5 Third-party email system Not common include:<domain_name><domain_name> is the domain of the third-party email system.
6 On-premises email system. For example, Exchange Online Protection plus another email system Not common Use one of these for each additional mail system: ip4:<IP_address>ip6:<IP_address>include:<domain_name><IP_address> and <domain_name> are the IP address and domain of the other email system that sends mail on behalf of your domain.
7 Any email system (required) Common. All SPF TXT records end with this value <enforcement rule>This can be one of several values. We recommend the value
-all.If you haven't already done so, form your SPF TXT record by using the syntax from the table.
For example, if you are hosted entirely in Office 365, that is, you have no on-premises mail servers, your SPF TXT record would include rows 1, 2, and 7 and would look like this:
textv=spf1 include:spf.protection.outlook.com -allThe example above is the most common SPF TXT record. This record works for just about everyone, regardless of whether your Microsoft datacenter is located in the United States, or in Europe (including Germany), or in another location.
However, if you bought Office 365 Germany, part of Microsoft Cloud Germany, you should use the include statement from line 4 instead of line 2. For example, if you are hosted entirely in Office 365 Germany, that is, you have no on-premises mail servers, your SPF TXT record would include rows 1, 4, and 7 and would look like this:
textv=spf1 include:spf.protection.outlook.de -allIf you're already deployed in Office 365 and have set up your SPF TXT records for your custom domain, and you're migrating to Office 365 Germany, you need to update your SPF TXT record. To do this, change
include:spf.protection.outlook.comtoinclude:spf.protection.outlook.de.Once you have formed your SPF TXT record, you need to update the record in DNS. You can only have one SPF TXT record for a domain. If an SPF TXT record exists, instead of adding a new record, you need to update the existing record. Go to Create DNS records for Office 365, and then select the link for your DNS host.
Test your SPF TXT record.
4 Verify your SPF configuration
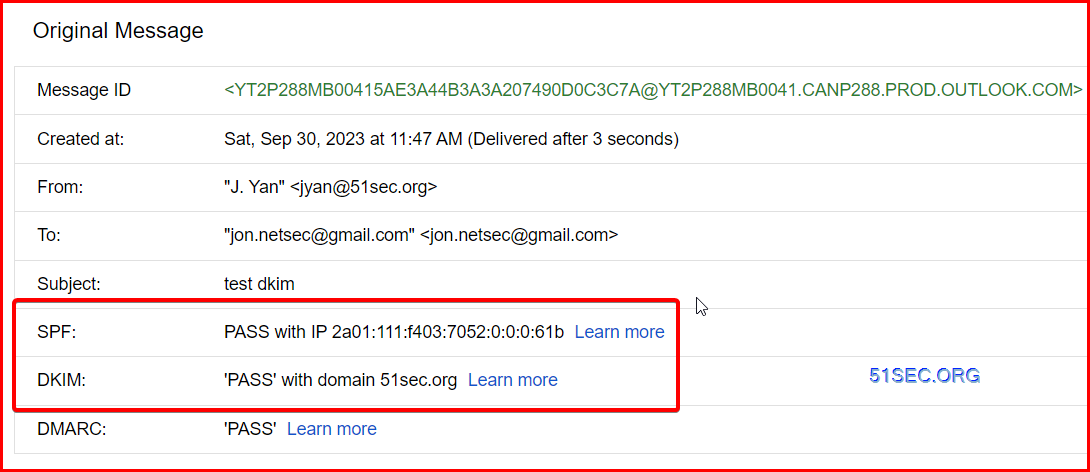
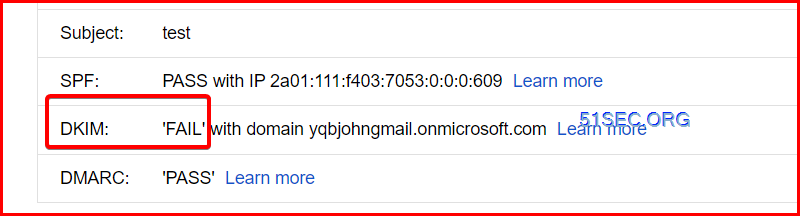
After enabled 51sec.org's DKIM in Office365 - Defender - Email & collaboration - Threat Policy - Authentication Settings - DKIM
You will see DKIM passed, SPF passed.
Refer: Set up SPF to help prevent spoofing
SPF was first proposed with IETF standard 4408 back in 2006, and has been updated most recently to standard 7208 in 2014.
An email message may contain multiple originator or sender addresses. These addresses are used for different purposes. For example, consider these addresses:
"Mail From" address: Identifies the sender and says where to send return notices if any problems occur with the delivery of the message (such as non-delivery notices). Mail From address appears in the envelope portion of an email message and isn't displayed by your email application, and is sometimes called the 5321.MailFrom address or the reverse-path address.
"From" address: The address displayed as the From address by your mail application. From address identifies the author of the email. That is, the mailbox of the person or system responsible for writing the message. The From address is sometimes called the 5322.From address.
SPF uses a DNS TXT record to list authorized sending IP addresses for a given domain. Normally, SPF checks are only performed against the 5321.MailFrom address. The 5322.From address isn't authenticated when you use SPF by itself, which allows for a scenario where a user gets a message that passed SPF checks but has a spoofed 5322.From sender address.
Limitations of SPF
SPF records don’t apply to the From address
Emails have multiple addresses to identify their sender: the From address that you normally see, and the Return Path address that’s hidden and require one or two clicks to view. With SPF enabled, the receiving email server looks at the Return Path and checks the SPF records of the domain from that address.
The problem here is that attackers can exploit this by using a fake domain in their Return Path address and a legitimate (or legitimate-looking) email address in the From section. Even if the receiver were to check the sender’s email ID, they’d see the From address first, and typically don’t bother to check the Return Path. In fact, most people aren’t even aware there is such a thing as Return Path address.
SPF can be quite easily circumvented by using this simple trick, and it leaves even domains secured with SPF largely vulnerable.
DKIM
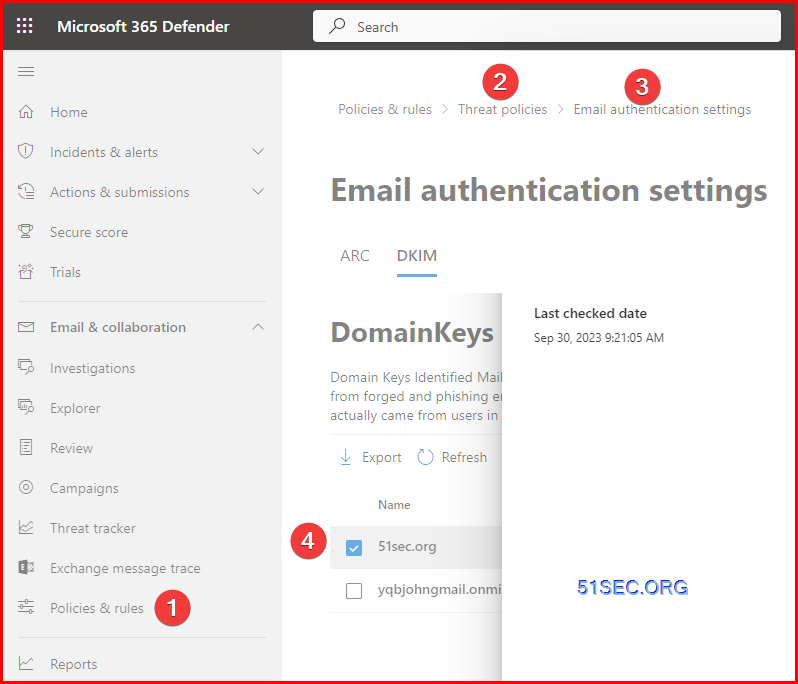
1 Go to Microsoft 365 Defender
2 Expand Email & Collaboration - Policies & rules
3 seclect Email Authentication settings - DKIM (DomainKeys Identified mail)
4 Choose your custome domain to enable DKIM.
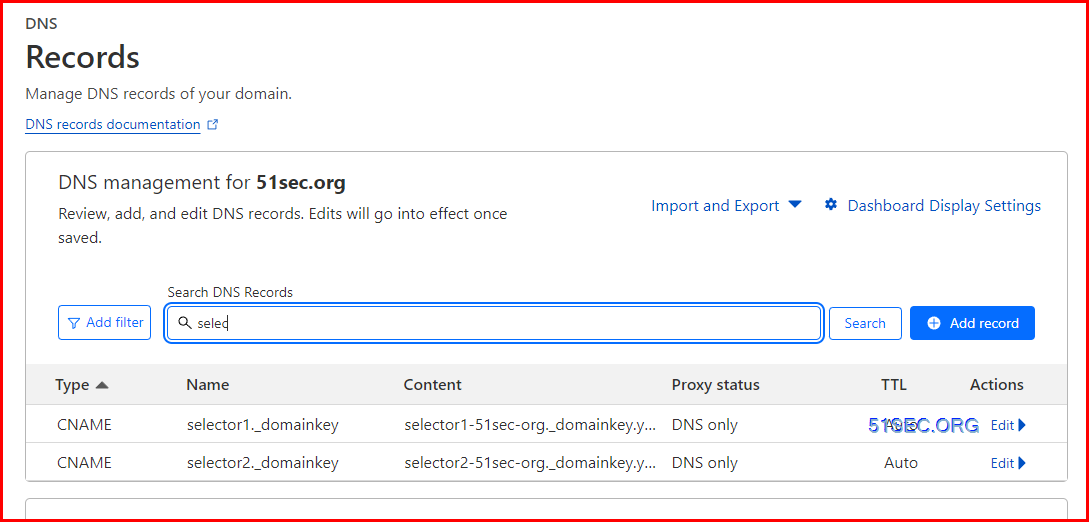
5 Add two cname records into your DNS administrtation site, such as Cloudflare
6 You might need to wait 10+ minutes for dns cname records taking into effect.
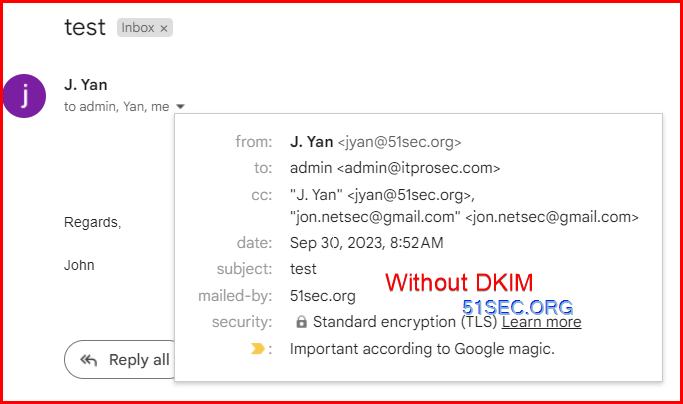
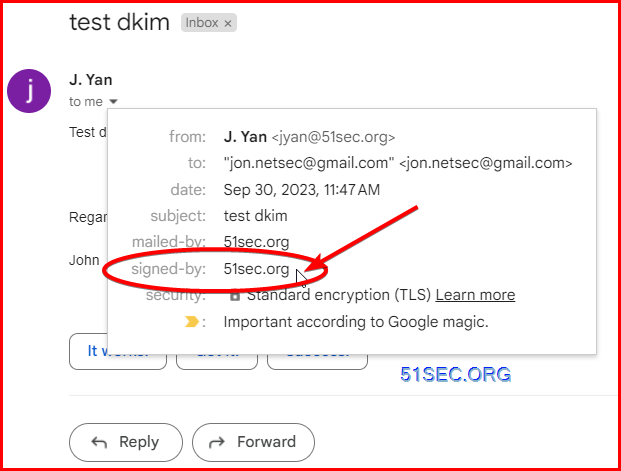
7 Test email without DKIM. You wont see the signed-by information.
If you have DKIM configured properly, you can test it by sending an email to your Gmail account. Then open your email in Gmail web mail, click "show details". If there is "signed-by: your domain", your DKIM signature is ok.
Delivered-To: [email protected]
Received: by 2002:a54:3f08:0:b0:231:65f5:b15b with SMTP id b8csp311128ecq;
Sat, 30 Sep 2023 05:52:12 -0700 (PDT)
X-Google-Smtp-Source: AGHT+IHdvkUJsAQ8/uwYcD60wgV+L7XMptrtch1OAr1Vpq/ae+gxZjU53W0KMeETaNFgZx8o3aCX
X-Received: by 2002:a19:650f:0:b0:4f8:6d9d:abe0 with SMTP id z15-20020a19650f000000b004f86d9dabe0mr5200756lfb.33.1696078332521;
Sat, 30 Sep 2023 05:52:12 -0700 (PDT)
ARC-Seal: i=2; a=rsa-sha256; t=1696078332; cv=pass;
d=google.com; s=arc-20160816;
b=BiIPadf61CnZxrjT8Zfzd4trGipbZWD6T65/p2avBa/iMVODZ/yXcL+muDYcRDOMTy
M/9jjKFFTJNngWT7xYlj/tJClZ7rpbMhltEPr1okzfKBic4Vvt+RJLGYhehP4ioM3N/H
aQDwRPtThdAK+J8FfgZLsozAb4jLDSIMFzem7kiIX0/W1ljkUsiCcQ/0ZTG/aYoEOV4S
xYRNppowdVDT7mhp7U+3mi4wbugtCWcMtj9F0X/uBb3E/mWA06IKv0EVT72Wzz1vaQSI
gXVm2OhQch6d5AhYVuZJbB9vRQ79mzvU49CrgbEU+Y7kvI04fDBvaSVgQeTdl8h6pfib
620A==
ARC-Message-Signature: i=2; a=rsa-sha256; c=relaxed/relaxed; d=google.com; s=arc-20160816;
h=mime-version:content-language:accept-language:message-id:date
:thread-index:thread-topic:subject:cc:to:from:dkim-signature;
bh=TR6VUALzsQCDl9oUUfSfhTnrwTeM8g6kMrYE1dUiMis=;
fh=W6bUczERNO+qEYfh1Yr3RvOPqcdoEOzGlPax467iG8w=;
b=opLGxxbhS+8teUXcomvw128ZJdXzDrjko+gqUrWpp8Xei+P0kSNKnyvERsi/fNwDRc
DXxph4IHa9p3gv62AsvlhKuwu2Pig+pf7WQCBuqwjd5znPU3hrQq8BLJIIpa/O3hKmRN
0rT8hB+ChK7eQmzIX7UfAmsAMwLI+ZYD/WOlwFSM0FDlXFcQ6tqD81t83B19/+6xxwfa
TJiTIAAva/BMkCynG00ehv2j0wPZVs87a7Tb05fBwnjgWWVOCUtJIdxx7usCM8PdkYzv
ugGeR7grl7VdmAm4SuVkudP87E3CvkJZ7EUo3WXopBSzYXnW3jxAkeKvUxseWj5ugroO
fSfg==
ARC-Authentication-Results: i=2; mx.google.com;
dkim=temperror (no key for signature) [email protected] header.s=selector1-yqbjohngmail-onmicrosoft-com header.b=cEdJu6Jj;
arc=pass (i=1 spf=pass spfdomain=51sec.org dkim=pass dkdomain=51sec.org dmarc=pass fromdomain=51sec.org);
spf=pass (google.com: domain of [email protected] designates 2a01:111:f403:7053::609 as permitted sender) [email protected];
dmarc=pass (p=QUARANTINE sp=QUARANTINE dis=NONE) header.from=51sec.org
Return-Path: <[email protected]>
Received: from CAN01-YT3-obe.outbound.protection.outlook.com (mail-yt3can01on20609.outbound.protection.outlook.com. [2a01:111:f403:7053::609])
by mx.google.com with ESMTPS id w25-20020a05651204d900b0050296fffebasi9364656lfq.114.2023.09.30.05.52.12
for <[email protected]>
(version=TLS1_2 cipher=ECDHE-ECDSA-AES128-GCM-SHA256 bits=128/128);
Sat, 30 Sep 2023 05:52:12 -0700 (PDT)
Received-SPF: pass (google.com: domain of [email protected]g designates 2a01:111:f403:7053::609 as permitted sender) client-ip=2a01:111:f403:7053::609;
Authentication-Results: mx.google.com;
dkim=temperror (no key for signature) [email protected] header.s=selector1-yqbjohngmail-onmicrosoft-com header.b=cEdJu6Jj;
arc=pass (i=1 spf=pass spfdomain=51sec.org dkim=pass dkdomain=51sec.org dmarc=pass fromdomain=51sec.org);
spf=pass (google.com: domain of [email protected] designates 2a01:111:f403:7053::609 as permitted sender) [email protected];
dmarc=pass (p=QUARANTINE sp=QUARANTINE dis=NONE) header.from=51sec.org
ARC-Seal: i=1; a=rsa-sha256; s=arcselector9901; d=microsoft.com; cv=none; b=bLTkG9U+g4cav0Yc9dNE4sqji8R0kh1c9vf1+SYKInfCV1nkOZEEWKiDv6mNyV1ydqIo+XkAFnotGS/KJRygSzQTFy5sl+ISoCU4IEJ8EMq5+GHajC5eiAgWoHxu+kv2748A7EnYyaZmGLobcmAW8ABfFOR+tfMOCj9HwgOPpv5H2c0TAuUj40oiU1gRYNrBvRPw3GJ15+v0PxjqTid8u7MmUXHpH0f3cB4+FiDYznVvPEY2xlGjdobf/eKgQjOS14ZvVC+Zvsnp/fyvcUi2AD6X65gqNcG+NUd3XZvx5sAQrG56YHfVEKwcoEravW5vqbavtR4jbB6mW6VzsTxCnw==
ARC-Message-Signature: i=1; a=rsa-sha256; c=relaxed/relaxed; d=microsoft.com; s=arcselector9901; h=From:Date:Subject:Message-ID:Content-Type:MIME-Version:X-MS-Exchange-AntiSpam-MessageData-ChunkCount:X-MS-Exchange-AntiSpam-MessageData-0:X-MS-Exchange-AntiSpam-MessageData-1; bh=TR6VUALzsQCDl9oUUfSfhTnrwTeM8g6kMrYE1dUiMis=; b=QU+PMbjsSL/SrICi/FA1E+vUoxNGOTlF60TPL5TUrj9xYIixaZlSeUdgX9HPWPecNkE5uvhNOv4Gzv6gqMIVD3d1uOoQQ1o/tA4ldQZPHX//YNIZKA7kLczla78Sd1CH/5TeFdflu8Im6njfIsQs7c9rn4qprtFG7PQT/otuBL4HBL8cPtnvvwCCKbACqdDXBDOEkiB62H30pZbl+VcNeMXv5VPh3QV1KKArgPiVSumVwfflySJ/7MHzycsY7Z5n60c6+wsgmkObXezHOg4jbntOR2EmdEaZ5WQFekNkyxDm+EWmIce4H0e85DIZ5PVI/P4OB4evTCy6fZyNh/OO9Q==
ARC-Authentication-Results: i=1; mx.microsoft.com 1; spf=pass smtp.mailfrom=51sec.org; dmarc=pass action=none header.from=51sec.org; dkim=pass header.d=51sec.org; arc=none
DKIM-Signature: v=1; a=rsa-sha256; c=relaxed/relaxed; d=yqbjohngmail.onmicrosoft.com; s=selector1-yqbjohngmail-onmicrosoft-com; h=From:Date:Subject:Message-ID:Content-Type:MIME-Version:X-MS-Exchange-SenderADCheck; bh=TR6VUALzsQCDl9oUUfSfhTnrwTeM8g6kMrYE1dUiMis=; b=cEdJu6JjFZJYdO4ZdzE9CCd9ntjOQnPfxVBQwrrDIefHHU4aCq6hpHAEHVKRScxc3MMUs2WZJaq1AT8hMgnRNu4sk7q5Cz2Ow4dhGMpY6KfOWAlEDOmXKAXj4si7xdBD72F5BqfEmSS4jkzwoIACidBbsF+AZZ90eTHvlRr/5TU=
Received: from YT2P288MB0041.CANP288.PROD.OUTLOOK.COM (2603:10b6:b01:f6::19) by YT3P288MB0127.CANP288.PROD.OUTLOOK.COM (2603:10b6:b01:fb::11) with Microsoft SMTP Server (version=TLS1_2, cipher=TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384) id 15.20.6838.28; Sat, 30 Sep 2023 12:52:10 +0000
Received: from YT2P288MB0041.CANP288.PROD.OUTLOOK.COM ([fe80::861b:5d98:2623:62ec]) by YT2P288MB0041.CANP288.PROD.OUTLOOK.COM ([fe80::861b:5d98:2623:62ec%4]) with mapi id 15.20.6838.029; Sat, 30 Sep 2023 12:52:10 +0000
From: "J. Yan" <[email protected]>
To: admin <[email protected]>
CC: "J. Yan" <[email protected]>, "[email protected]" <[email protected]>
Subject: test
Thread-Topic: test
Thread-Index: AdnznOZEGrbpXiabQ6SRy1zEfg/d6A==
Date: Sat, 30 Sep 2023 12:52:10 +0000
Message-ID: <YT2P288MB004161575CF9AA9259F1C8DEC3C7A@YT2P288MB0041.CANP288.PROD.OUTLOOK.COM>
Accept-Language: en-CA, en-US
Content-Language: en-US
X-MS-Has-Attach:
X-MS-TNEF-Correlator:
authentication-results: dkim=none (message not signed) header.d=none;dmarc=none action=none header.from=51sec.org;
x-ms-publictraffictype: Email
x-ms-traffictypediagnostic: YT2P288MB0041:EE_|YT3P288MB0127:EE_
x-ms-office365-filtering-correlation-id: 37f4deee-5690-4cab-6a79-08dbc1b40fa4
x-ms-exchange-senderadcheck: 1
x-ms-exchange-antispam-relay: 0
x-microsoft-antispam: BCL:0;
x-microsoft-antispam-message-info: iCXKriAJgXncUHcL1za25S/mDtX2jgSxzaHPrRrI4VpHG6pl8IjDNiednu/vweAkEogBYXPmYtvZjmaVcQyEFU4cEH7JjpIqNOC1Nr20CjuiGq4fCMd+mfLzvBe38/7pYXDkkgbCzQiHNsJ4OqkCaaQBVuHpvSZBXzVDfZ4bx0vhxdahdQR60EuvVugou2BUpT9IK+ppgTyf//cF20wy6R3e8HEwUnuybdOFMQlmaWyUkY2tIYL36w4q9Rcw0n9bX5fL9n3+IdemVfhetuTyL96HT1aw1IMRj/uOk8U6lnijJXpHbMrwzOddMgfg/TXl3QNbFB/8hCWfgJxiE/LD3ECrN/nqQMjV2nj0PAQwV5Rnrja4LN0t6sQoErnZR9CQY/vWZ8OH/w5aeARXfVXNlyGtTlegazqx2xRNEVWwawC8f/9Y84EfBrAes3ZYunPDGGNIrFKcIjk4hmV7yGS3gD7n/FmQAREH9eMv1mcfDDj/GQBeyn0OIyrIdbc6LCDllfLoVTJucssny50CfOu0zLw6OkBs1XlLvnwowkEOpRNgYylvE61tlan6hdrY9h7BDeP1jZ75TcEUfvCBumclDnW3DvMSmlf7TUMA/4/uZyLinBKm31rp8VgzP7SnTMXJWwCxC9a/WUQBhJsDBQ8JyQ==
x-forefront-antispam-report: CIP:255.255.255.255;CTRY:;LANG:en;SCL:1;SRV:;IPV:NLI;SFV:NSPM;H:YT2P288MB0041.CANP288.PROD.OUTLOOK.COM;PTR:;CAT:NONE;SFS:(13230031)(136003)(396003)(346002)(39830400003)(376002)(366004)(230922051799003)(64100799003)(1800799009)(451199024)(186009)(33656002)(558084003)(86362001)(55016003)(26005)(4270600006)(2906002)(122000001)(9686003)(7696005)(6506007)(71200400001)(478600001)(52536014)(4326008)(8936002)(7116003)(8676002)(41300700001)(38100700002)(38070700005)(64756008)(54906003)(5660300002)(3480700007)(316002)(66446008)(6916009)(66556008)(76116006)(66946007)(66476007)(220243001);DIR:OUT;SFP:1101;
x-ms-exchange-antispam-messagedata-chunkcount: 1
x-ms-exchange-antispam-messagedata-0: c1rgyCSjGUK+llZ4H4diLW+FjBFvADhWg/nWBf92es7/kbsVRoQ8pWPpL4fgUUnZX17mdbWrxK05BgoHMkV3j6zctP1NYe14DOYNC5h2B3zen+bYLPqkRi47SupfxDZOvpXJqD9HWaOA0kCCMEL5GaQ264kVTK0m9AYL+DWXES2dFKInL0uIjz09oT5hTIpAqTF6dwMN6m7omqhRaqpfHmJ3N/VdO5qaDZYBYiTC57skmCWSxu7CHegxcYkSuzGQKafPCqgCnS3b+lH6b6mh6LxfnMrZU8g/vQatBQk6MAyTHV9TDIh6N/iCJ0S4g7KhlUMujL6cpzow+ABUD43E+OZoqHLYts7rBgtKUWCH1If5RDIVIdSJPwrbX18s81vrppAySVVca5dcTTvF9z4EfQ+pS0RLzBMaYgTLwvldHtpC4gn50/CoqO2lYQyt5+Oj8z+3iGLGvHQkef8+JJ02ZgmGG2ZchU4DgMgHhlZppa3ej2/NMa9J5998fqxmuWYoaL8ggIMUmLy45ZFh90TONxI1lu2ltWtKapfW3V6pkRb5FuAe35kvSXUtWr3fD9GvfZOXz4/mJkDLG6axhsBDmZg20OVjwN0L79+xYa5mOsMEfqGTwyadgggsOtG69pVxW4hawje96mstSZ8Fz0oSObXZ/zukjlxcRL9okfhQPyjGX/Beca0XiEt9lO+Zw39goj377AVcG3YMS/dL3mP0XyHhsJxeVQ3p5hmQyl/VaVSJ79oxMg2DVqDmyZq42BGY/bWnQ5i8gADC1cNSEOezYHFHYcFNGiFL+/XQZaYTgBWrw6rHy1N0x+H7+VSxagTPO7k//zbEqZwhNeZNwq+zF1QpCY7HsEdUut4nlGsEGCocBuhUaEqjWWShDje1okIcDP47Cta14SgPxzjuHFSbcl4JPsP9KLNSWLD0yX6mAm+q16M0j9EcRRYYXnmn08XX0USWdY1q2KrNC+zoKDsCbU4BHIz+YYPxllp0OOqc+ilRvphjLjOhLqKjmwR2hdCgry5FX8FGMqKQOCedentRr4NPvXgaduyk+0P2fWeFtYjTbfv07jnn4O9uR9eUZMUbVVXNQmSFWoHHW89yyelNduA4W9ODB3Ngqt8bC7744oOP7KKJH6CsUvo1rNBWumgtl/Oc5/2AeZqh04n7WNo1gDcMgA2kbxzkPCSm9VL1dWfMdIBylZWt/ggEEqID+qS3eFj/AL+C5wh8VyHNKPm6nyNFlNdlUk1Af/a52w1hNHMHY2NpogyQ27SrjL0TIu5BReafP5lvogdYwO1FvGsPV2GblFW/57vuBouT4j7UOl6YpHZJQsQp3Q+P3DrKrCpXiNuASZWfXmYFT0/lBtXzkcHlOU+RhmwMU8qxWa/r2VPt90bX4goikZXKxPSr1bSUNh2QWH1r1KyYdYH6vACl1DsuwzRp4cquU5ZpxtkOwhWjD/UkruhKIzDd6QgLq3AMuY4gdHdbe/Q+wlhSoIPa0Ul8tn10kB23UReBdeiGXkvGDeKV2cTucF3lrAP+P22Q+JYQUh5+ECPezyg6A1YNu5iVLcmO1PBGNi0TyUxXr2k=
Content-Type: multipart/alternative; boundary="_000_YT2P288MB004161575CF9AA9259F1C8DEC3C7AYT2P288MB0041CANP_"
MIME-Version: 1.0
X-OriginatorOrg: 51sec.org
X-MS-Exchange-CrossTenant-AuthAs: Internal
X-MS-Exchange-CrossTenant-AuthSource: YT2P288MB0041.CANP288.PROD.OUTLOOK.COM
X-MS-Exchange-CrossTenant-Network-Message-Id: 37f4deee-5690-4cab-6a79-08dbc1b40fa4
X-MS-Exchange-CrossTenant-originalarrivaltime: 30 Sep 2023 12:52:10.3696 (UTC)
X-MS-Exchange-CrossTenant-fromentityheader: Hosted
X-MS-Exchange-CrossTenant-id: b7a98d75-076f-43b1-bfdb-c99217221d23
X-MS-Exchange-CrossTenant-mailboxtype: HOSTED
X-MS-Exchange-CrossTenant-userprincipalname: flw+XaG3ytoAAKXPub0SeGZ3j3Dk2N9uKTH4R302sma39V+YN38Qml7osYMuBqAZ
X-MS-Exchange-Transport-CrossTenantHeadersStamped: YT3P288MB0127
--_000_YT2P288MB004161575CF9AA9259F1C8DEC3C7AYT2P288MB0041CANP_
Content-Type: text/plain; charset="us-ascii"
Content-Transfer-Encoding: quoted-printable
Regards,
John
--_000_YT2P288MB004161575CF9AA9259F1C8DEC3C7AYT2P288MB0041CANP_
Content-Type: text/html; charset="us-ascii"
Content-Transfer-Encoding: quoted-printable
<html xmlns:v=3D"urn:schemas-microsoft-com:vml" xmlns:o=3D"urn:schemas-micr=
osoft-com:office:office" xmlns:w=3D"urn:schemas-microsoft-com:office:word" =
xmlns:m=3D"http://schemas.microsoft.com/office/2004/12/omml" xmlns=3D"http:=
//www.w3.org/TR/REC-html40">
<head>
<meta http-equiv=3D"Content-Type" content=3D"text/html; charset=3Dus-ascii"=
>
<meta name=3D"Generator" content=3D"Microsoft Word 15 (filtered medium)">
<style><!--
/* Font Definitions */
@font-face
=09{font-family:"Cambria Math";
=09panose-1:2 4 5 3 5 4 6 3 2 4;}
@font-face
=09{font-family:\7B49\7EBF;
=09panose-1:2 1 6 0 3 1 1 1 1 1;}
@font-face
=09{font-family:Calibri;
=09panose-1:2 15 5 2 2 2 4 3 2 4;}
@font-face
=09{font-family:"\@\7B49\7EBF";
=09panose-1:2 1 6 0 3 1 1 1 1 1;}
/* Style Definitions */
p.MsoNormal, li.MsoNormal, div.MsoNormal
=09{margin:0in;
=09font-size:11.0pt;
=09font-family:"Calibri",sans-serif;
=09mso-ligatures:standardcontextual;}
span.EmailStyle17
=09{mso-style-type:personal-compose;
=09font-family:"Calibri",sans-serif;
=09color:windowtext;}
.MsoChpDefault
=09{mso-style-type:export-only;
=09font-family:"Calibri",sans-serif;}
@page WordSection1
=09{size:8.5in 11.0in;
=09margin:1.0in 1.25in 1.0in 1.25in;}
div.WordSection1
=09{page:WordSection1;}
--></style><!--[if gte mso 9]><xml>
<o:shapedefaults v:ext=3D"edit" spidmax=3D"1026" />
</xml><![endif]--><!--[if gte mso 9]><xml>
<o:shapelayout v:ext=3D"edit">
<o:idmap v:ext=3D"edit" data=3D"1" />
</o:shapelayout></xml><![endif]-->
</head>
<body lang=3D"EN-US" link=3D"#0563C1" vlink=3D"#954F72" style=3D"word-wrap:=
break-word">
<div class=3D"WordSection1">
<p class=3D"MsoNormal"><o:p> </o:p></p>
<p class=3D"MsoNormal"><o:p> </o:p></p>
<p class=3D"MsoNormal"><o:p> </o:p></p>
<p class=3D"MsoNormal"><o:p> </o:p></p>
<p class=3D"MsoNormal">Regards,<o:p></o:p></p>
<p class=3D"MsoNormal"><o:p> </o:p></p>
<p class=3D"MsoNormal">John<o:p></o:p></p>
<p class=3D"MsoNormal"><o:p> </o:p></p>
</div>
</body>
</html>
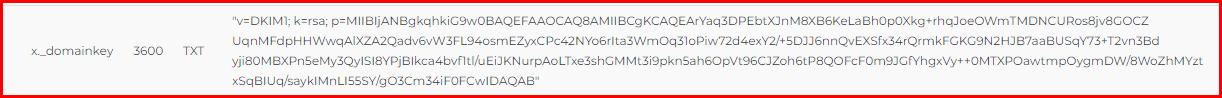
--_000_YT2P288MB004161575CF9AA9259F1C8DEC3C7AYT2P288MB0041CANP_--DKIM is one of the trio of Authentication methods (SPF, DKIM and DMARC) that help prevent attackers from sending messages that look like they come from your domain.
DKIM lets you add a digital signature to outbound email messages in the message header. When you configure DKIM, you authorize your domain to associate, or sign, its name to an email message using cryptographic authentication. Email systems that get email from your domain can use this digital signature to help verify whether incoming email is legitimate.
In basic, a private key encrypts the header in a domain's outgoing email. The public key is published in the domain's DNS records, and receiving servers can use that key to decode the signature. DKIM verification helps the receiving servers confirm the mail is really coming from your domain and not someone spoofing your domain.
Tip
You can choose to do nothing about DKIM for your custom domain too. If you don't set up DKIM for your custom domain, Microsoft 365 creates a private and public key pair, enables DKIM signing, and then configures the Microsoft 365 default policy for your custom domain.
Microsoft-365's built-in DKIM configuration is sufficient coverage for most customers. However, you should manually configure DKIM for your custom domain in the following circumstances:
- You have more than one custom domain in Microsoft 365
- You're going to set up DMARC too (recommended)
- You want control over your private key
- You want to customize your CNAME records
- You want to set up DKIM keys for email originating out of a third-party domain, for example, if you use a third-party bulk mailer.
DMARC
1 Proofpoint has a free interactive tool to create your DMARC record here.
2 https://mxtoolbox.com/dmarc/details/dmarc-tags
3 DMARC Report : Manage and monitor your DMARC configuration and reports
Policy set to none
Console_dmarc.contoso.com 3600 IN TXT "v=DMARC1; p=none"Policy set to quarantine
Console_dmarc.contoso.com 3600 IN TXT "v=DMARC1; p=quarantine"Policy set to reject
Console_dmarc.contoso.com 3600 IN TXT "v=DMARC1; p=reject"
Once you've formed your record, you need to update the record at your domain registrar.
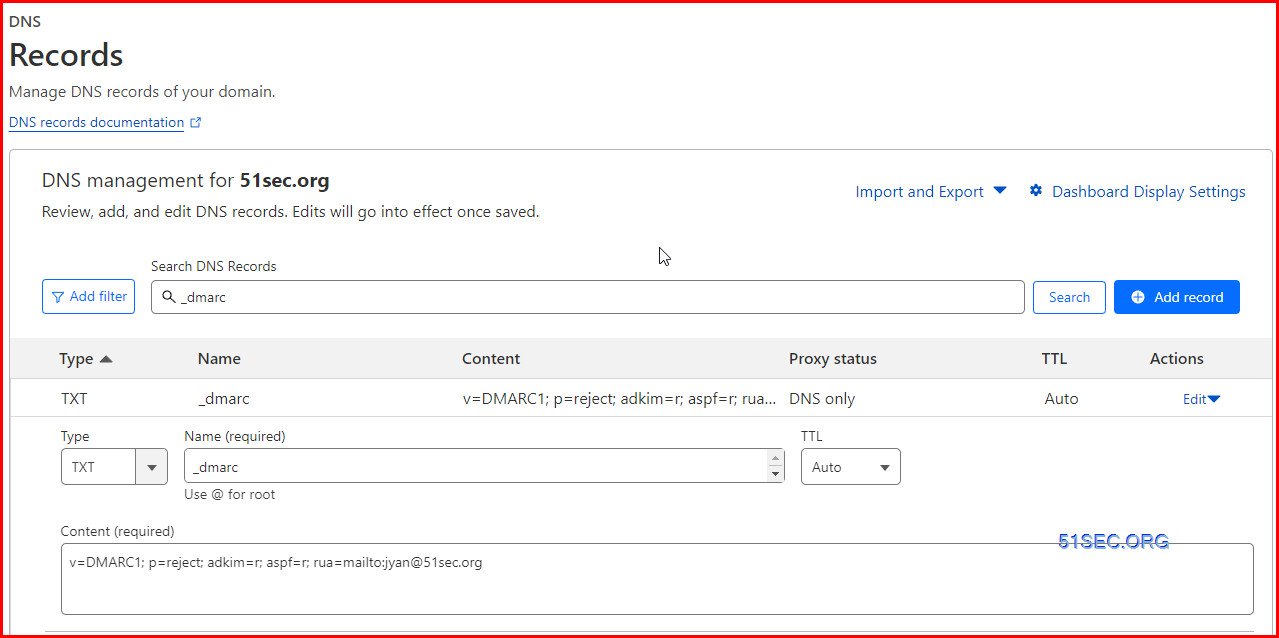
DMARC configuration
- TXT _dmarc v=DMARC1; p=reject; adkim=r; aspf=r; rua=mailto:[email protected]







No comments:
Post a Comment